Logpoint SIEM: Reduce Cyber Risk with Powerful Data Analysis
-
Decrease the time to detect and investigate threats by pairing enhanced visibility across your entire IT infrastructure with contextual data.
-
Achieve more effective detection and precise incident investigations with all data sources connected under one single source of truth.
-
Meet regulatory compliance criteria with ease by automatically generating out-of-the-box reports and audit records of all changes in your system.
Over 1,000 Organizations Across 70 Countries Use Logpoint SIEM
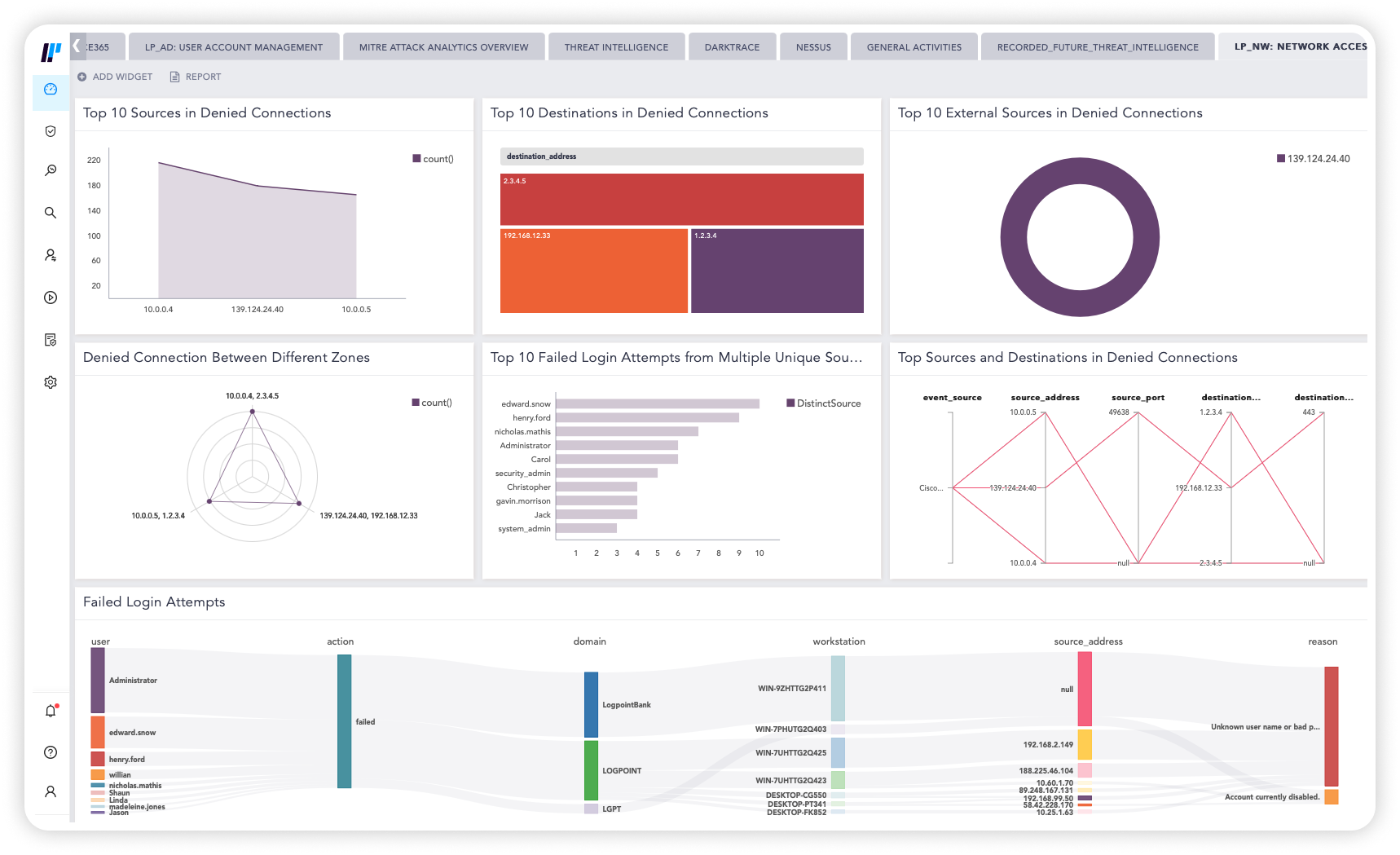
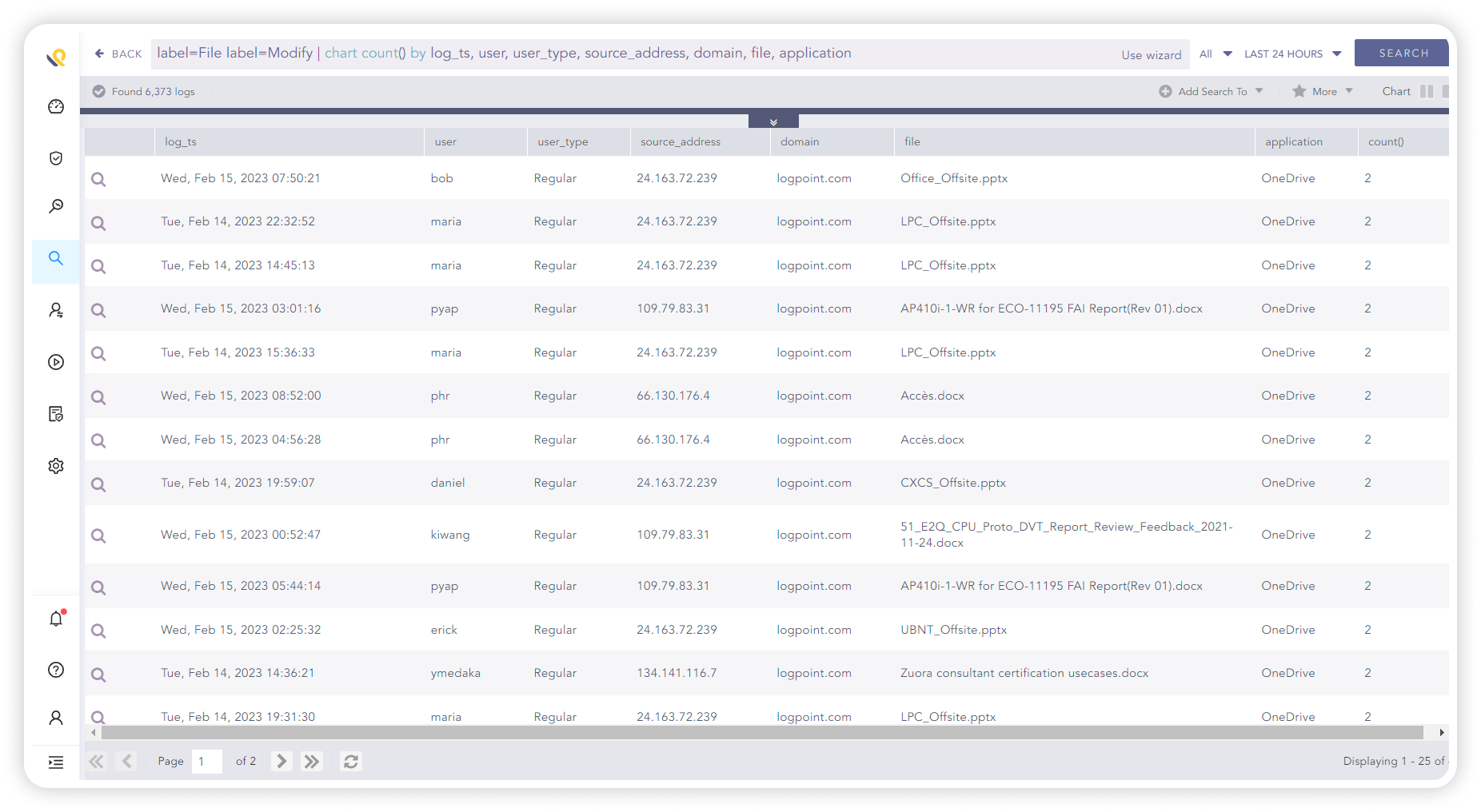
Data Monitoring – Centralized for Heightened Visibility
Logpoint SIEM collects event data produced by any device, application or endpoint within your infrastructure.
By centralizing the data monitoring you improve your visibility into your network and IT infrastructure.
