By Bhabesh Raj Rai, Associate Security Analytics Engineer
First discovered in August 2018, Ryuk is a ransomware strain that has a reputation of being one of the nastiest ransomware families to ever grace the cybercrime scene. After a short hiatus, Ryuk has made a comeback with new tactics that drastically shorten the time between initial intrusion and ransomware deployment.
Ryuk is based on an older ransomware variant called Hermes that was sold on underground cybercrime forums in 2017. Lazarus Group deployed Hermes in 2017, which led researchers to mistakenly believe that Ryuk originated in North Korea. But now, there is a consensus that Russian-speaking cybercriminal groups obtained access to Hermes and operate Ryuk.
Ryuk is one of the first ransomware variants with the ability to identify and encrypt network shares and resources, as well as delete shadow copies on the infected endpoint. According to multiple researchers, Ryuk is deployed as the final payload through TrickBot and Emotet but is now found to use Bazar malware. Bazar has recently become the preferred stealthy, covert malware of choice for attacking high-value targets and is a part of the TrickBot group toolkit arsenal.
Ryuk operators are notorious for demanding higher ransom payments compared to many other ransomware gangs. Joel DeCapua revealed in the RSA Conference 2020 that out of 144.35 million in bitcoin paid to ransomware groups between 2013 and 2019, 61.26 million was sent to Ryuk operators. The attackers go after organizations with critical assets that are more likely to pay, known as “big game hunting.”
A typical Ryuk attack initiates when a user opens a weaponized Office document attached to a phishing email that drops Emotet. Shortly after, Emotet downloads Trickbot, which begins reconnaissance and starts collecting credentials, allowing lateral movement to critical assets connected to the internal network. Ryuk actors then check if the organization is of high value, and finally deploy Ryuk on selected targets completing the attack chain.
Recently, Ryuk returned after a long hiatus with fresh tools and tactics. Ruk operators changed their tactics, techniques and procedures (TTPs) to drastically shorten the time between initial compromise and ransomware deployment. They cut down the time difference from around weeks to a mere couple of days. There are even cases of only a couple of hours between initial compromise and deployment. Nowadays, Ryuk operators deploy procedures such as ADFind, vsftpd, Cobalt Strike, Rubeus and PowerView to accomplish their objectives.
