By Nilaa Maharjan, Security Research
Index
Executive Summary:
- IcedID, aka BokBot, is a banking trojan that has evolved multiple times and is now used as an initial access broker.
- It’s one of the fastest and more prevalent ransomware threats and is being used by multiple threat actors like Conti and REvil but also as a gateway to other malware like XingLocker.
- Campaigns used to deliver IcedID have been rapidly increasing with phishing emails, contact forms, and spoofed invoices and have been targeting Ukraine-based companies during the conflict.
- On the initial IcedID payload execution the threat actors use Cobalt Strike and RDP to move across the network and use WMI and PsExec to deploy further ransomware.
- It’s difficult to predict how profitable IcedID has been. But many ransomware groups have been using it, which ensures the threat posed is high.
Threat analysts at Logpoint have been tracking activity related to IcedID. In many cases they have been spreading via multiple initial access methods. We are condensing the attacks into a blog and report and cover two particular cases: First, where contact forms published on websites are abused to deliver malicious links to enterprises using emails with fake legal threats, and second, using spoofed invoices. In either of the cases, the emails instruct recipients to click a link to review supposed evidence behind their allegations but are instead led to the download of IcedID, an info-stealing malware.
From the trends, IcedID has dropped but its instances are still significant.
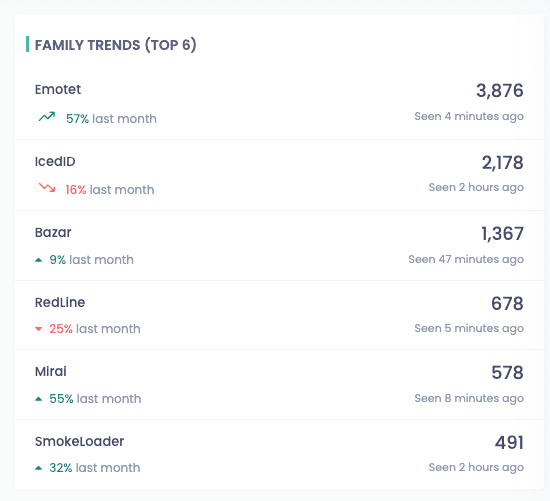
Figure 1. Ransomware Family trends compared to last month
(Source: OVTracker)
In this edition of the Emerging Threat Protection report, we research this malware attack and how the techniques assist attackers in their objective of discovering new ways to infect computers. We have been releasing alerts, search templates, and playbooks to rapidly detect emerging threats in collaboration with partners.
Why is this threat noteworthy?
- Attackers are exploiting legitimate infrastructure. A simple contact form on a webiite can seem pretty innocent, but attackers use them to circumvent security measures making this threat extremely evasive. Furthermore, attackers employ valid URLs, in this case, Google URLs that need victims to sign in using their Google credentials.
- Contact form linked emails are used to distribute the IcedID virus, which may be used for reconnaissance and data exfiltration and can lead to further malware payloads such as ransomware.
- Attackers are constantly looking for new ways to infiltrate networks, and they frequently target services exposed to the internet. Organizations must ensure they are protected.
While this specific campaign distributes the IcedID malware, the delivery method can be used to distribute a variety of other viruses, introducing new hazards to the company. a
As a banking trojan it has grown into a gateway for more sophisticated attacks such as human-operated ransomware. It links to a command-and-control server and downloads further implants and tools, allowing attackers to conduct hands-on-keyboard attacks, steal credentials, and move laterally across vulnerable networks to distribute other payloads.
Ice-breaker #1. Delivering IcedID via contact forms
Contact form pages are commonly used on websites to allow site visitors to communicate with site owners without disclosing their email addresses to potential spammers.
However, during this campaign we noticed an increase in misused contact form and subsequent emails aimed at businesses. This suggests that attackers may have utilized a technology that automates this activity while avoiding CAPTCHA safeguards.
