Updated April 2023
Security practitioners should not assume that they can thwart all security breach attempts and should plan for the eventuality that some will compromises will occur. The primary goal of a security practitioner should instead be to try to be able to detect and recover from security breaches as quickly as possible in order to minimize their impact.
In order to accomplish this, we should leverage the principle of defense in depth and use overlapping controls to minimize single points of failure. We should take a risk-based approach to security understanding first where our most critical assets reside, where the greatest risk lies, and allocating our resources accordingly to protect them. Preventive controls should be leveraged where possible, but detective controls should be used where prevention is not feasible.

The detection challenge
The fact that digital resources are based on software means that log data is often readily available and with addition of a SIEM, we can essentially put a detective control on every device or application that can produce a log.
We can leverage threat intelligence for lists of known IOCs (Indicators of Compromise) to aid in detection of threats. This approach has been used successfully for decades with tools like AV, IDS, Spam filters etc, however this approach comes with some challenges.
First, the universe of threats is ever-expanding which means we will always have new IOCs to look for in addition to the old ones resulting in challenges around maintaining increasingly long lists of IOCs. Additionally, adversaries can easily modify certain attributes of the attack such as the source IP of network-based attacks or even just a single bit within the malware code so that its hash will no longer match with existing IOCs.
Most importantly, while this approach is fairly effective for known threats, it relies on somebody having previously seen and created a signature for those threats, so it doesn’t work for 0-day exploits or unknown threats.
When we contemplate a detection strategy, we want to consider both known and unknown threats. Knowing that we have to rely on detective controls how can we detect unknown threats?
Seeing the forest for the trees
Behavior analysis in security is a methodology for threat detection which prescribes a focus on understanding the behaviors of users and entities (servers, fileshares etc.) within your environment as well as the behaviors of your adversaries including their motivations and methods. With this understanding, you can detect potentially malicious activity not only by being able to identify known adversary behavior but also by being able to detect subtle changes in the known behaviors of the users’ and of the entities in your environment which could be the by-product of malicious activity.
Behavior analysis differs from traditional IOC detection in that it dictates that you use a big-picture, macroscopic perspective of your environment versus the microscopic view when you focus only on signature detection. This approach mitigates one of the primary challenges of traditional signature detection as it relates to managing the ever-expanding list of known-bad items you have to look for. With behavior analysis you can focus on a finite number of known adversary behaviors versus an infinite number of signatures with traditional signature-based methods.
The other key advantage of behavior analysis compared to traditional signature-based detection methods in security is that it is effective for unknown threats in addition to known threats because changes in behavior can serve as an indication that something is awry even when that behavior has never been seen before.
Tracking adversary behavior is difficult
Looking at your environment through the lens of behavior is in some respects more challenging than simply hunting for signatures of known malware, however doing so can be much more fruitful. This idea was first proposed by David Bianco, an incident handler with FireEye back in 2014 who described what he called the “Pyramid of Pain”.
The pyramid represented the comparative strengths and weaknesses of using various IOCs across two dimensions: a stack ranking of various IOC types in terms of how easy they were to implement and the relative size of the universe of each IOC type. At the bottom of the pyramid were hash values which are abundant and easy to detect and at the top of the pyramid were TTPs (tactics, techniques, and procedures i.e behaviors) which are far less abundant and also the most difficult to detect and track.
