by Nilaa Maharjan Logpoint Global Services & Security Research
What is SpoolFool (CVE-2022-21999)?
SpoolFool, also known as CVE-2022-21999, is a local privilege escalation flaw in Microsoft Windows’ print spooler service, which controls print operations. On all Windows platforms, the print spooler executable file (spoolsv.exe) is loaded by default upon system startup.
A user can construct a printer port that points to a file on a disk using the print spooler service’s capability. In order to build folders in the printer spool driver directory and load arbitrary DLL files from it, the SpoolFool vulnerability modifies the path of a printer port. This circumvents security checks found in earlier print spool privilege escalation vulnerabilities. A security check can be circumvented by an attacker by defining a universal naming convention (UNC) path, such as \\localhost\C$\spooldir\printers\ (where c:\spooldir is a symbolic link to C:\Windows\System32\spool\drivers\x64\), that allows arbitrary files to be written to the privileged directory and then loaded as DLLs by the print spool service and executed with administrative privileges.
This would provide the attacker a handle with the PRINTER ACCESS ADMINISTER right, which can be used to carry out other operations like DLL injection leading to but not limited to creating local admin users, which is depicted in the attached comprehensive report.
How bad is this?
| CVE | CVSSv3 Score |
|---|---|
| CVE-2022-21999 | 7.8 |
Severity: Critical
- Local privilege escalation
- Results in trivial ‘SYSTEM’ access on vulnerable systems
- Likely to be chained with other vulnerabilities, malware, and rootkits
Current situation: Exploited in the wild, proof of concept code publicly available.
Affected Systems:
- Windows Server 2012 R2
- Windows Server 2012
- Windows Server 2008 R2 for x64-based Systems Service Pack 1
- Windows Server 2008 for x64-based Systems Service Pack 2
- Windows RT 8.1
- Windows 8.1 for x64-based systems
- Windows 7 for x64-based Systems Service Pack 1
- Windows Server 2016
- Windows 10 Version 1607 for x64-based Systems
- Windows 10 for x64-based Systems
- Windows 10 Version 21H2 for x64-based Systems
- Windows 11 for x64-based Systems
- Windows 10 Version 20H2 for x64-based Systems
- Windows Server 2022 Azure Edition Core hotpatch
- Windows Server 2022
- Windows 10 Version 21H1 for x64-based Systems
- Windows 10 Version 1909 for x64-based Systems
- Windows Server 2019
- Windows 10 Version 1809 for x64-based Systems
Understanding the Vulnerability:
Introduction to Spooler Components
The Windows Print Spooler is a built-in component on all Windows workstations and servers, and it is the primary component of the printing interface. The Print Spooler is an executable file that manages the printing process. Management of printing involves retrieving the location of the correct printer driver, loading that driver, spooling high-level function calls into a print job, scheduling the print job for printing, and so on. The Spooler is loaded at system startup and continues to run until the operating system is shut down. The primary components of the Print Spooler are illustrated in the following diagram.
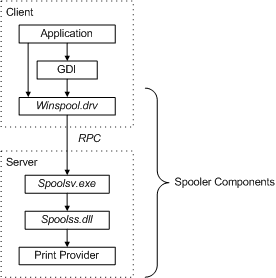
Introduction to Spooler Components – Windows drivers
Application
The print application creates a print job by calling Graphics Device Interface (GDI) functions or directly into winspool.drv.
GDI
The Graphics Device Interface (GDI) includes both user-mode and kernel-mode components for graphics support.
winspool.drv
winspool.drv is the client interface into the Spooler. It exports the functions that make up the Spooler’s Win32 API, and provides RPC stubs for accessing the server.
spoolsv.exe
spoolsv.exe is Spooler’s API server. It is implemented as a service that is started when the operating system is started. This module exports an RPC interface to the server side of the Spooler’s Win32 API. Clients of spoolsv.exe include winspool.drv (locally) and win32spl.dll (remotely). The module implements some API functions, but most function calls are passed to a print provider by means of the router (spoolss.dll).
Router
The router, spoolss.dll, determines which print provider to call, based on a printer name or handle supplied with each function call, and passes the function call to the correct provider.
Print Provider
The print provider that supports the specified print device.
Local Print Provider
The local print provider provides job control and printer management capabilities for all printers accessed through the local print provider’s port monitors.
The following diagram provides a view of the control flow among the local printer provider’s components when an application creates a print job.