POWERFUL DATA ANALYSIS:
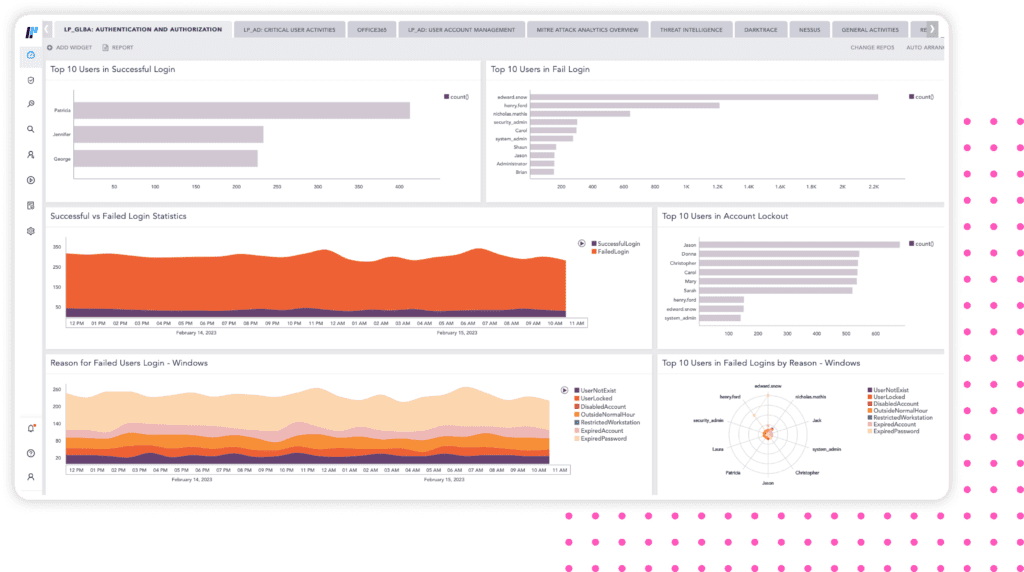
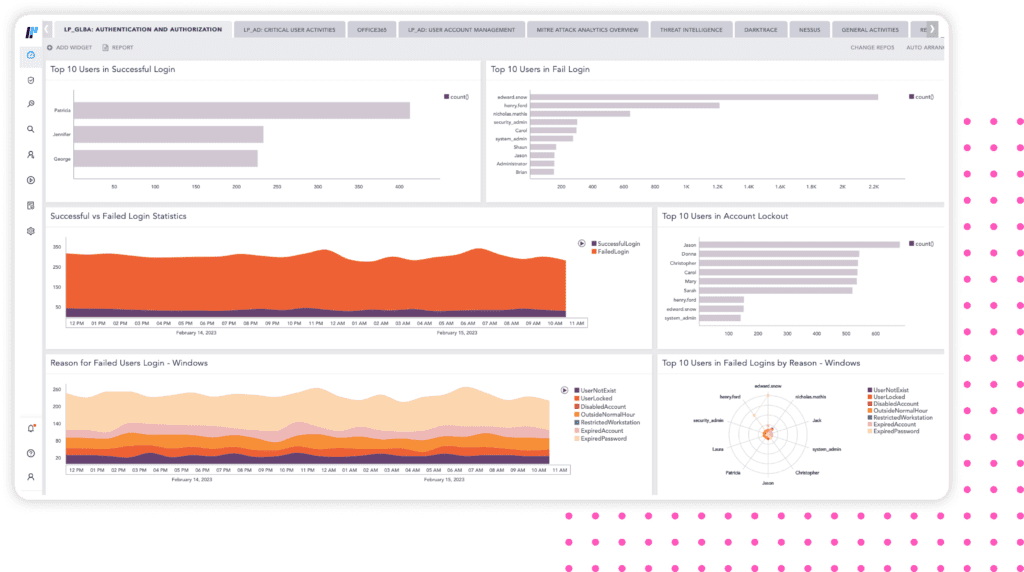
Improve Your Threat Detection and Investigation
Logpoint SIEM makes it easy to analyze user activity and incidents by translating complex log data into a single language and maps the alerts to MITRE ATT&CK.
The data is visualized intuitively and puts it into context allowing you to quickly detect and investigate incidents.
