Updated August 2023
Threats are continually changing and becoming more sophisticated, making it impossible to buy a tool that detects every potential cyber threat. You can help protect your business by taking a proactive approach to threat hunting. According to the 2020 Verizon Data Breach report, more than 25% percent of breaches took months or longer to discover. Months inside the network is more than enough time to cause damage to any organization.

What is Threat Hunting?
Threat hunting is a proactive way to uncover advanced threats that are difficult to detect using automated security systems. Organizations primarily use cyber threat hunting to detect top-tier attackers, such as advanced persistent threats from state-sponsored groups. Government-backed attacks are covert and persistent. They aim to maintain a foothold in the network for a longer period of time so as not to cause significant disruption that automatic security systems can detect. Undetected, state-sponsored attackers can snoop around the network looking for confidential material or login credentials that will allow them to move laterally through the environment.
Threat hunters actively look for evidence of active, covert threats in the IT environment. Successful threat hunters are experienced security analysts who are backed by threat-hunting tools and have established security operations and response capabilities.
Essentials when Hunting Threats
Being proactive is one of the key aspects of threat hunting. Threat hunters assume that adversaries are already in the system. They look for unusual behavior that could indicate the presence of malicious activity. Successful threat hunters look for clues that indicate ongoing attacks in the system. Threat hunters then take the clues and create a hypothesis about how the hacker could carry out the attack.
Hunting for threats is an interactive process that involves identifying and investigating clues and redefining the hypothesis as the threat hunters track down the threat. The security team is vital to threat hunting and needs to have advanced threat knowledge and know the organization’s IT system inside and out. While the security team will use tools to help identify threats, the team is the most important part of delivering results.
What do you Need to Start Cyber Threat Hunting?
Organizations looking to start hunting threats need first to ensure they have threat hunters who have the experience and skills required to understand and look for threats. While threat-hunting tools are helpful, the security team is actually doing the hunting. The best threat hunters know their adversaries and can think like them. They know the different tactics, techniques, and procedures (TTPs) that their adversaries are using and how to look for them within the network.
Cyber threat hunting typically involves a massive amount of information. Security teams benefit from having a centralized data set to reveal insights efficiently. Typical cybersecurity tools used by mature security teams can help threat hunters reach their goals faster and easier. A SIEM solution will collect and enrich logs so that threat hunters can easily search the data while investigating potential threats. Adding UEBA will speed up a threat hunter's ability to identify suspicious and abnormal behavior in the network. It also helps the threat hunter form a hypothesis about the threat. Threat intelligence will help threat hunters start the hunt by providing threat indicators and TTPs they can use as initial clues.
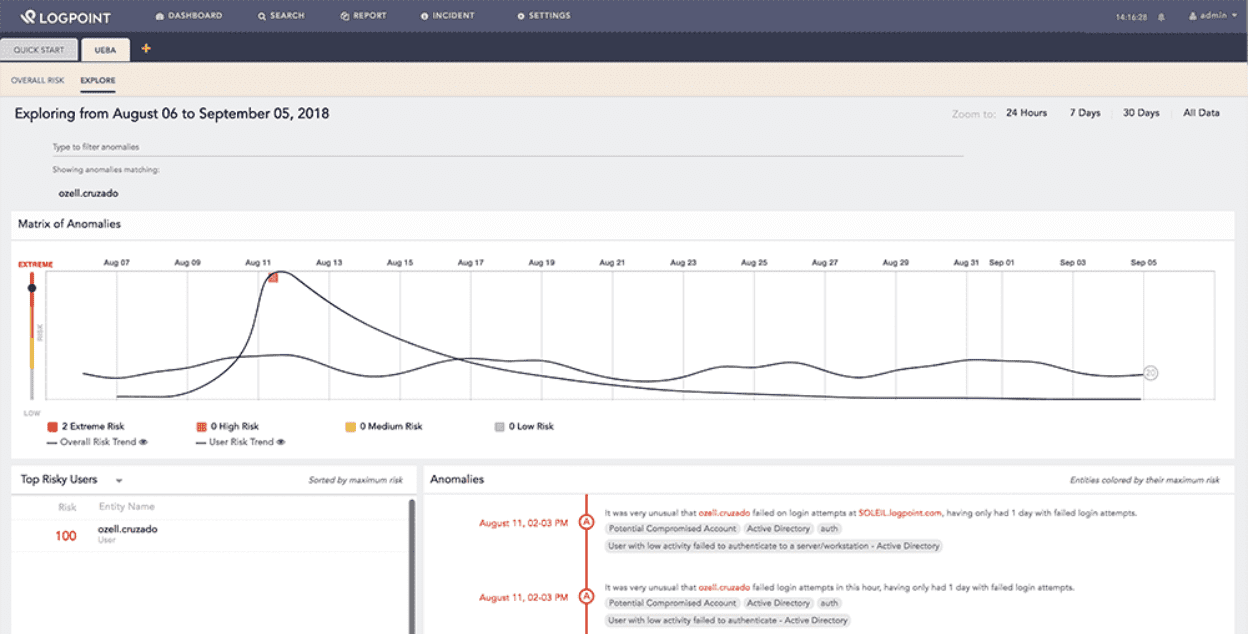
Security tools, like SIEM and UEBA, can help security teams speed up and simplify threat hunting.