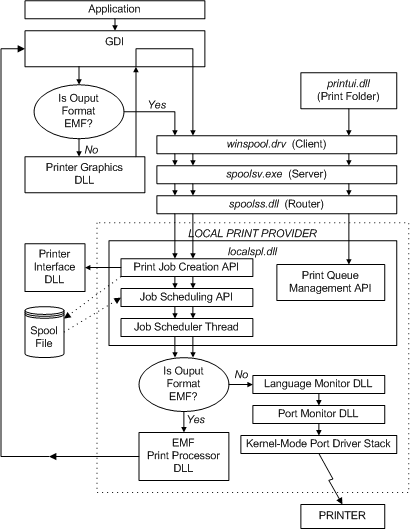
Introduction to Print Providers – Windows drivers
While this control flow is rather large, the blog and the subsequent report will focus on the local print provider localspl.dll.
Symbolic Link
A symbolic link, commonly referred to as a soft link, is a type of file that links to another file, much like a Windows shortcut or a Macintosh alias. In contrast to a hard link, a symbolic link does not contain the target file’s data.
It merely makes a reference to another file system location.
Due to this distinction, symbolic links are granted advantages over hard connections, such as the capacity to link to remote machines via NFS-connected directories or files. A target file’s contents are retained using hard links rather than symbolic links when the target file is removed.
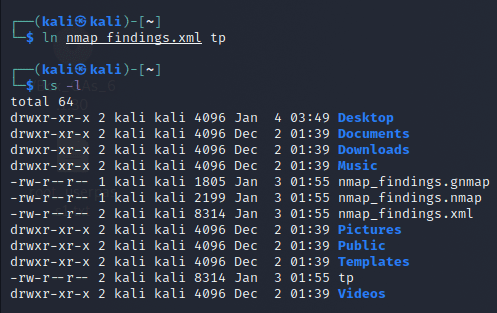
Fig-1: Created a Hard Link to a file
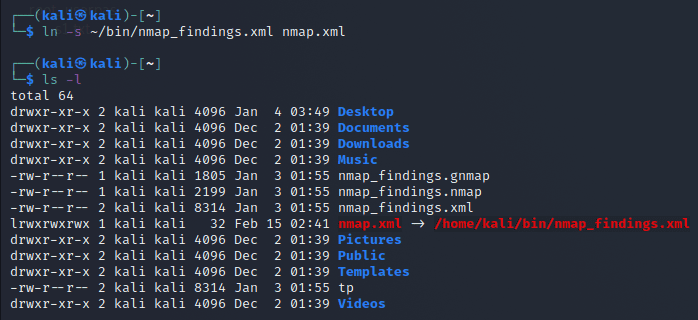
Fig-2: Created a Symbolic Link
CVE-2020–1048 and CVE-2020–1337, respectively, were fixed in May and August 2020. Microsoft addressed a separate issue in the Print Spooler in September 2020. In summary, by specifying the SpoolDirectory property on a printer, users were able to establish arbitrary and readable directories. What was the purpose of the patch? Before establishing the SpoolDirectory attribute on a printer, the Print Spooler would now verify if the user had permission to create the directory.
Global Exposure Analysis
Over 17000 instances are potentially vulnerable to this vulnerability, with South Korea and the United States being the top two on the list, according to a fast search in Shodan for “pjl” and port 9100. Pjl stands for Printer Job Language.
Note: Port 9100 is the port on which many printers run by default. Also, many machines found on Shodan are most likely honeypots. Even with the estimation, many of the systems are government or health industry systems that aren’t patched.