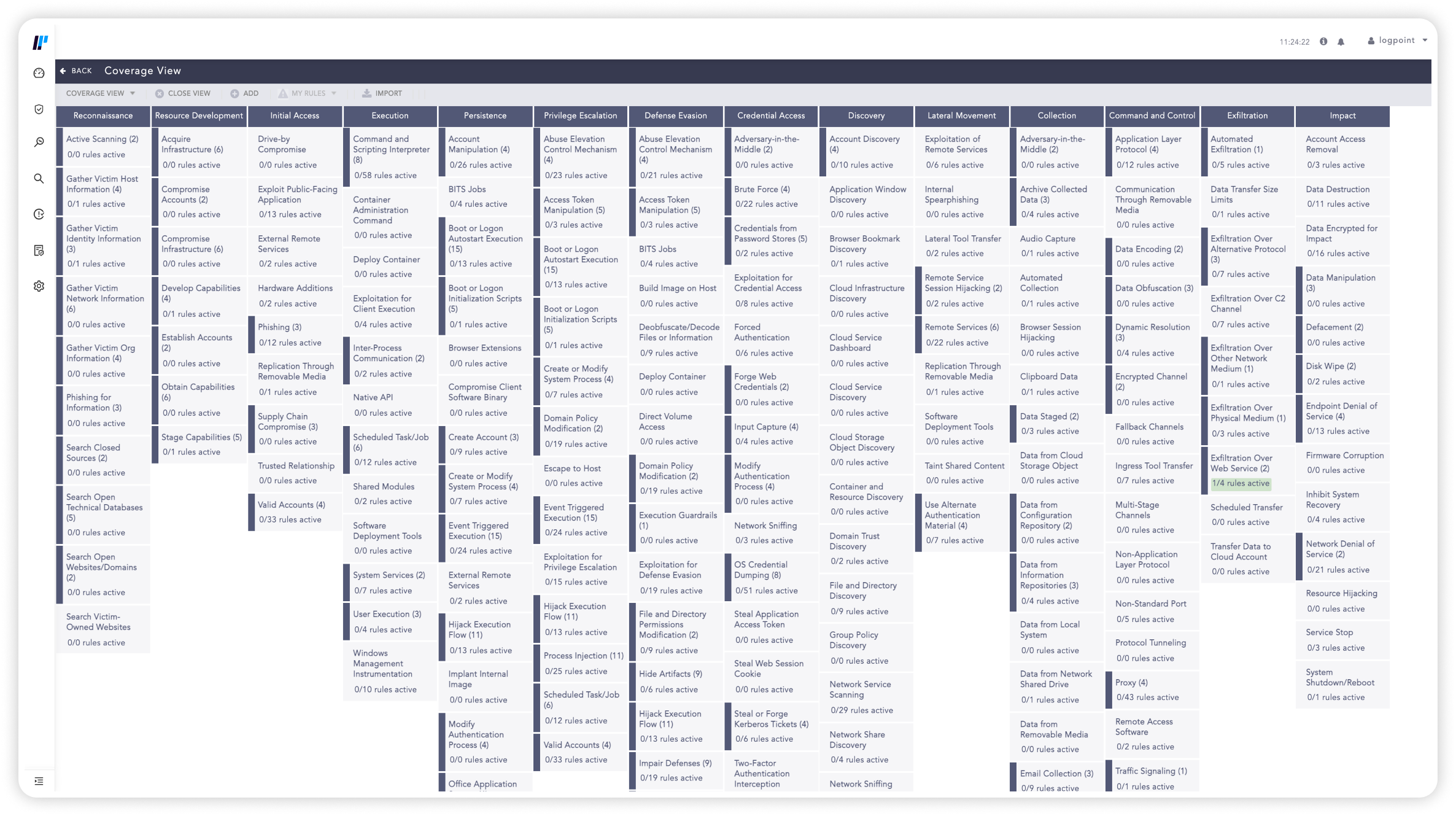
OUT-OF-THE-BOX COMPLIANCE SUPPORT:
Effortless Compliance Adherence
Logpoint SIEM provides compliance for all major regulatory domains such as Schrems-II, HIPAA, GDPR, and supports forensic analysis and investigation, making it effortless to present compliance evidence and determine the root cause of the breaches.
Using Logpoint fundamentally changes the way you work with log data in your infrastructure. With Logpoint log data becomes a useful tool. It allows us to take control and get a meaningful, constant output that enables us to spot potential problems and react promptly. Before things turn into a real threat.
Converged SIEM
Looking to consolidate your tech stack? See how SIEM fits with SOAR, UEBA, and more in one platform. Converged SIEM helps SOC teams combine data sets from multiple sources. Instead of using multiple standalone products, they now have one single source of truth. It is the only unified platform that delivers SIEM+SOAR, UEBA, EDR capabilities and security monitoring of SAP for both enterprises and MSSPs.