Ryuk actors also escalate privileges using ZeroLogon (CVE-2020-1472), which means they are successfully able to infect the entire enterprise in five hours. Read more about detecting the ZeroLogon exploitation with LogPoint SIEM in our previous blog .
Detecting Ryuk ransomware using LogPoint
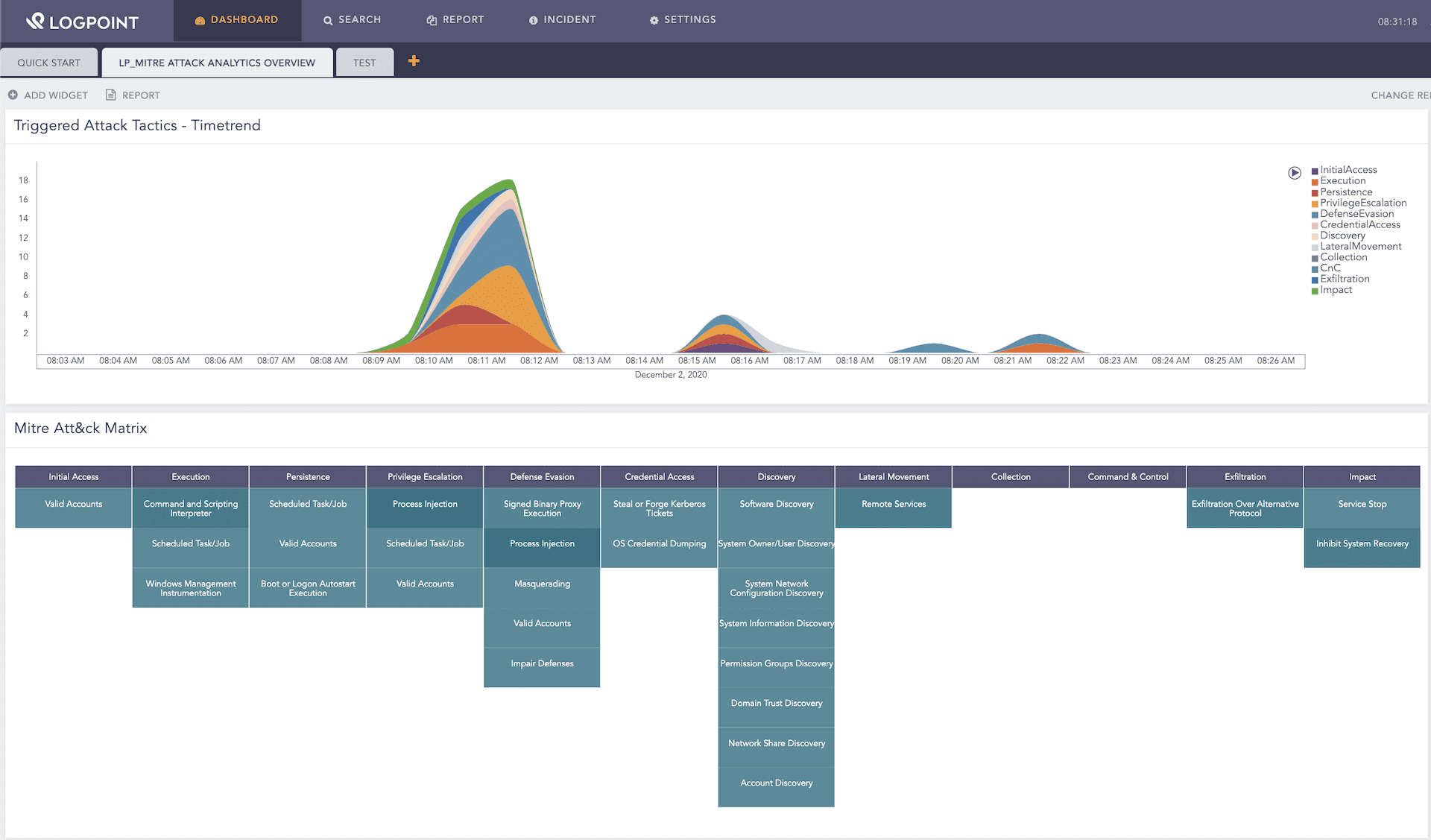
Using the MITRE ATT&CK framework and LogPoint, security teams can detect Ryuk throughout the stages of an attack. Hunt queries related to different TTPs employed by Ryuk are mentioned below.
Using the MITRE ATT&CK framework and LogPoint, security teams can detect Ryuk throughout the stages of an attack. Hunt queries related to different TTPs employed by Ryuk are mentioned below.
Ryuk ransomware Execution
We can look for the initial infection stage by looking at the spawning of command prompt (T1059.003) or PowerShell (T1059.001) from Office products.
norm_id=WinServer event_id=4688 parent_process IN ["*\winword.exe", "*\excel.exe", "*\powerpnt.exe"] "process" IN ["*\cmd.exe", "*\powershell.exe"]
Sometimes, the malicious macro embedded inside the document may directly download and execute the payload. In general, we can look for any suspicious process creations from Office products.
norm_id=WinServer event_id=4688 parent_process IN ["*\winword.exe", "*\excel.exe", "*\powerpnt.exe"]
Usually the payloads are dropped in Temp or ProgramData or C:\Users\Public folders, which we can detect via Sysmon’s file creation logs.
norm_id=WindowsSysmon event_id=11 file=*.exe path IN ["C:\ProgramData*", "*\AppData\Local\*", "*\AppData\Roaming\*", "C:\Users\Public\*"]
Next, we can check for any execution of processes from above the aforementioned paths.
norm_id=WinServer event_id=4688 "process" IN ["C:\ProgramData\*.exe", "*\AppData\Local\*.exe", "*\AppData\Roaming\*.exe", "C:\Users\Public\*"]
Discovery
Ryuk operators are known for using legitimate built-in Windows tools for performing reconnaissance and maintaining stealth. As these commands are not used by normal users, the use of the commands in a short time frame can prove to be a valuable indicator of an ongoing reconnaissance activity in the environment.
