By Christian Have, LogPoint CTO
LogPoint’s mission is about “creating the best SIEM in the world,” where “creating” is an explicit reference to our mantra of accelerating detection and response. Throughout the past year and in the coming years, we are helping companies detect and respond faster than ever before. Looking ahead, we’ll see that without a proper security foundation, even the best tools won’t help companies detect or respond faster.
Looking back at 2020
In 2020, we published many articles highlighting how to detect malware and malicious activity in networks. We also launched several product features and enhancements, including increased UEBA source coverage, increased detection capabilities for the cloud and support for the MITRE ATT&CK framework (and ported the entire detection catalog to the ATT&CK taxonomy).
In addition to product features and articles, we expanded our customer success team in LogPoint. The team helps speed up customer adoption of new capabilities by guiding customers and providing more content, such as device configuration and documentation for incorporating MITRE. When our customers are using the latest capabilities, they can detect and respond to attacks quickly.
Using the latest security enhancements to shield against outside attacks remains essential. As the NSA mentions in the NSA Cybersecurity 2020 year in review, many actors are willing and able to launch disruptive cyber operations on critical infrastructure, disinformation warfare and steal intellectual property to further their economies and militaries. Breaking this down further, the 2020 Verizon Data Breach Investigations Report finds that external actors perpetrate 70% of attacks, and of all attacks, 86% are financially motivated.
No matter which threat actor your threat model identifies as the most pressing, accelerating detection and response holds. Accelerating is the keystone. We see an improvement with our customers to detect and contain breaches. Whether a result of the numerous high-profile and high-impact ransomware attacks, increased regulatory focus, or the fact that more customers seek the expertise and detection capability of MSSPs, the trend remains – detection and response timelines are decreasing.
Heading into 2021
In our R&D team, we are working to solve the time-consuming steps and challenges associated with triage and understanding what evidence relates to a given incident. Similarly, we are engineering an analytics fabric that spans different detection and analysis capabilities to coalesce and condense observations, alerts and incidents. We will introduce these capabilities throughout 2021 and 2022. Taking a step out of the R&D bubble and looking at where our users are moving, we anticipate several trends.
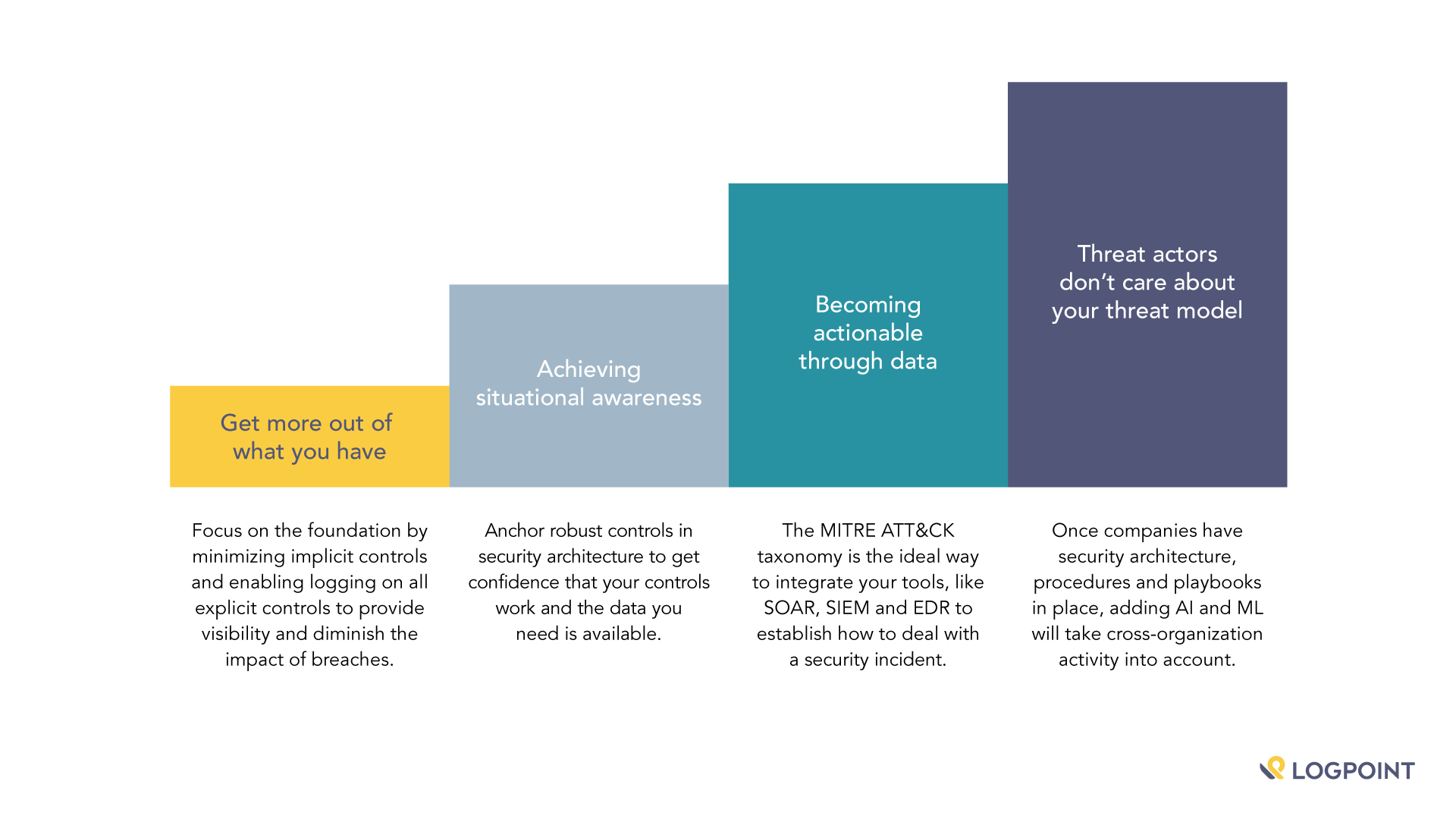
Getting more out of what you have