- Full data integration for automated TDIR
- No integration or maintenance required
- Out-of-the-box compliance support
- Flexible deployment based on your needs
Precise Detection of Malware and Lightning Fast Remediation of Incidents in Endpoints with AgentX
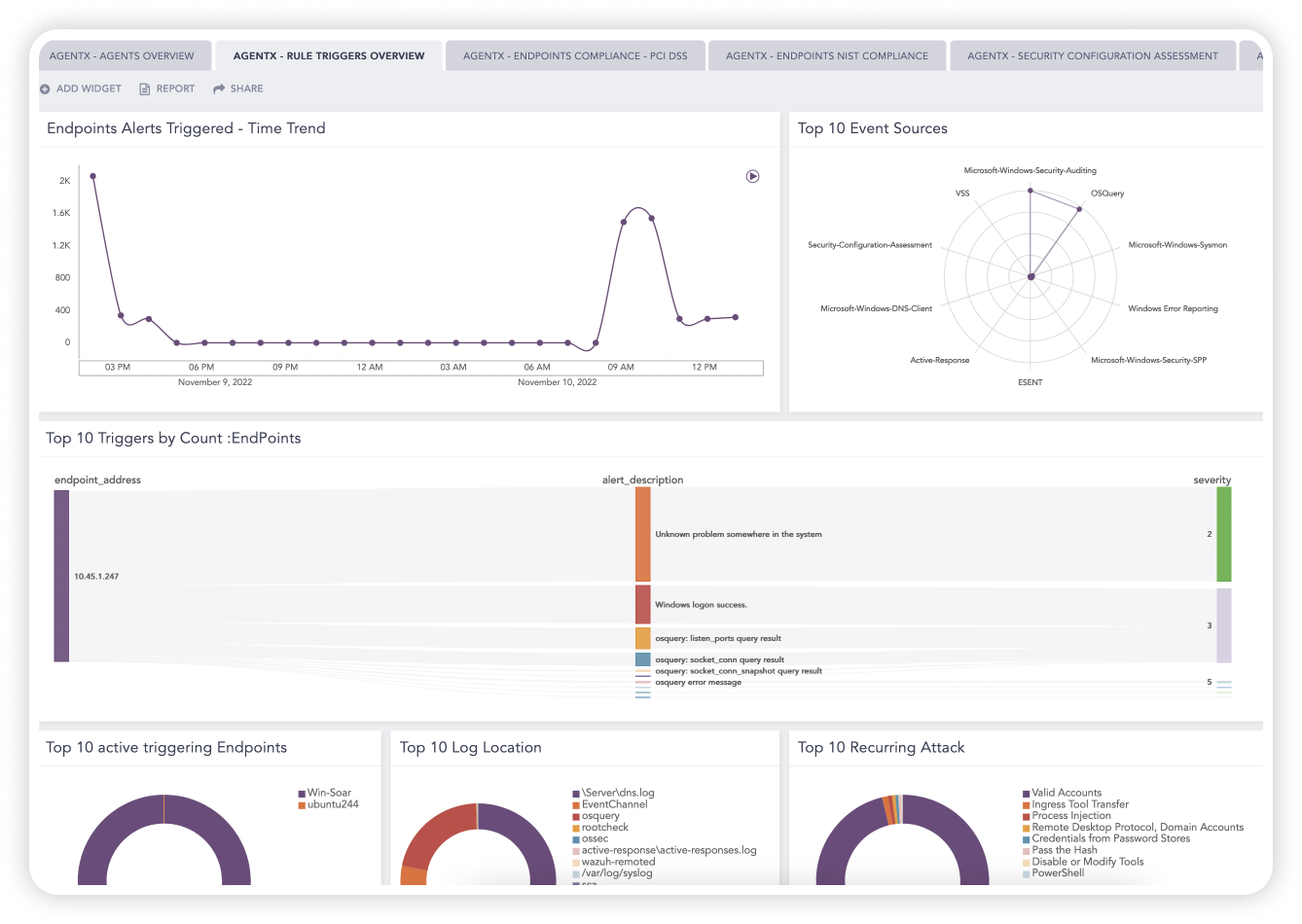
Complex cyber tech stacks make it difficult for security analysts to maintain an efficient portfolio of tightly interconnected tools.
With a converged solution that combines SIEM, SOAR and native Endpoint Security, Logpoint speeds up TDIR capabilities without adding additional vendors or tools into the mix.
AgentX collects logs and telemetry from your endpoints and normalizes them into a single taxonomy via SIEM.
