Logpoint and MITRE ATT&CK framework
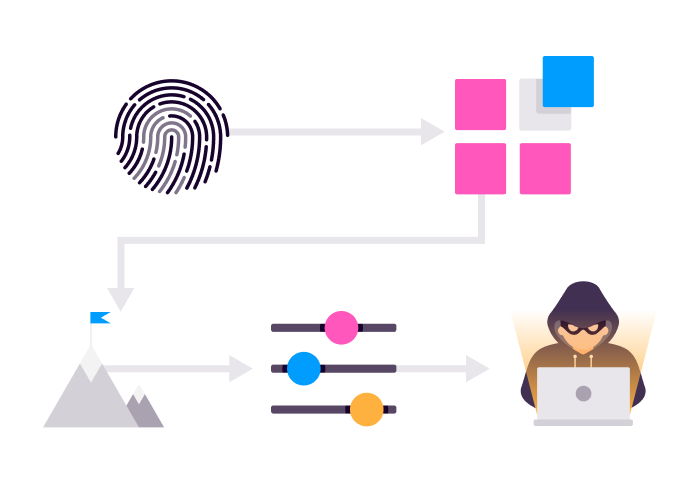
Automatically add context. Transform weak alerts into meaningful investigations, providing analysts orchestration and automation actions at their fingertips to respond faster than ever.
MITRE is a non-profit organization focused on cybersecurity and solving security challenges to create a safer IT environment for organizations. MITRE developed the ATT&CK framework to classify adversarial tactics universally. ATT&CK is also a database that organizations can use to reference and document threat behaviors across the entire attack lifecycle.
MITRE ATT&CK tactics and techniques
The ATT&CK model assigns a unique ID to every adversarial tactic used within the typical process of an intrusion. The tactics help verify the existence of an intrusion, the type of intrusion and a prediction of what will happen next. Security teams can use the tactics when monitoring and responding to incidents.
The tactics are not concrete technologies or actions, but instead, they are conceptual, which means ATT&CK can be used to classify new techniques. Security teams can use ATT&CK for threat intelligence and reporting for a faster, more flexible and more informed approach to cybersecurity.
Situational awareness of your entire infrastructure
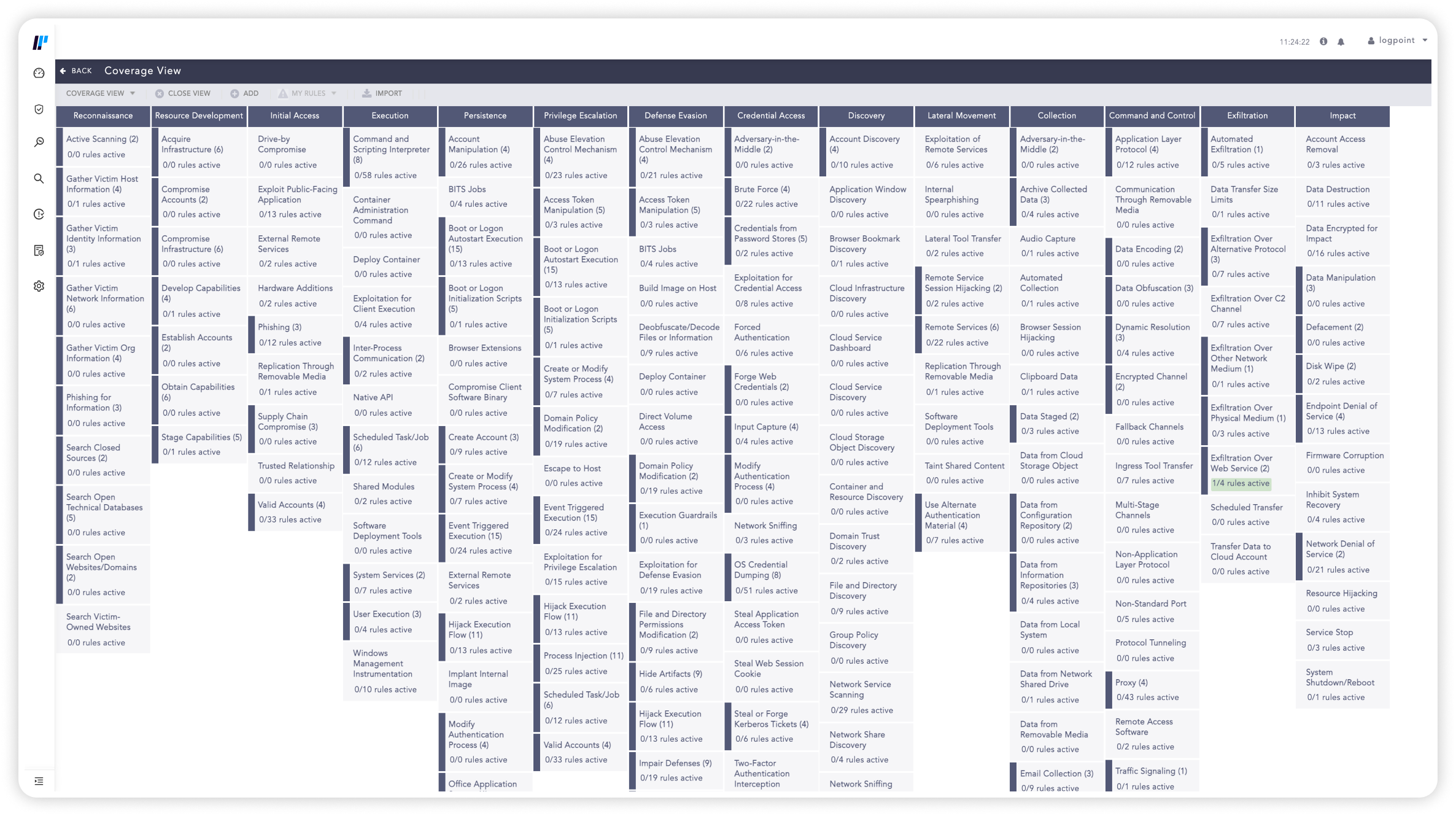
All the security functionality in Logpoint SIEM and all alerts in UEBA are based on the MITRE ATT&CK framework. Logpoint has developed all queries, as well as future technological enhancements, around the common ATT&CK taxonomy. Alerts in Logpoint are configured to the different stages of the ATT&CK model, making it easier to get situational awareness of the entire system. The advanced threat detection in Logpoint SIEM means that security teams can analyze and report trends and behaviors of entities and users within the organization.
Faster detection
Alerts are based on a standard framework, making it easier for analysts to detect malicious activity
Faster response
The ATT&CK steps are sequential, so analysts can predict an adversary’s actions and be one step ahead in the investigation
Comprehensive risk assessment
It’s much easier to map security coverage and risks when your defenses are all based on the same taxonomy
Understand the adversary
Security teams can create a more effective defense to protect their system. ATT&CK helps teams understand the adversary and how they operate
Minimize skills gap
The ATT&CK framework gives junior security analysts without much experience a knowledge base to figure out how to investigate and respond to incidents
Cohesive defense strategy
You can integrate ATT&CK with other security tools and services to standardize your entire infrastructure for a more effective cybersecurity defense
A blueprint for attack techniques
The Logpoint ATT&CK navigator has more information about the tactics and techniques and indicates which are covered by Logpoint SIEM and Logpoint UEBA. Techniques represent how an adversary achieves an objective. Security analysts can use the navigator to match Logpoint alerts with their relevance to ATT&CK, from initial access to privilege escalation to lateral movements to data exfiltration.