Threat Hunting Step-by-Step
Cyber threat hunting typically involves three steps: a trigger, an investigation, and a response.
Step 1: The trigger
Some organizations have scheduled programs for hunting threats, regardless of whether there is a concrete cause. Threat hunters usually identify the trigger in a specific application or area of the network. The threat hunter formulates a hypothesis based on unusual events that may indicate malicious activity.
Step 2: Investigation
Threat hunters typically use threat-hunting tools to deep dive into potential compromises within systems of the infrastructure. The investigation continues until the hypothesis is either proven or unproven.
Step 3: Response
Responding appropriately to malicious activity should follow the organization’s threat-hunting process. Usually, it involves communicating the new intelligence to the security and operations teams, enabling them to respond quickly and mitigate the threat. Documenting the attacker’s methods allows the organization to analyze and predict similar compromises in the future.
Choose the Right Tools
When you’re ready to start threat hunting, you can take advantage of the MITRE ATT&CK framework to help structure the hunt. ATT&CK is a standard framework that is continuously updated with TTPs from known attackers. When threat hunters have their starting points, they can use ATT&CK to help create a hypothesis and search for active or residual signs of attack activity. If the hypothesis doesn’t pan out, threat hunters have to look for other clues to start the hunt.
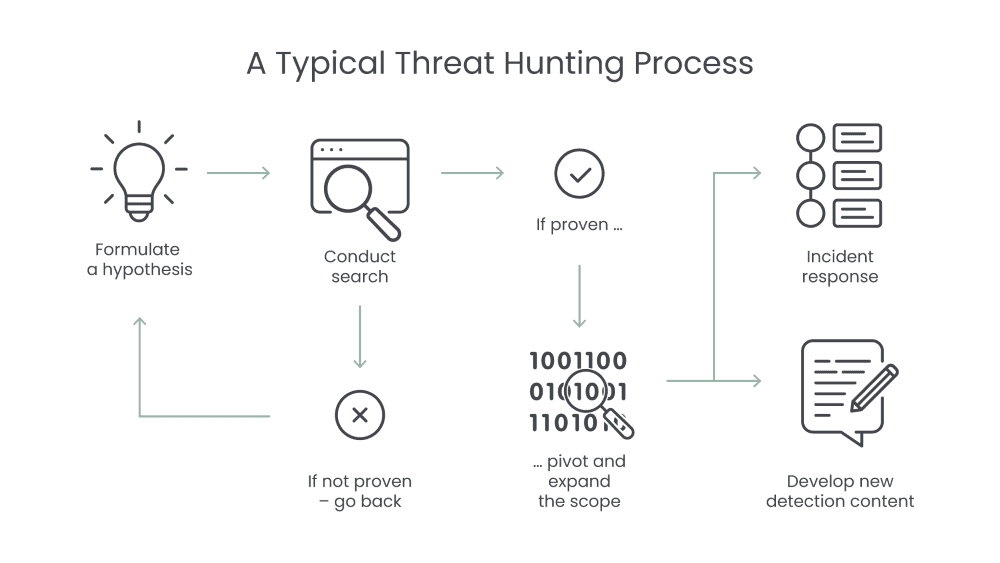
However, if threat hunters find evidence to support the attack hypothesis, then they need to build out the attack story by finding related resources. Security tools like SIEM, UEBA, and the ATT&CK framework can help threat hunters pivot and get a comprehensive overview of the potential threat. If the security team finds a threat, then they resolve it and follow the organization’s policies to maintain the security posture.
It’s difficult for organizations to conduct effective threat hunting. They need highly skilled employees and a mature security program. The right threat-hunting tools can help speed up and make the process easier. Ultimately, the threat hunter plays the biggest role in successfully uncovering threats.
Level Up your Threat Hunting with Converged SIEM
Logpoint Converged SIEM: SIEM fits seamlessly with SOAR, UEBA, and more in one platform. Converged SIEM helps SOC teams combine data sets from multiple sources. Instead of using multiple standalone products, they now have one single source of truth. It is the only unified platform that delivers SIEM+SOAR, UEBA, EDR capabilities and security monitoring of SAP systems for both enterprises and MSSPs.
The benefits of a converged platform include full data integration for automated TDIR, no integration or maintenance, out-of-the-box compliance support, and flexible deployment based on your needs.