Endpoint data helps to enrich SIEM+SOAR events providing the analyst with additional context regarding incidents and provides a more detailed analysis of the threats and incidents originating from endpoints.
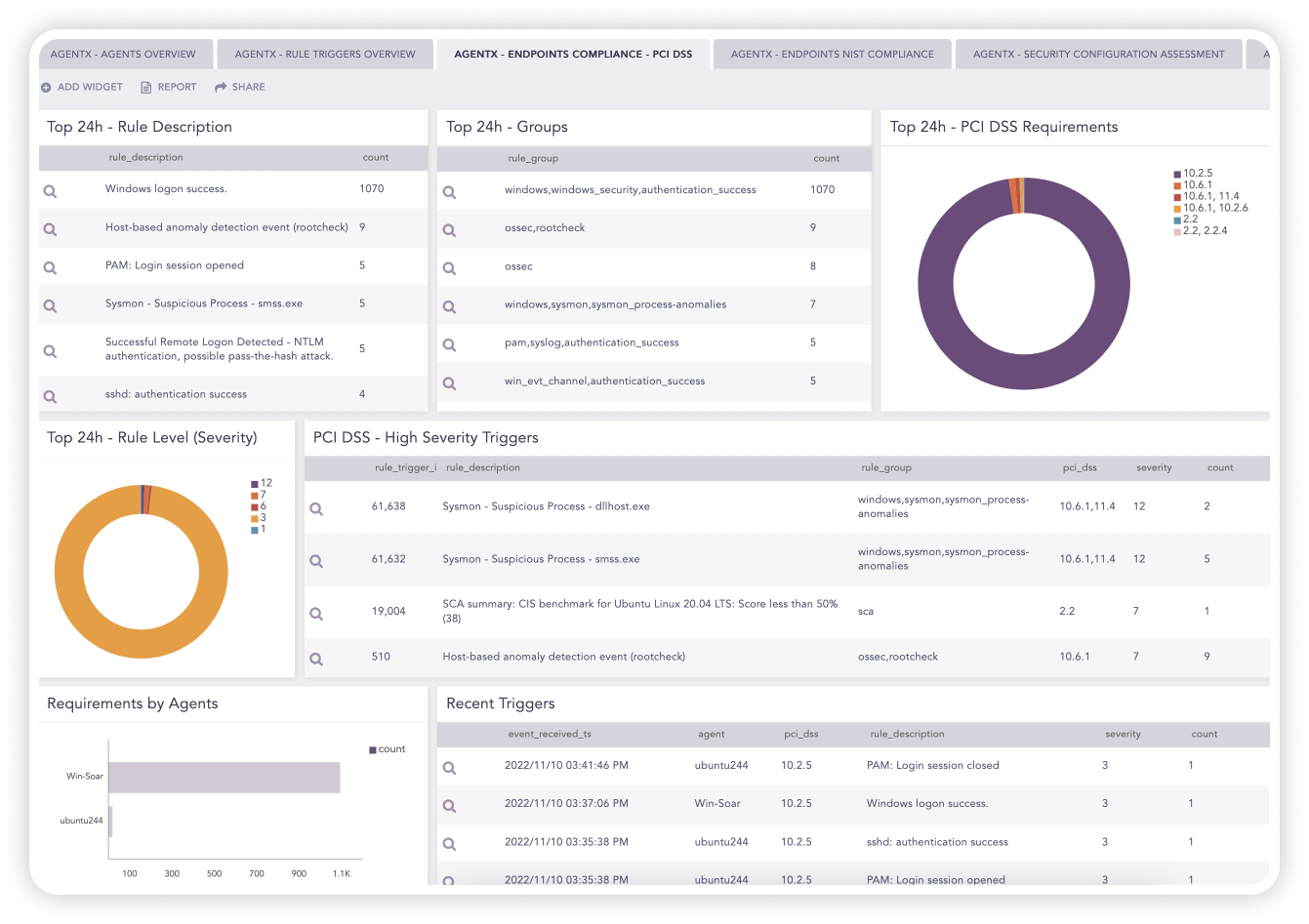
AgentX enriches event logs and telemetry with compliance standards information from e.g. GDPR, NIS2, and HIPAA so analysts can easily identify any events corresponding to regulatory compliance.
In addition, AgentX also performs policy checks via pre-defined Center of Internet Security (CIS) hardening guides to maintain standard configuration through the monitored endpoints and perform efficient compliance and security audit checks.