norm_id=WinServer event_id=4688 "process"="*\cmd.exe" command IN ["*whoami*", "*nltest /domain_trusts*", "*net*group*", "*ipconfig*", "*nltest /dclist*", "*sysinfo*" "*net*view*"]
| chart count() by host
| search count() > 4
On the most recent Ryuk infections, the operators used ADFind.exe, which is a third-party tool to collect Active Directory information. The best way to hunt for ADFind.exe execution is by looking for its command-line options rather than the process name because it can easily be renamed.
norm_id=WinServer event_id=4688 "process"="*.exe" command IN ['* -f *objectcategory=*', '* -sc trustdmp*']
Ryuk operators also check for installed antivirus software (T1518.001) on identified endpoints via WMI.
norm_id=WinServer event_id=4688 "process"="*\wmic.exe" command="*SecurityCenter2*AntiVirusProduct*"
Active Directory information collection is performed by using the popular PowerView module. LogPoint provides a POWERSPLOIT_RECON_MODULES list that contains the commonly used PowerView commands such as Get-NetComputer and Find-LocalAdminAccess.
norm_id=WinServer event_id=4104 script_block IN POWERSPLOIT_RECON_MODULES
When the Ryuk actors get access to a domain controller, they use PowerShell’s Active Directory module to discover hostnames, operating systems and last logon dates of all systems connected in the Active Directory.
norm_id=WinServer event_id=4103 command="Import-Module" payload="*ActiveDirectory*"
norm_id=WinServer event_id=4103 command="Get-ADComputer" payload="*DNSHostName*LastLogonDate*"
Defense Evasion
Ryuk actors attempt to disable Microsoft Defender (T1562.001) via PowerShell which security teams can easily detect through PowerShell’s Script Block logging.
norm_id=WinServer event_id=4104 script_block="Set-MpPreference -DisableRealtimeMonitoring $true"
Ryuk actors have also upped their game on defense evasion by adding “process hollowing” (T1055.012) to their TTPs. We can detect process hollowing of cmd.exe or regsvr32.exe by looking at their child process creations without any command-line arguments.
norm_id=WindowsSysmon event_id=1 parent_image="*\cmd.exe" image IN ["*\net.exe", "*\net1.exe", "*\nltest.exe", "*\ipconfig.exe"] parent_command="*\cmd.exe"
Similarly, we can detect process hollowing of svchost.exe by its anomalous behaviors, such as its parent process not being services.exe or its command-line arguments not consisting of any -k parameter, which is definitely suspicious.
norm_id=WinServer event_id=4688 "process"="*\svchost.exe" (-parent_process="*\services.exe" OR -command="* -k *")
Ryuk operators will also proceed to use the built-in icacls.exe (T1222.001) to grant “Everyone” full access to the root of the drive, while also propagating new permissions down the folder structure to prevent any permissions issue that may occur during the later encryption phase.
norm_id=WinServer event_id=4688 "process"="*\icacls.exe" command="icacls*:*/grant everyone*"
Persistence
It should be noted that some versions of Ryuk have dropped the persistence feature, which was the addition of a new Run key entry in the registry (T1547.001) to establish persistence across reboots.
norm_id=WinServer event_id=4688 "process"="*\cmd.exe" command="*reg add*\Windows\CurrentVersion\Run*.exe*"
Sometimes, in conjunction with the above persistence method, Ryuk also creates scheduled tasks (T1053.005) in C:\Users. We can monitor the location to detect Ryuk in its early stages.
norm_id=WinServer label=Schedule label=Task label=Create -user=*$ command IN ["*C:\Users\*", "*C:\Windows\Temp\*"]
Credential Access
Recently, Ryuk actors use the open-source LaZagne tool to gather credentials for facilitating lateral movement, which we can detect via Sysmon’s Process Access event logs.
norm_id=WindowsSysmon event_id=10 call_trace="*C:\Windows\SYSTEM32\ntdll.dll+*|C:\Windows\System32\KERNELBASE.dll+*_ctypes.pyd+*python27.dll+*"
Ryuk actors also attempt to Kerberoast (T1558.003) using the popular Rubeus tool.