Let’s start by defining a razor in cybersecurity: The least sexy solution to a complex problem is often the most impactful. Adding more security technology can add complexity and doesn’t equate to a safer system. As trivial as mandatory access control (MAC) may sound, Zero Trust is experiencing a revival as rebranded MAC, and for good reason. Managing the flow of information by ensuring that packets cannot traverse security zones in the network without going through a firewall or a content inspection product or ensuring that execution flows are understood is a foundational yet underutilized set of concepts.
Getting rid of implicit controls and enforcing explicit controls of network packets and explicit behaviors of operating systems or applications substantially diminishes the likelihood or impact of breaches. Enabling logging on explicit controls provides the visibility of what happens. It allows performance monitoring of the efficacy of the security architecture as a whole and the specific control in detail.
Bottom line: We expect more organizations to take a hard look at their existing architecture. Rather than implement a lot of new technology, they’ll find ways to adopt simple measures that limit breaches’ impact.
Achieving situational awareness
When an alert fires, you commence triage as a security analyst: Does it need immediate action, urgent action or delayed action?
To effectively manage an alert, you have to have confidence in the infrastructure, the device responsible for the alert firing, and that data is available. Essentially, you need to know that your controls work and the data you need is available.
Suppose you have your security razor in place. In that case, you won’t have to worry much about false positives because the controls are explicit, and the network traffic terminates on proxies or firewalls. What do you need to deliver effective triage?
You might ask yourself questions such as:
- What risk model are we dealing with?
- What risk group does our device, log source, log message, user group, ATT&CK technique ID belong to?
- Pro-tip: In LogPoint, you would deploy static and dynamic lists and cross-reference these as part of the alert creation, automatically
- Do you have the right supporting evidence to make a judgment call?
- Did UEBA flag a user or network-entity associated with the alert as malicious?
- How often has this alert triggered before?
- For this user?
- For this IP?
- What other alerts triggered for this user, or user or system?
- Did your MISP or STIX threat intel feed flag any associated log message?
- Did your Windows infrastructure use Sysmon and a curated config?
- Is the involved system behind on security updates?
- Did your Malware Sandbox, EDR or XDR provide supporting evidence?
- What risk group does our device, log source, log message, user group, ATT&CK technique ID belong to?
After answering these questions, it becomes evident that technology alone can’t solve everything. You need to have your security foundation in order first.