Around 40% of organizations acknowledge IT resources are stretched too thin and cybersecurity personnel are struggling to protect their organizations against the increasing number of threats.
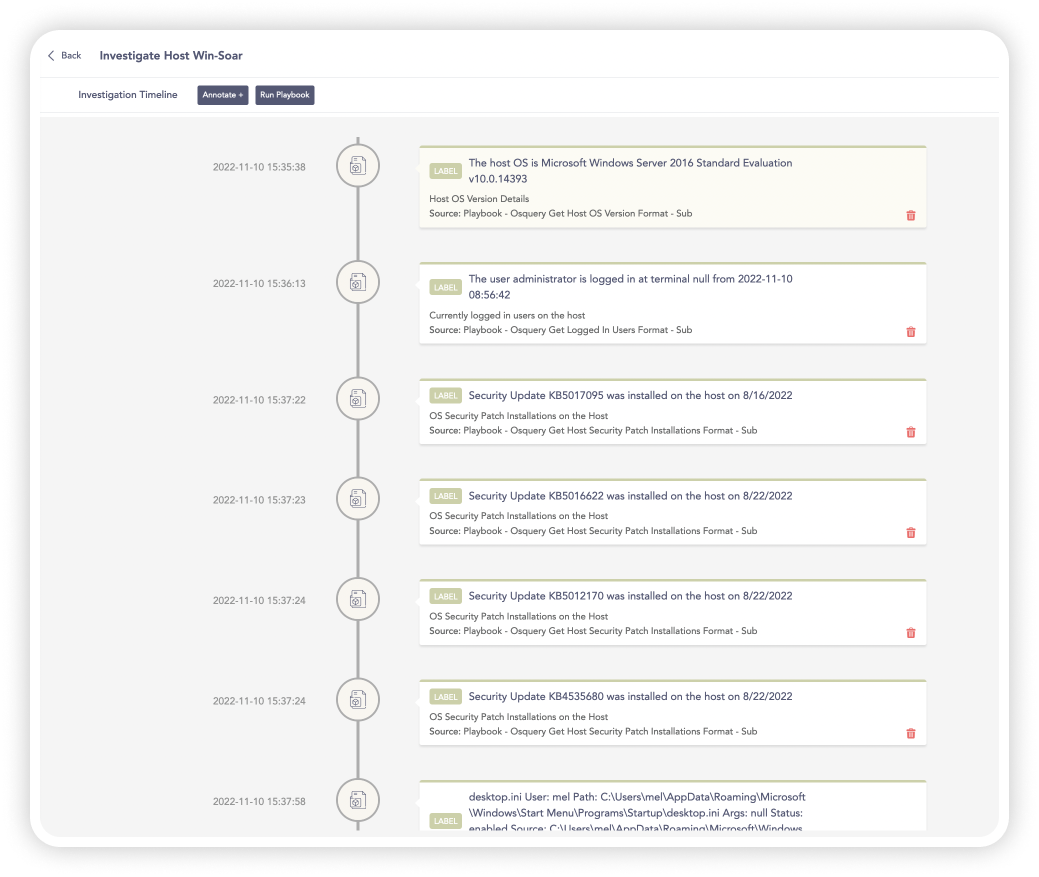
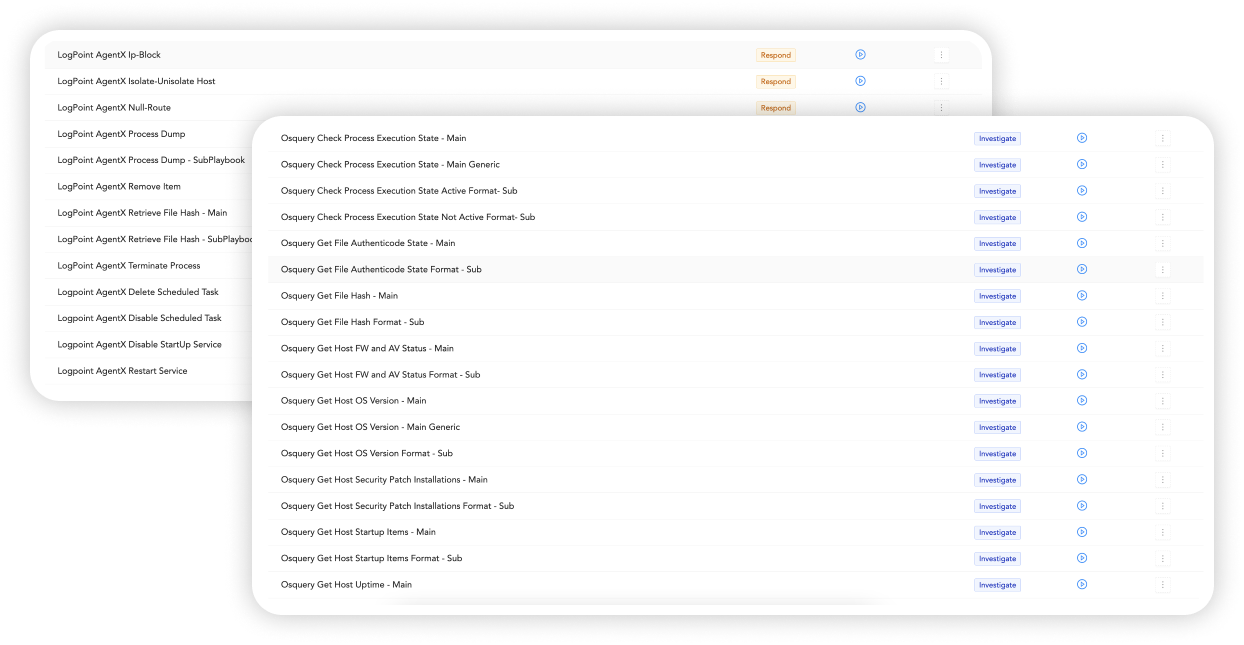
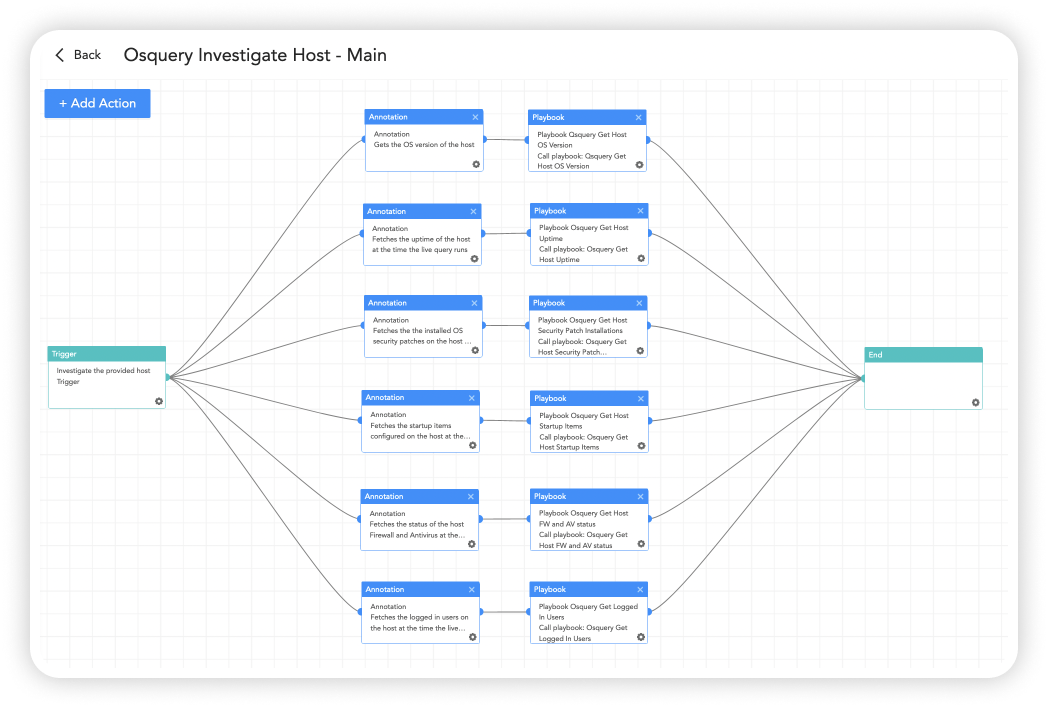
Logpoint’s lightweight AgentX ships with osquery actions and investigation playbooks that retrieve contextual information and state of the endpoints in near real-time for efficient investigations from a single console, decreasing mean time to investigate and mean time to respond.
The lack of visibility and high mean time to respond to threats across workstations and servers of employees causes ineffective security operations, leaving organizations wide open to threats.
With out-of-the-box security content and investigation and response playbooks, AgentX combined with our SIEM+SOAR gives you precise and fast detection and response capabilities.

