Logpoint’s SIEM system – How it works
SIEM, standing for Security Information and Event Management, is the process of ingesting log data from disparate systems and then correlating that data to try and find indicators of compromise/attack or patterns of behavior. The only issue with this approach has been the highly technical nature of implementations, leading to a large swathe of companies forgoing a key managed network security tool.
The Logpoint’s SIEM system is designed from the ground up to be simple, flexible, and scalable, providing streamlined design, deployment, and integration tools to open the use of a network security tool up to all businesses. This means that the architecture can be continuously extended with additional functionality without the need for a full major release, to continue to support your business’s growing and changing needs.
The Logpoint system is built on a set of specific tenants:
- No company should be limited by the amount of data they can ingest into a SIEM system
- Simplified architectural principles to enable faster and more efficient software deployments
- World-class support available 24×7 to help customers get the most value from their SIEM system
At Logpoint, we have years of experience in SIEM implementation and sizing customer installations in all ranges correctly. Based on our experience, we have developed a simple Logpoint SIEM sizing calculator to help you estimate the EPS and GB/day.
Logpoint Architecture
Logpoint SIEM software for managed network security can be broken down into three main modules that deliver the functionality typically expected from a SIEM system. These components can be delivered within a single physical appliance or split up across as many physical/virtual servers as makes sense for the business needs.
The modularization of the individual components within Logpoint allows customers greater flexibility when deciding on the SIEM architecture that works for their organisation. Smaller networks may wish to emphasize simplicity of design through the deployment of all components within a single virtual appliance, whilst larger networks can split the components across various network zones to reduce the potential load on the network.
The three main components of the Logpoint platform are:
LogPoint Collectors – The ingestion component of the LogPoint system
Collectors are responsible for the ingestion, normalisation and enrichment of log data from disparate log sources into the LogPoint platform. This is achieved with LogPoint’s single taxonomy and compiled plugins that normalise any log file into LogPoint’s standardised key/value pair format for long term storage. By normalising the log data upon ingestion (rather than upon search) LogPoint can significantly speed up the search and correlation process.
There are hundreds of plugins available out-of-the-box when deploying the LogPoint software, further simplifying the process of log ingestion by taking away the hassle of configuring these yourself. Indeed, if there is a commercial-off-the-shelf (COTS) product that LogPoint doesn’t have a plugin for, LogPoint will commit to getting this written for customers as part of the normal support process.
The Collector architecture also provides full data-enrichment capabilities, meaning that gathered events can be correlated with external metadata for contextual analytics. For instance, LogPoint can be used to correlate Threat Intelligence feeds against any collected data source or correlate incidents with CMDBs to quickly target pinpoint locations of devices. Any structured data can be used to enrich the collected data. These capabilities increase performance and accuracy of analytics through ingest-time enrichment, without the need to import and fragment existing data.
Alongside the Collector, LogPoint provides the LogPoint Agent which enables the transmission of encrypted log data, system and integrity monitoring of log sources and fetching log data from sources that may not have an easy method of data transmission natively to the network security tool. The LogPoint Agent can be implemented and managed from a central LogPoint server to simplify the dissemination of the functionality across the customers wider network.
LogPoint Backend – The storage component of the LogPoint solution
The Backend of the LogPoint system is a NOSQL-based storage solution, which means that all data is stored in flat file, enabling searches that take seconds. This architecture is then split down into individual repositories, defined by the customer, as best suits business needs.
These repositories (repos) can manage retention policies on an individual basis, meaning that sensible usage of repos can provide business with massive savings on storage infrastructure. The LogPoint platform even allows you to automatically migrate data within repo onto different storage tiers as the data becomes older, until such a time as the data is no longer required, when it can be automatically deleted.
Finally, access control is integrated into the system so that administrators can control which of their security analysts can view which repo. This can be particularly useful in environments where customers wish to store log data but want to restrict correlation of that data to a few trusted employees (such as HR records).
LogPoint Search head – The analytics component of the LogPoint managed network security system
The Search head is where customers will develop the custom content that extracts value from that raw and normalized log data. The built-in log analysis engine will use this content to automatically detect and alert on critical incidents on your systems. Events monitored can be very diverse and can, for example, include an ongoing attack, a compromised system, malicious insider activity, performance degradations, and much more.