Bottom line: Robust controls anchored in a security architecture framework will free up analysts’ time to focus on what’s essential: risk models and gathering supporting evidence to triage effectively.
Becoming actionable through data
Gathering telemetry from systems, consuming TI feeds, enriching data with contextual information from CMDBs, AD, vulnerability management and user/entity behavioral scoring are essential steps toward dealing with a security incident.
Deciding on actions and, in turn, what type of playbook or what type of escalation and organizational procedure to invoke is vital. It’s crucial to ensure the proper attention and priority is assigned, and it’s equally essential to ensure classification and remediation is appropriate.
Analysts must consider several factors for the response and remediation:
- How severe is the impact at the current stage of the breach?
- Is fine-grained containment a feasible approach at this stage?
- If using Zero Trust, service compartmentalization and micro-segmentation, is it possible to contain the breach while allowing most of the infrastructure to remain operational?
- With the current understanding of detection and control coverage, with a knowledge of TTPs used by the threat actor and by understanding the risk appetite, what is the chance of potentially focusing the response too narrowly?
- Are people, processes and technology available and tested to automate and orchestrate?
- With the event data, contextual data, threat actor data and situational awareness in place is the organization prepared and ready to potentially lock hundreds of accounts, isolate systems on the network, validate the integrity of operating systems and applications and in a controlled fashion, begin the controlled return to normal operations?
The adoption of security orchestration and automation (SOAR) tools is looking promising. SOAR helps security teams automate repetitive tasks at scale, orchestrate sequences of automated tasks and respond via rules and feedback loops to inputs from SIEM and EDR/NDR tools. With the MITRE ATT&CK framework, a taxonomy of threat actor behavior allows disparate technologies to exchange information about TTPs and telemetry. We see the MITRE ATT&CK taxonomy as a way to integrate SIEM, SOAR, EDR, NDR, Sandbox and IAM tools via open and well-defined APIs.
Bottom line: To achieve security automation or orchestration capabilities, security teams must finely tune the security architecture and controls, or else run the risk that systems either miss or act insufficiently to manage the breach, leading to a false sense of security for the teams relying on these capabilities.
Threat actors don’t care about your threat model or organizational red tape
Attackers navigate a graph, and defenders navigate point solutions. A threat actor will take the easiest way to a target, expending as few of the juicy tricks as possible and generating as little noise as possible. Threat actors will have many ways of reaching the goal or objective. Therefore a company’s return on security technology investment diminishes relatively quickly.
For example, if your organization procures an EDR platform, your threat actor will attack via your ERP platform. Essentially, as the number of security controls increases, the complexity, costs and expanded attack surface of these new controls increases as well, resulting in a net-change in security that approaches zero.
We also see point solutions such as Zero Trust for both SAP and cloud. While Zero Trust for SAP and cloud will have value for companies with playbooks in order, procedures for triage and basic security architecture principles in place – there could be better places to invest and get end-to-end visibility.
Continuous monitoring across cloud deployments, ERP and CRM platforms and business applications with domain-specific detection, ATT&CK-mapped alerting and coalesced incident management would be a better choice for most organizations than applying point solutions. By joining the data from these applications and applying the ML and AI capabilities of a SIEM, with UEBA and SOAR, not only will organizations be able to use, for instance, UEBA on the data from the ERP system, but also build a detection-graph that takes network, endpoint and application activity into account.
Bottom line: The attack graph is real, and point solutions add more complexity than net security increases unless the foundation and architecture are firmly defined and followed.
In conclusion: Expect your tools to help, but you are still in the drivers’ seat.
In 2021 the industry will present automation and orchestration of incidents as a panacea. Automation and orchestration are relevant, and we see more and more vendors adding these capabilities to existing and new products. To accelerate detection and response even further, we see that these products will claim to use ML and AI to reduce the analyst’s workload.
Looking at where critical decisions are made during triage and response and looking at how detection takes place, AI and ML have a place, and so does automation. But most important is the foundation. Security teams need confidence that situational awareness is complete, with contextual information that the controls and assumptions made during remediation target the TTPs correctly.
For us at LogPoint, we are building capabilities to precisely uncover how the attacker navigates the path of least resistance. We’re providing visibility no matter where that path takes the attack with detection and investigation at every step. That’s what we call accelerated detection and response.