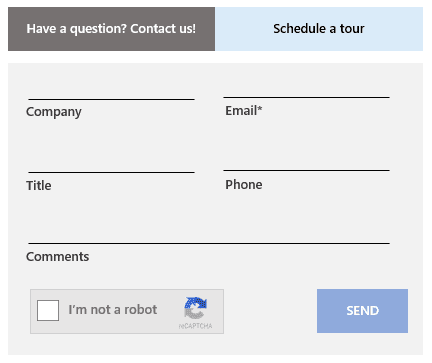
Figure 2. Sample contact form that attackers take advantage of by filling in malicious content, which gets delivered to the target enterprises
In this campaign, the malicious email delivered to the recipient’s mailbox appears trustworthy as it was supposedly sent from trusted email marketing systems.
Attackers fill out and submit the web-based form, an email message containing the attacker-generated message is sent to the associated contact form recipient or targeted company. The message employs forceful and urgent wording (“Download it right now and check it out for yourself”), putting the receiver under pressure to act quickly, and ultimately users are duped into clicking the links to avoid supposed legal action.
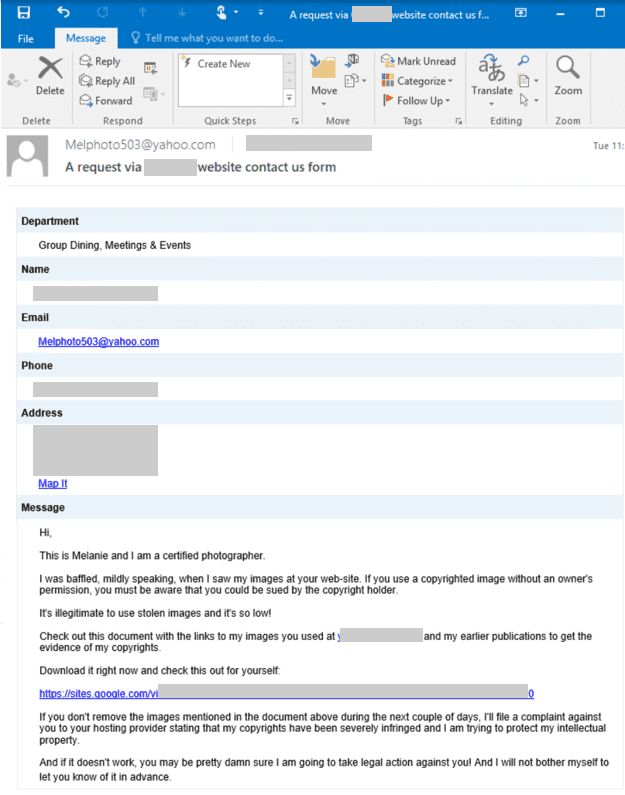
Figure 3. A sample email delivered via contact forms that contain malicious content added by attackers (Source: Microsoft)
Along with phoney legal threats placed in the comments, the message content includes a link to a sites.google.com page where the receiver can view the allegedly stolen images.
When the recipient clicks the link, they are taken to a Google page where they must sign in using their Google credentials. Due to the additional authentication layer, detection methods may fail to recognize the email as malicious entirely.
The sites.google.com page automatically downloads a malicious ZIP file containing a deeply obfuscated.js file after the email recipient checks in. The malicious.js file is executed via WScript to create a shell object for launching PowerShell to download the IcedID payload (a.dat file), which is decrypted by a dropped DLL loader, as well as a Cobalt Strike beacon in the form of a stageless DLL, allowing attackers to remotely control the compromised device.
Ice-breaker #2. Delivering IcedID via Spoofed Invoices
Spearphishing is extremely difficult to detect when it uses industry-specific phrases generated from intelligence-gathering tactics to deceive a receiver into opening a file. This is especially true when an enemy understands how a firm operates and the processes that support it. Using this knowledge, a lure taking advantage of day-to-day activities, such as settling the cost of a fuel transaction, can be created.
As an example, while looking at cyber attack techniques used against Ukraine, we discovered a case in which a gasoline firm in Kyiv. They received a spearphishing e-mail with an attached counterfeit invoice from another fuel provider. We looked at this in depth into back in April.
