Logpoint as a cybersecurity solution
It has never been more lucrative – and in some cases, never easier – for cyber criminals to target enterprises than today. With the advent of employees working from anywhere across multiple devices, there are more opportunities for your critical business data to be exposed. Further, the diversity and accessibility of digital and new media is placing data and other resources at more risk for compromise.
And as we’ve seen, data breaches can result in significant financial and reputational damage. What’s clear is that your enterprise cybersecurity solution must not only protect your network – it should prepare you to proactively reduce risk before a small problem becomes a big one.
Holistic cybersecurity
As a CISO or CXO, you know that implementing perimeter, endpoint and access control security measures are excellent first steps to reducing the risk of damage, disruption and misdirection. But you can’t stop there. Effective cybersecurity strategies also have to take into account the very real possibility that systems can be compromised, regardless of security implementation.
This necessitates a solid holistic view of your infrastructure, including real-time insights facilitating vulnerability management as well as a reporting structure supporting accountability in compliance. Logpoint’s SIEM & SOAR solution can help you fill in those gaps.
The power of troubleshooting
Our Modern SIEM & SOAR solution will arm you with a cybersecurity analytics engine that allows you to easily identify attacks, immediately respond and effectively report them. Logpoint acts as a force multiplier for security analysts by ensuring the safety of critical business intelligence.
With Logpoint, you can quickly troubleshoot potential issues via:
- Rapid analytic insight into incidents across the infrastructure
- Removed dependencies of specific personnel with restricted system access
- Big data analytics for sharp, easy analysis of all issues and incidents related to production applications, databases and RFID environments
- Reduction of the number of false positives and eliminating the hassle of maintaining and developing expert rules
- Forensic investigation with the execution of custom playbooks should an incident arise
Valuable insight and analysis for cybersecurity
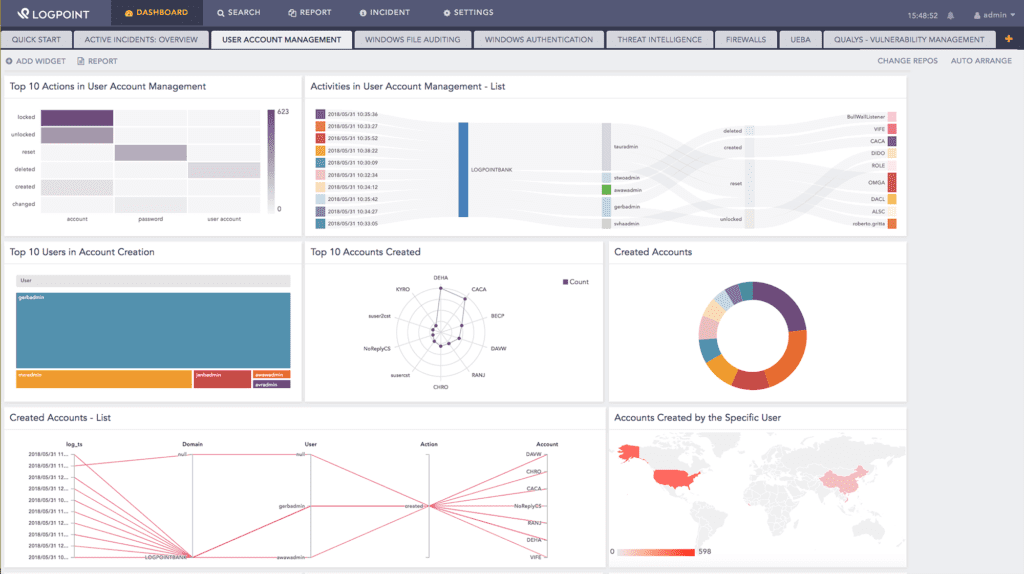
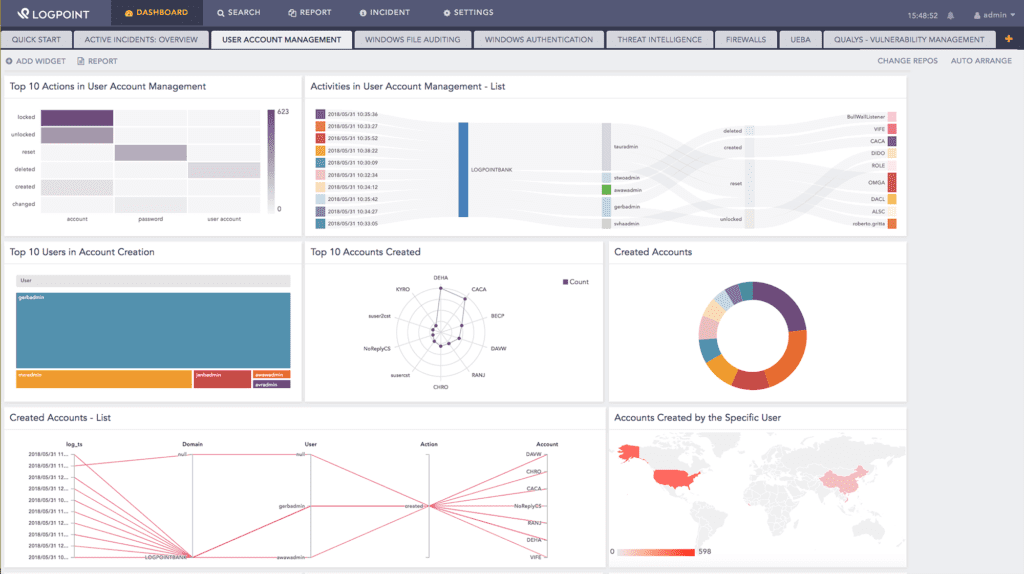