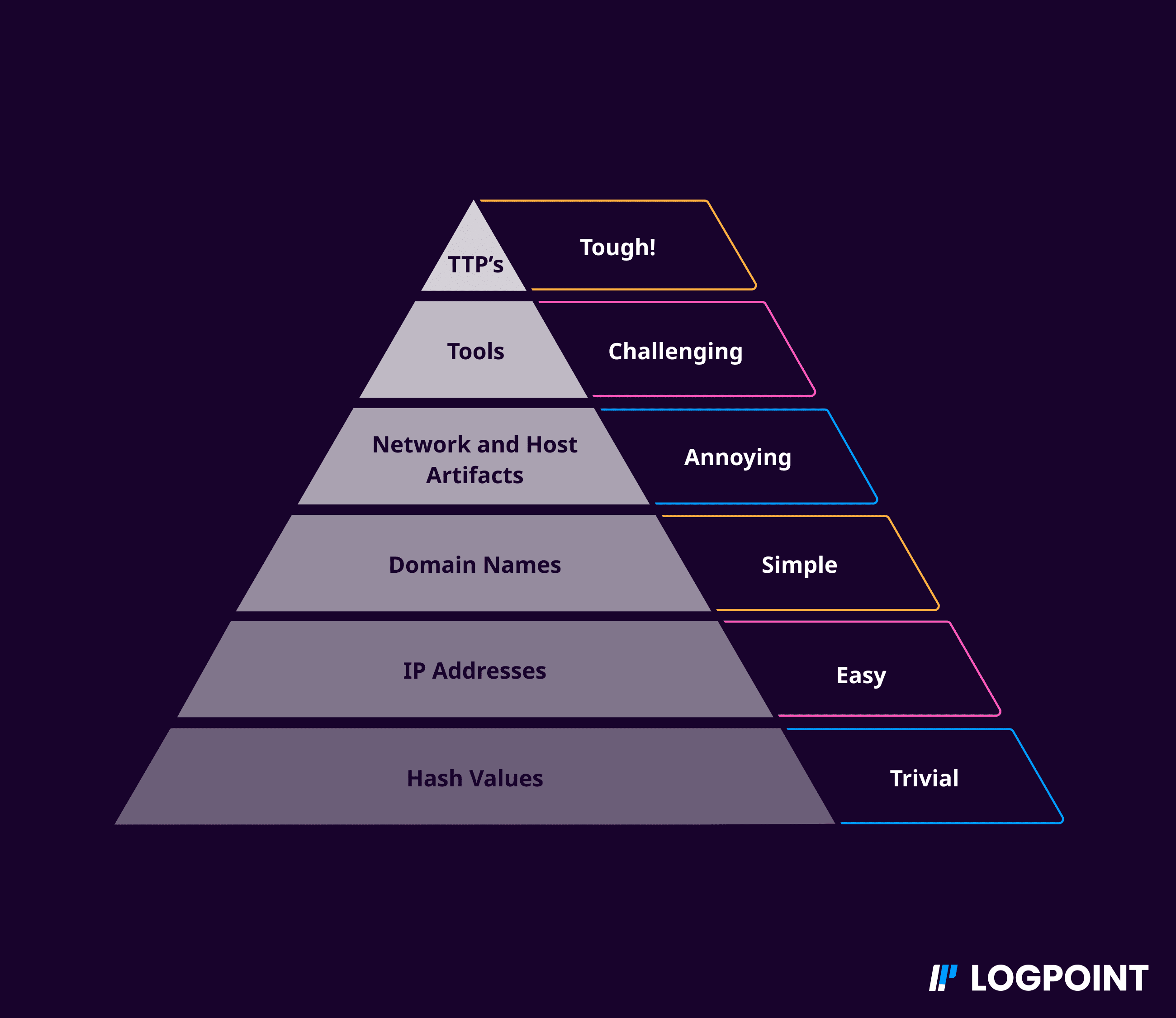
Source: Pyramid of pain, David J. Bianco
Although it is trivially easy to detect file hashes of known malware samples, it is likewise trivially easy for an adversary to change the hash value of a piece of malware simply by changing a single bit in the code. This makes it very easy for adversaries to slip malware past defenses which rely on signatures.
Fortunately the correlation between the difficulty to implement detection and the difficulty for an adversary to alter an IOC holds true as we move up to the top of the pyramid. This means that although it is difficult to track adversary behaviors, it is also very difficult for adversaries to change those behaviors and there are also far fewer of them to track versus files hashes.
We can infer that while a defense-in-depth strategy is a best practice, the controls that are implemented at the top of the pyramid should be more effective than the ones at the bottom and we should attempt to implement them where it is feasible. This of course begs the question: how can we start to implement behavioral methods in our security program?
Below I will discuss two ways that Logpoint can help you to implement behavioral analysis into your security program: leveraging the MITRE ATT&CK framework and leveraging User and Entity Behavior Analytics (UEBA).
MITRE ATT&CK
MITRE ATT&CK® is a community-sourced knowledge base of adversary tactics and techniques based on real-world observations maintained by the MITRE corporation, a private not-for-profit organization funded by the US government to conduct research in cybersecurity. The ATT&CK knowledge base is used as a foundation for the development of specific threat models and methodologies in the private sector, in government, and in the cybersecurity product and service community.