There are intriguing deployment strategies, such as employing the ISO format, which is immediately mounted as a disk in Windows. ISO files can also be used to make bootable CD-ROMs, as well as to install an operating system or virtual machine. It also includes an LNK (shortcut file) for launching a DLL (Dynamic-link Library).
Let’s take a look at an e-mail originating from an IP address in Belize, at 179[.]60[.]150[.]96. It forges the originating e-mail address to look to have been sent from another Ukrainian fuel provider. The e-mail comprises both English and Ukrainian sections and appears plausible, considering the mention of further security measures for the attachment.
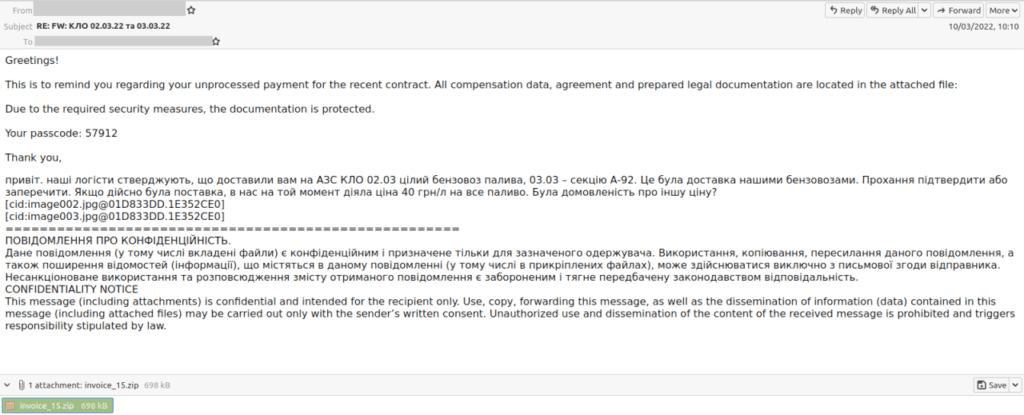
Figure 4. Phishing e-mail. (Source: Fortinet)
Attached to the e-mail is a file named “invoice_15.zip”. Extracting the Zip file will drop “invoice_15.iso” and begin the first phase of infection.
In either of the cases, once the iso is dropped, the process remains the same. The rundll32 program is used to load the downloaded.dat file. The rundll32 program then executes a series of commands linked to the following information-stealing capabilities:
- Machine discovery
- Obtaining machine AV info
- Getting IP and system information
- Domain information
- Dropping SQLite for accessing credentials stored in browser databases
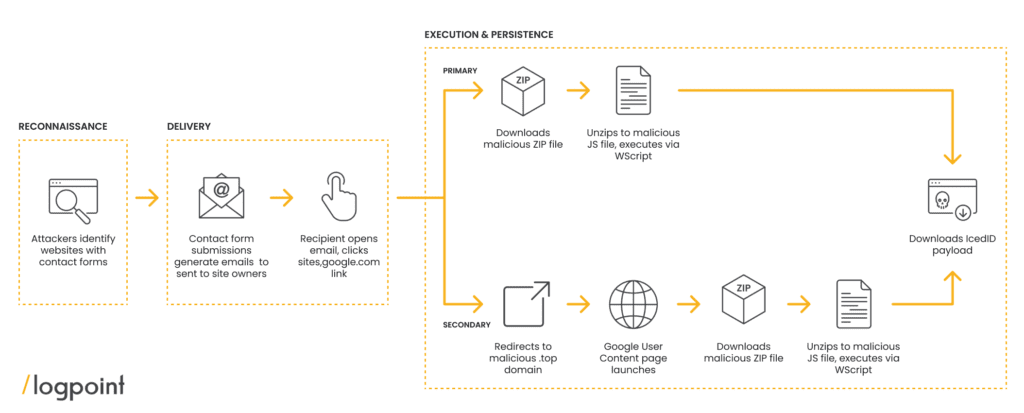
We go deeper into the post-initial-attack phases later in the report, but the diagram (below, figure 5) provides a broad flow of how attackers carry out these malicious email campaigns, starting from identifying the contact forms of the targets and ending with the IcedID malware payload.