While information security is a complicated task, your ability to receive and analyze activities should be seamless and simple. That’s why Logpoint generates concise, detailed statistics and alerts, effortlessly produced reports and easily configured dashboards reports for effective cybersecurity monitoring.
With Logpoint’s cybersecurity monitoring you’ll have a clear overview of relevant security information right at your fingertips. This ensures that malicious or fraudulent activity isn’t only discovered, but it can be immediately handled before the damage is done.
Tip: Read our guide about the top 10 SIEM & SOAR use cases and behaviors that Logpoint can detect in your infrastructure.
SIEM & SOAR cybersecurity monitoring
The proactive cybersecurity monitoring gives you:
- Easy-to-use centralized management, analysis and event reporting across your enterprise
- Real-time, actionable insights from raw machine data
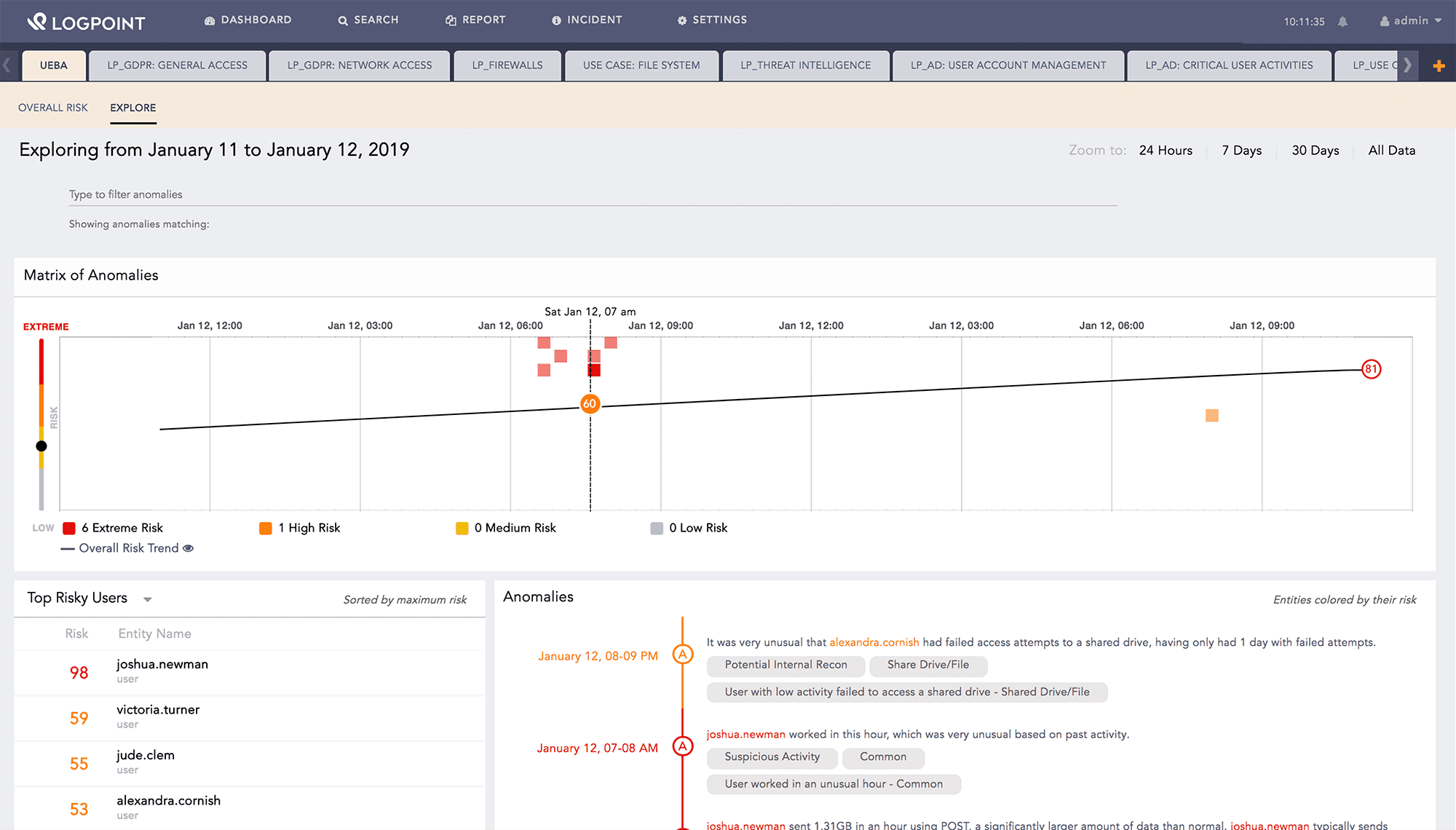
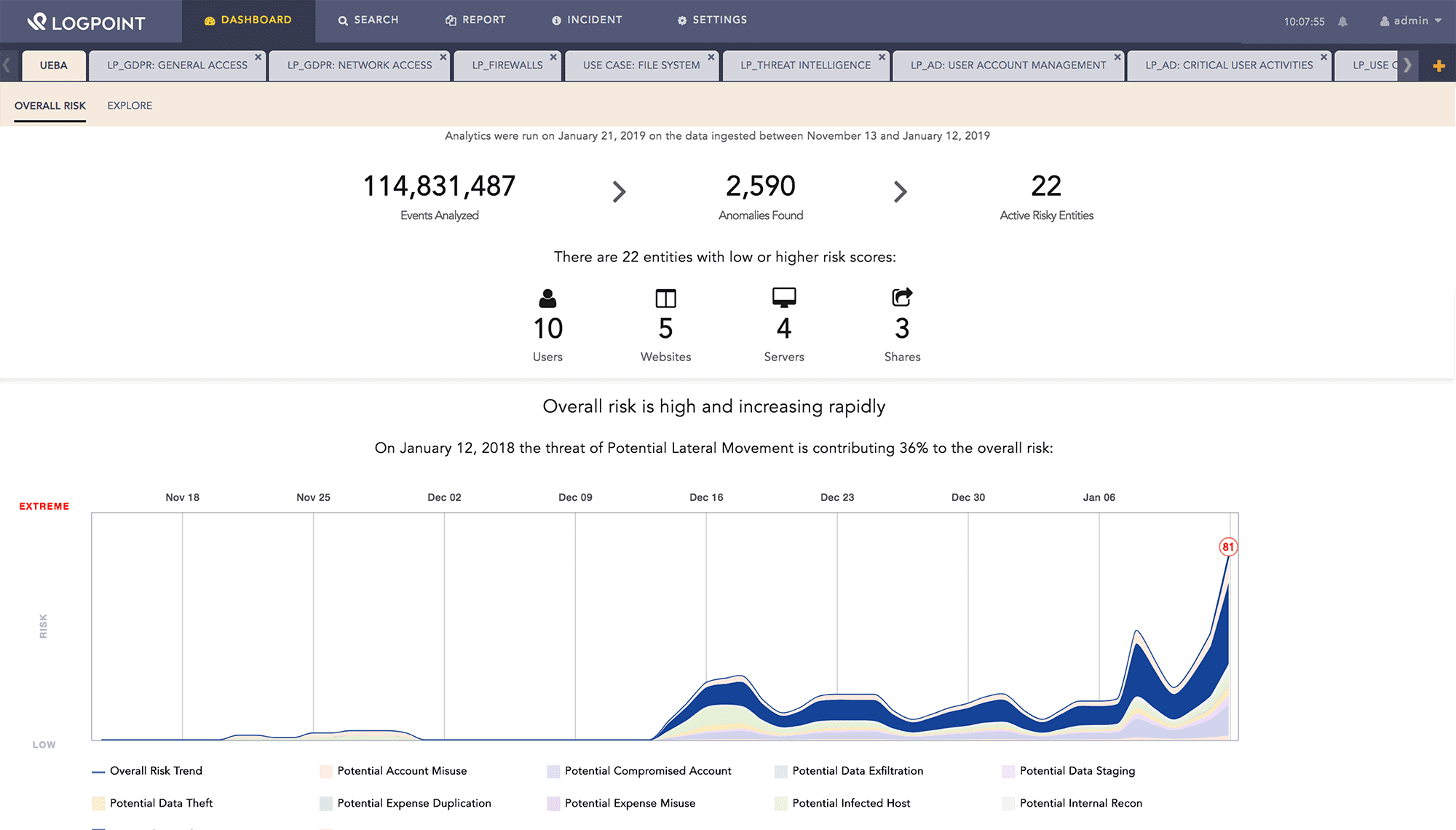
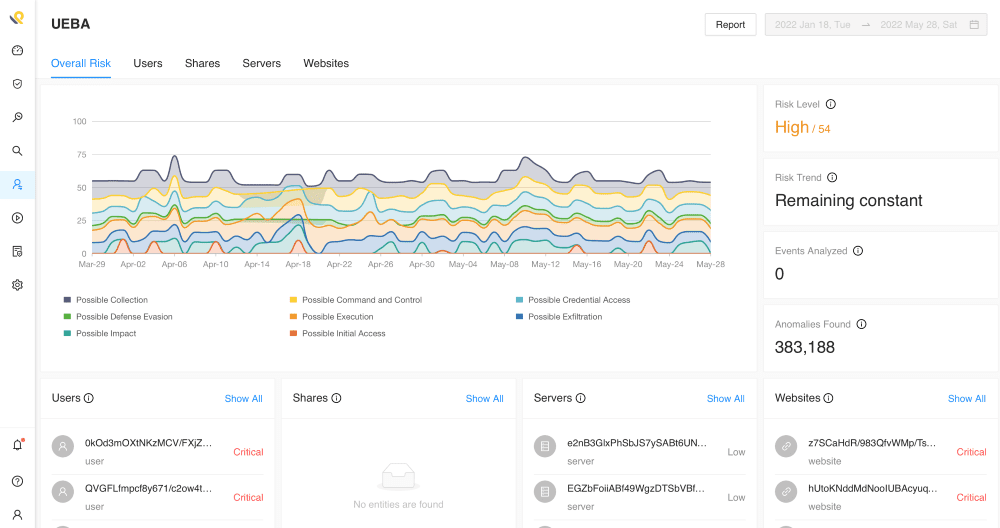
- Automatic detection and alerting of critical incidents on your systems, allowing you to locate unusual patterns and identify threats
- Visibility into unauthorized network or system access and attacks intended to compromise the availability of networks and systems
- Detection of potentially malicious actions by employees or others with corporate network access
We also fulfill compliance and regulatory requirements, including auditing guidelines, ISO standards, UK GPG13 and the European Union’s GDPR.

Trust Logpoint
SIEM cybersecurity is one of the cornerstones of any holistic solution, and our Modern SIEM and big data analytics solution offers unprecedented performance, scalability and flexibility. You can deploy Logpoint on premise and in the cloud, and it’s designed for both in-house cybersecurity departments as well as managed security service providers (MSSPs).
Logpoint delivers the most flexible and easy-to-use platform for collecting, analyzing and monitoring your machine data, whether generated by applications, databases, infrastructure, sensitive assets, manufacturing systems or security systems.
By combining, extracting and enriching data from multiple sources, our information security services can provide you with unique analytic capabilities and insights, smoothly presented in use-case oriented, out-of-the-box dashboards and reports.