The ATT&CK framework enables security teams to leverage a wealth of adversary knowledge that has been collected by thousands of security researchers across the globe and helps them to both prepare for and react to cybersecurity threats. Integrating ATT&CK in detect and response programs allows security teams to see patterns of adversary behavior in seemingly benign activity.
By aligning its products with the ATT&CK framework, Logpoint takes advantage all of the known methods of detecting and tracking various tactics, techniques, and procedures used by adversaries. Logpoint can leverage behavior signatures from open-source projects such as the Sigma SIEM project. Logpoint users can overlay detections onto the framework to better understand potential vulnerabilities in their defense and to predict potential next steps of their adversaries.
Understanding your environment
While the Mitre ATT&CK framework enables the outside-in approach of understanding your adversaries’ behavior, Logpoint UEBA provides the inside-out approach to behavioral security of understanding your environment so well that you can detect subtle changes that could be the result of adversary behavior.
UEBA uses unsupervised machine learning to complement the traditional rules-based and signature-based detection capabilities of the SIEM. UEBA models the behavior of each user and entity in your environment at various times of the day, days of the week, and weeks of the month. It then uses those baselines as a basis for detecting anomalies to which it can apply heuristic algorithms to determine the likelihood that the observed differences in behavior could be indicative of a threat
Unsupervised machine learning can also be used to group together users and entities that have similar behavior. These peer groupings can be very important for improving the accuracy of detection because in addition to comparing an individual entity’s behavior to its own baseline, you can also compare an entity’s current behavior to the baseline of its peer group. This comparison reduces the chance for false positives in situations when a user does something new which is otherwise a very common thing to do among his/her peers.
Transforming raw data into actionable intelligence
At its core UEBA is based on using data science to leverage statistical approaches to detect anomalies, though we can’t expect that our security analysts are also data scientists. The challenge then comes in making sense of these anomalies and providing context and domain expertise around them that a security analyst can act on. Rather than simply alerting the analyst to an anomalous event without any context, LogPoint is able to provide actionable information in very clear and unambiguous terms.
Tune alerts with risk scores
Logpoint’s UEBA provides two benefits: first it detects anomalous behaviors and makes a disposition as to whether they are suspicious or legitimate with high degree of certainty. This analysis is based on understanding context and is difficult if not impossible to automate using non-behavioral methods.
The second benefit of UEBA is that it assigns a risk score to each user and entity in the organization which corresponds to the number and severity of anomalous events with which that user/entity has been associated.
These risk scores an additional dimension to rule-based analytics throughout the SIEM. So instead of being alerted whenever any user does something which could be innocuous or malicious such as accessing a file-sharing website, a smarter alert can be configured to only alert when users with high-risk scores access the file-sharing website. This ultimately results in an increase in the fidelity of alerts with lower false positives and false negatives.
Behavioral analysis reduces attacker dwell time
Because of the principle of defense-in-depth, there will always be value in leveraging overlapping controls which means that there will continue to be value in leveraging traditional signature detection methods such as IDS, blacklists, and anti-virus as they can be very effective for filtering out known-bads and they are relatively easy to implement.
However, with detective controls, we must be mindful of the fact that too many alerts from too many controls can distract and overwhelm the limited resources of our security teams. In order to reduce the dwell time of an adversary we need ways to filter out the noise and bring the attention of our security teams to what’s most urgent at that moment. Traditional signature-based detection methods alone are not good enough. Behavioral analysis in security can complement these approaches and fill many of the gaps that these approaches create.
Logpoint provides two ways of implementing behavioral techniques: First, with its alignment to MITRE ATT&CK, Logpoint enables an easy way to better understand and detect the behaviors of adversaries. Second, UEBA provides another complementary behavioral analysis security technique by helping security teams to better understand when something out of the ordinary could be an indication of a compromise.
Together these two approaches along with best-in-class log collection and analytics enable organizations to process billions of security events and thousands of alerts into a prioritized, manageable list of a handful of security incidents. LogPoint’s mission is to enable security teams to quickly detect and respond to threats in order to minimize the amount of time adversaries can spend in the environment and the damage they can cause.