To enable your organization to create value fast, LogPoint offers several preconfigured configurations based on 400+ Use Cases, allowing your team to orchestrate analytics and playbooks, without the hassle of countless hours of professional services.
Analysts produce content (dashboards, alerts, reports) through the search function of the LogPoint portal, which takes advantage of the single taxonomy to simplify the process. Everything stored within the LogPoint backend can be searched using the same key/value pair identifiers, this means that even in the case of new functionality being released by LogPoint, all of the existing content will continue to work as initial intended.
Within LogPoint, events can trigger alerts, but can also be configured to trigger an incident. Incidents within LogPoint can be assigned Risk levels, then assigned to a user. This can then be used to jump to the data that has triggered the incident directly through the GUI. Once the incident has been investigated, the analyst can either comment, resolve, close or re-open the incident.
Finally, to further enable the segregation of data, it is possible to assign the four eyes principle to individual key/value pairs within logs through the implementation of Data Privacy mode. In LogPoint any field that can be used to identify a given user may be encrypted/obfuscated when presented to the GUI in a way that no analyst can see the original data. The analyst can still run queries, view dashboards and reports etc. but the encrypted field-values will be shown and not the real data. If there is a requirement for the analyst to see the unencrypted data, the analyst can request time-based access from the companies nominated Data Privacy officer.
Logpoint Support
Logpoint’s support function, is a leader in providing fast and effective support to the Logpoint community, as proven by the leading review scores in Gartner’s Peer Insights awards. Alongside the standard support functions customers would expect the Logpoint support team offer additional assistance to ensure a smooth ongoing SIEM deployment for customers. This includes:
Plugin development
If customers need new log sources ingested and a plugin doesn’t exist, the team can commit to getting this developed within days. If the log source is a commercial-off-the-shelf product it is done as part of the existing contract.
Use case assistance
If a customer is not feeling particularly confident in the development of use cases, the support team are on hand to assist in translating a customer’s plain-text use case idea into the Logpoint search language.
Reports, dashboards, use cases
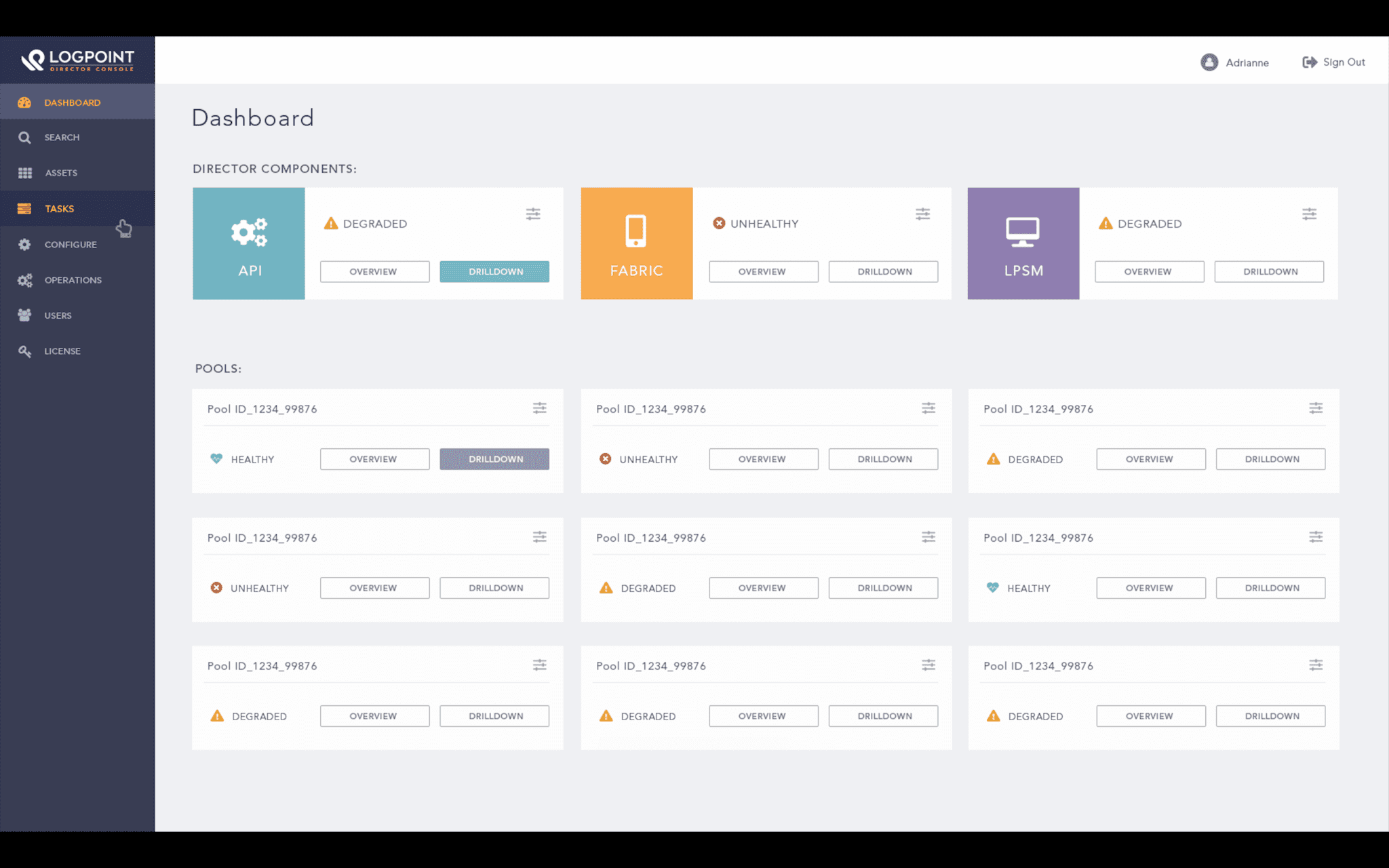
Logpoint Director for managed network security
