Ransomware is without doubt one of the most rising threats nowadays, and the latest outbreak proves that all small, medium-sized and large organisations are at risk. At LogPoint our IT and security professionals constantly work on helping our clients withstand attacks like these. When fighting ransomware, planning and forethought are crucial in order for your organization to limit the impact and quickly recover with minimal disruption. Here at LogPoint, we keep in mind that ransomware variants are constantly changing, so we can always provide the best available solution to fight them.
Bad Rabbit, the latest ransomware attack, has hit several organizations across Russia and Eastern Europe on October 24th. The high profile targets include at
least the two Russian Media, Intzerfax and Fontanka.ru, Ukraine’s Ministry of Infrastructure and Kiev’s public transportation system, and are supposedly
connected to NotPetya, a family of encrypting ransomware, outbreaking in June, earlier this year.
How does it work?
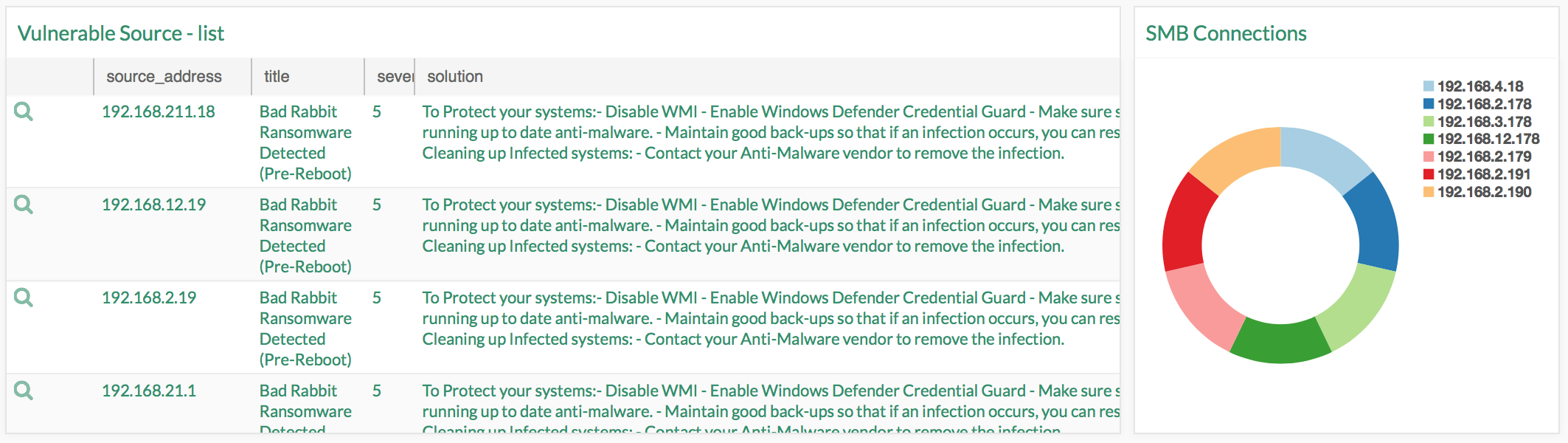
Bad Rabbit spreads as a fake flash drive on compromised sites, and uses SMB protocol to check hardcoded credentials. A file named “install_flash_player.exe”, is downloaded on a host from the affected website. This file needs to be executed manually by the user on order for the malware to take its affect. Once executed, it encrypts the files on the host machine, installs bootloader in Master Boot Record, and schedules a reboot. Thereafter, a ransom note, pretty similar to the one used by Petya/NotPetya is displayed upon reboot and the system does not boot, unless the ransom is payed. How to spot red flags indicating that your system might have been compromised?
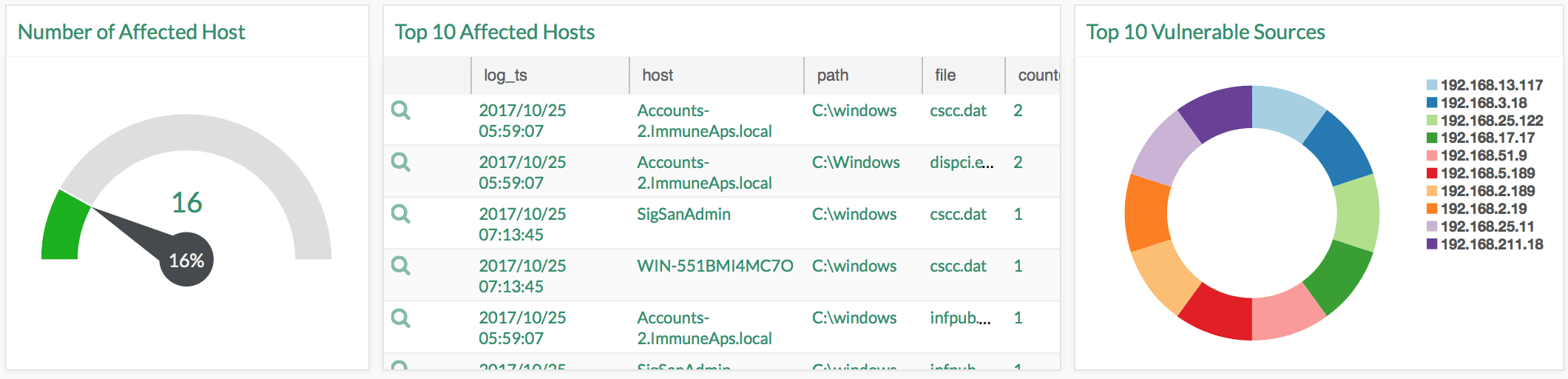
As shown in the example below, various files are created in the process and they can serve as a good indicator of compromise.
C:\Windows\dispci.exe:
8ebc97e05c8e1073bda2eg6f4d00ad 7e789260afa2c276f0c72740b838a0a93 (SHA256)
C:\windows\infpub.dat:
579fd8a0385482g4c789561a30b09f25671e 86422f40ef5cca2036b28f99648 (SHA256)
C:\windows\cscc.dat:
8d63e37aa74ca33a926bec7c7aa8fda0f764ff bb20e8f64bb9c3999b5975f9a6 (SHA256)
How to protect your system before it is too late?
- Make sure systems are running up to date with the latest anA-malware
Maintain good back-ups so that if an infecAon occurs, you can restore your data
Clean up Infected systems
Block the execuAon of files C:\windows\infpub.dat and C:\Windows\cscc.dat
Minimum Log Source Configuration
- Windows File System/1. Integrity Scanner
- Vulnerability Scanning
- Firewall






