
The Threats That Never Went Away
Why v2.29 goes deeper on the tactics attackers still use every day If you want to understand how breaches are happening [...]

Frontline Intel: Pinpointing GRU’s TTPs in the Recent Campaign
Joint Cybersecurity Advisory (CSA) AA25-141A exposes a sustained and multifaceted cyber-espionage campaign attributed to Russia’s GRU Unit 26165, also known [...]
The Impacket Arsenal: A Deep Dive into Impacket Remote Code Execution Tools
In today's evolving threat landscape, we continually see new threat actors emerge and novel attack techniques surface. To keep pace, [...]

Tricked by trust: How OAuth and device code flows get abused
In today’s cloud-first environments, access tokens have become the new keys to the kingdom. Attackers no longer need passwords or [...]

Kubernetes Threat Hunting using API Server Audit Logs
Kubernetes has emerged as the preferred platform for deploying and managing containerized applications in contemporary IT environments. As its adoption [...]

Announcing a new integration between Logpoint and Microsoft Defender XDR
Relying solely on a single security tool can leave vulnerabilities that attackers may exploit. While Microsoft Defender offers robust protection—especially [...]
From Exploit to Ransomware: Detecting CVE-2025-29824
The Microsoft Security blog highlights the active exploitation of CVE-2025-24983, a zero-day vulnerability in the Windows Common Log File System [...]
ClickFix: Another Deceptive Social Engineering Technique
Fast FactsClickFix, first observed in mid-2024, represents a sophisticated form of social engineering that quickly gained traction among adversaries.ClickFix has [...]
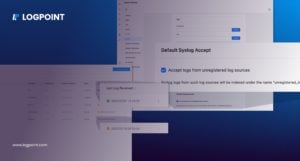
Reduce operational burden and gain efficiency with Logpoint’s latest release
Security Operations Centers (SOCs) and Managed Security Service Providers (MSSPs) are under immense pressure to keep pace with an [...]

Windows Shell Link Vulnerability ZDI-CAN-25373: Detecting Hidden Commands
One of the latest vulnerabilities disclosed by TrendMicro, ZDI-CAN-25373, exposes a flaw in Windows shortcut (.LNK) files that allow attackers [...]
State of Managed Security services: How MSSPs can Capture New Business
European organizations need help managing their cybersecurity. With a threat landscape constantly developing, threats becoming more difficult to detect, [...]

Logpoint 2025 predictions: Cybersecurity in transformation
The year 2025 is upon us, and it’s time to reflect on what’s in store for the cybersecurity industry. [...]