Director is a multi-tenant component of the Logpoint managed network security tool, allowing customers (or MSSPs) to manage large scale environments in segregated “Logpoint Pools” comprised of the three mentioned above Logpoint modules in whatever configuration is required.
Logical segregation of these pools allows customers to limit both visibility and long-term storage of data to only the analysts and regions where that data should be held. Examples of this could include limiting the storage of German log data to a pool specifically hosted within Germany.
Key Logpoint benefits
Single taxonomy
Logpoint ensures single taxonomy for normalisation of log data, enabling an easy-to-use search function for the creation of dashboards, alerts and reports. By translating all log files into a simplified single taxonomy, searching across a wide variety of log sources is made easier and more efficient.
Simplified role-based access control
Administrative user access is bound into AD via LDAP for ease of permission definition. Group permissions to the system are aligned with a role based approach to administrative rights, giving full control over access to both the log repositories and the dashboard usage.
Full HA deployment
The Logpoint HA architecture allows synchronisation of both index and event data in a fault tolerant fashion, providing a robust integrity to the data storage. Any recovery has a very speedy recovery point objective whilst the platform operates in failover mode.
Agile platform design
The LogPoint system is agile in design with an intuitive interface, built for administrators with network security tool experience or ad-hoc users alike.
Flexible / scalable architecture
LogPoint architecture is entirely flexible and scales linearly for large and complex implementations. The network security tool can be deployed in either physical or virtual environments and on premise or in the cloud.
Unique license model
Fair and holistic license model, no hidden extra’s due to the transparent license structure. Adopting a node based model rather the EPS/MPS basis that many other SIEM vendors models follow for managed network security.
Data Privacy mode
By utilising Data Privacy Mode, it is possible to ensure the context of the log files can be included on multinational searches, without compromising the need to ensure the information remains secure. This functionality is particularly beneficial where data must remain in a region.
Streamlined normalisation architecture
Plugin architecture, enables dynamic development and custom enhancement. Being vendor agnostic, logs can be collected using varying methods and sources. If a plugin is not present prior to deployment, LogPoint, will create it. Development is not charged for commercial-off-the-shelf product.