By Kushal Gajurel, Associate Security Analytics Engineer, LogPoint
On the first Patch Tuesday of 2020, on January 14, Microsoft addressed a critical vulnerability uncovered by the NSA. The vulnerability CVE-2020-0601 opens up an exploitation where an attacker can spoof certain cryptographic operations on Windows. The vulnerability was discovered in the CryptoAPI subsystem used by Windows and most software running on Windows.
The Windows CryptoAPI Spoofing Vulnerability dubbed “The ChainOfFools” or “CurveBall” attack is a result of a flaw occurring when validating certificates that are using Elliptic Curve Cryptography (ECC).
By exploiting the flaw, attackers can spoof certificates, allowing an attacker to trick Windows into believing that an executable has been code-signed by a trusted third party, for instance Microsoft.
Affected products include:
- Windows 10 (all build numbers)
- Windows Server 2016
- Windows Server 2019
Older versions of Windows are not affected.
Detection using LogPoint
Detection is possible in LogPoint after the patch has been installed. Once the patch has been installed, Windows will detect and log to the eventlog all attempts to exploit the vulnerability. The attempts will be logged through the CveEventWrite mechanism.
- SourceName: Audit-CVE OR Microsoft-Windows-Audit-CVE
- EventID: 1
- Channel: Application
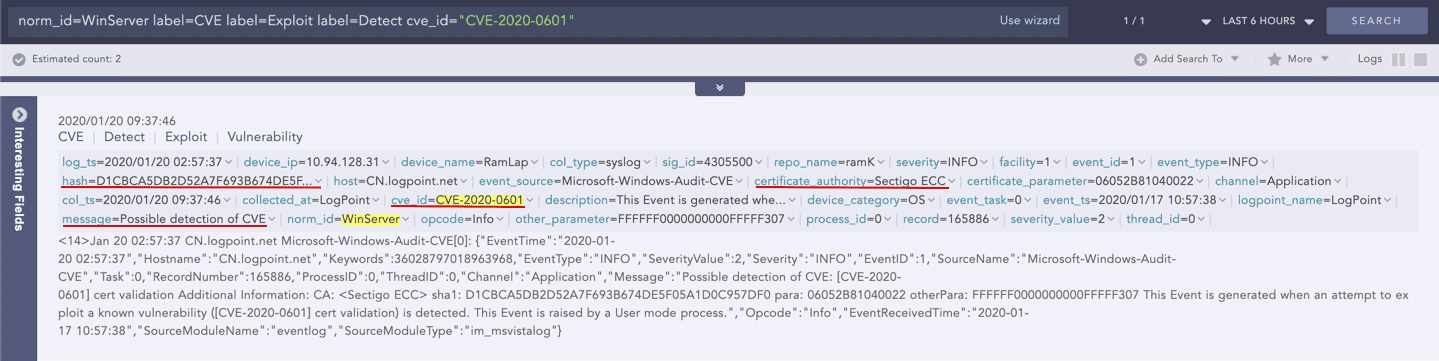
LogPoint query
norm_id=WinServer label=CVE label=Exploit label=Detect cve_id="CVE-2020-0601"