norm_id=WindowsSysmon event_id=7 -source_image="C:\Windows\System32\*" image IN ["*\clr.dll", "*\kerberos.dll", "*\cryptdll.dll", "*\dsparse.dll"]| chart distinct_list(image) as images, distinct_count(image) as dc by source_image
| search dc=4
Lateral Movement
Ryuk occasionally uses WMI (T1047) to laterally execute dynamic link libraries (DLLs).
norm_id=WinServer event_id=4688 "process"="*\wmic.exe" command="*/node*process call create*"
Ryuk actors heavily use Remote Desktop Protocol (RDP) (T1021.001) for lateral movement or deploying the final Ryuk payload. Mostly, Ryuk actors initiate RDP connection from the compromised domain controller. Logs from TerminalServices/RemoteConnectionManager provide the source IP address from where the actors initiated the RDP connection.
So, we can look out for any RDP connection from any DC to a workstation.
norm_id=WinServer event_source="Microsoft-Windows-TerminalServices-RemoteConnectionManager" event_id=1149
| rename eventxml.param3 as source_address
| search source_address IN WINDOWS_DC
Apart from RDP, Ryuk actors laterally drop malicious DLL or EXE in Perflogs location and later execute them via rundll32 (T1218.011) or regsvr32 (T1218.010).
norm_id=WindowsSysmon event_id=11 file IN ["*.dll", "*.exe"] path="C:\Perflogs"
norm_id=WinServer event_id=4688 "process" IN ["*\rundll32.exe", "*\regsvr32.exe"] command="*C:\Perflogs*.dll*"
Ryuk has also added the Wake-On-LAN feature to wake up sleeping devices in the network.
norm_id=WinServer event_id=4688 "process"="*.exe" command="* 8 LAN*"
Exfiltration
Ryuk actors are also known to exfiltrate data collected during discovery via FTP (T1048.003), which we can easily detect via Sysmon.
norm_id=WindowsSysmon (event_id=1 image="*\ftp.exe") OR (event_id=3 destination_port=21)
Impact
Ryuk operators use a batch file (usually kill.bat) that invokes taskkill to kill various processes so that the encryption process runs smoothly.
norm_id=WinServer event_id=4688 parent_process="*\cmd.exe" "process"="*\taskkill.exe"
| chart count() as cnt by host
| search cnt > 2
Ryuk stops various services like the Security Accounts Manager Service (samss) (T1489) via the net command, which can act as a very high fidelity indicator.
norm_id=WinServer event_id=4688 "process" IN ["*\net.exe", "*\net1.exe"] command IN ["*stop *samss*"]
As is the norm now in ransomware, Ryuk uses WMI or vssadmin to delete volume shadow copies to make recovery difficult.
norm_id=WinServer event_id=4688 ("process"="*\wmic.exe" command="*shadowcopy delete*") OR ("process"="*\vssadmin.exe" command="*delete shadows*quiet*")
Finally, the operators want to ensure the recovery process after infection is as difficult as possible. Ryuk operators use bcedit.exe (Boot Configuration Data Editor) to disable Windows Automatic Startup Repair feature (T1490), as well as to change the boot status policy to ignore all failure.
norm_id=WinServer event_id=4688 "process"="*\cmd.exe" command IN ["*bootstatuspolicy ignoreallfailures*", "*bcdedit /set*recoveryenabled no*"]
Reducing incident response time is key
Ryuk has certainly made a fierce reputation in the ransomware scene even before its current resurgence. Now, blue teams must further up their game to remain ahead by building defenses for newer TTPs used by Ryuk actors. Since Ryuk relies on droppers and other malware before its deployment, there are several detection possibilities at various stages.
It’s common for ransomware groups to strike a partnership with other cybercriminal groups, commonly called “initial access brokers.” Initial access broker groups act as the supply chain to criminal underground groups, providing them with access to a range of compromised systems. Using already compromised systems enables ransomware groups to easily gain access to an organization’s internal networks, from where they start to escalate privileges, move laterally and finally deploy the ransomware.
Since Ryuk operators now move quicker than ever after initial infection to deploy ransomware as quickly as possible. We advise Blue teams to use CISA’s alert on Ryuk to better their infrastructure against Ryuk and other ransomware so that it is never too late to avert disaster.