Under the execution and persistence stages, we discovered a primary and secondary attack chain. The principal attack chain follows an attack path that begins with the download of a malicious.zip file from the sites.google.com link and ends with the IcedID payload. The secondary attack chain, on the other hand, appears to be a backup assault flow for when the original attack chain’s sites.google.com page has already been taken down.
Users are led to a .top domain in the secondary chain while unintentionally browsing a Google User Content page, which downloads the malicious.ZIP file. According to further investigation, the forms contain malicious sites.google.com links that automatically downloaded the IcedID malware into the victim’s devices.
When IcedID is launched, it connects to a command-and-control server to download modules that allow it to perform its primary job of gathering and exfiltrating banking passwords and other information. It provides consistency through planned tasks. It also downloads implants such as Cobalt Strike and other tools, allowing remote attackers to do malicious activities on the compromised system such as gathering new credentials, moving laterally, and delivering secondary payloads.
Adding legal threats to social engineering tactics
This campaign is successful because it uses valid contact form emails and because the message content appears to be something recipients would expect to receive, increasing the likelihood of attackers successfully delivering emails to inboxes, allowing “safe” emails that would otherwise be filtered out into spam folders to be delivered.
In the cases we found attackers also utilized legal threats as a scare technique. They alleged that the recipients used their photographs or graphics without their permission and that legal action will be taken against them. The email also conveys a sense of urgency, with terms such as “you could be sued” and “it’s not legal.” Everything else about this email is genuine and respectable, which indeed is a clever and devious approach.
We discovered further emails sent by attackers using different contact forms with similar wording about legal threats. The communications almost always include a copyright claim enticed by a photographer, illustrator, or designer, with the same desire to click the sites.google.com link.
Defending against sophisticated attacks through a coordinated defense
Attackers are still motivated to create novel ways to distribute malicious emails to organizations to avoid detection. The instances we observed provide a significant peek into how sophisticated strategies have evolved while still delivering malware payloads like IcedID. Their use of submission forms is of interest because the emails lack the traditional hallmarks of malicious messages and appear authentic.
It is not just the delivery method that is complicated but the action of the malware itself. IcedID, a prominent malware is now being used as an initial access payload, leading to more complicated and devastating post-compromise attacks. For us, defending the cyber infrastructure, we have to be a step ahead of the threat actors and possess multiple tools working alongside each other. Firewalls, XDRs, antiviruses, and Privilege Access Managers all have to actively be used, patched, and monitored using a centralized monitoring system with effective alerts, automated actions, and dashboards.
Of course, the Logpoint Converged SIEM solution, including SOAR and machine learning capabilities, and backed by industry experts monitoring the threat landscape for new attacker tools and techniques provides a helping hand.
Expert monitoring is especially critical in detecting this campaign given the delivery method and the nature of the malicious emails. By leveraging Logpoint queries, out-of-the-box alerts, search templates, and playbooks, with the attached in-depth report and side-by-side manual hunting in Logpoint, customers can proactively locate threats related to this attack.
We also encourage customers to continuously build organizational resilience against email threats by educating users about identifying social engineering attacks and preventing malware infection. Using in-house social engineering attack scenarios, user awareness training, and empowering employees to recognize and report these attacks will be crucial steps to effectively stop IcedID or any ransomware attacks.
As for IcedID, we go into a lot of detail on how the threat actors have been operating, and the Tactic, Techniques, and Procedures(TTPs). We uncovered multiple files, domains, and botnet networks that are still active in the wild. All artefacts are provided as lists and the associated alerts are available to download as part of Logpoint’s latest release and through Logpoint’s download center.
Logpoint Emerging Threats Protection Service provides the service subscribers with customized investigation and response playbooks, tailored to your environment. Contact the Global Services team here.
The report containing the analysis, infection chain, detection, and mitigation using Logpoint SIEM and SOAR can be downloaded from the link below.