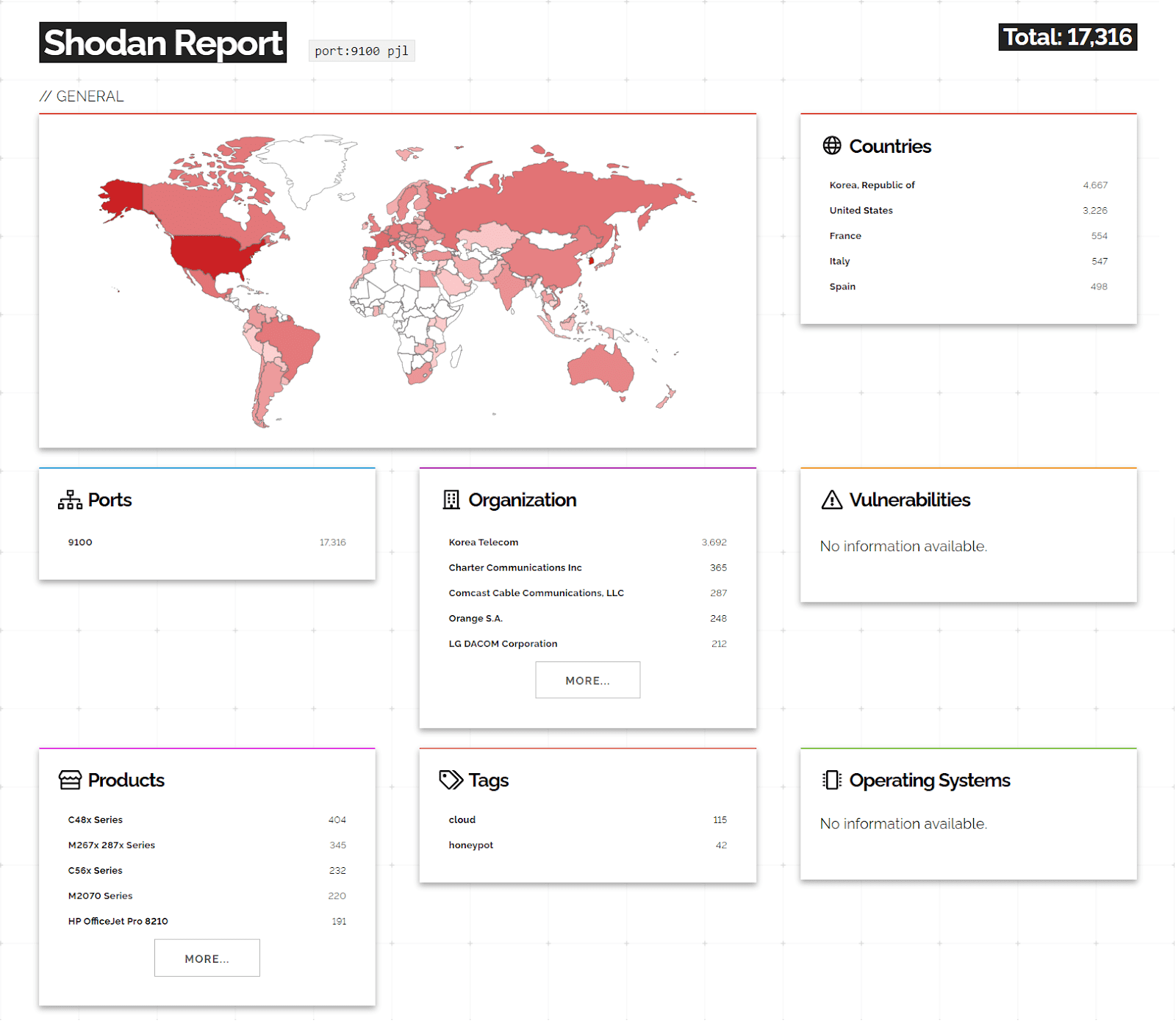
Heat Maps from Shodan Report
Stitch the Patch!
To prevent havoc with your print spooler service, Microsoft has provided updates, therefore update your systems as soon as possible. Patch Now!
That is all there is to it. Microsoft has issued an official fix. The Windows Error Reporting Service (WER) is misused to attack an arbitrary directory creation primitive, according to this article by Jonas L from Secret Club. The method, however, did not appear to operate dependably on a Windows 10 PC. The SplLoadLibraryTheCopyFileModule, on the other hand, is quite trustworthy, but it does presume that the user can operate a printer, which is already the case for this vulnerability.
Since the print spooler has been in the eye of this storm for some time, it seems unlikely that there will be any relief soon—at least, that’s what Oliver Lyan’s ominous “to be continued…” at the end of his story seems to suggest.
TL;DR
By specifying the SpoolDirectory attribute on a printer, a user is able to create any number of writeable directories. An attacker can build a remote printer and give EVERYONE the ability to manage it because a non-privileged user is permitted to add remote printers. This would provide the attacker a handle with the PRINTER ACCESS ADMINISTER right, which can be used to carry out other operations like DLL injection.
In the attached report, we will discuss the technical details of the associated CVEs(CVE-2022-21999, CVE-2020-1030, CVE-2020-1337, CVE-2020-1048) and methods through which an attacker can leverage and gain escalated privileges as NT AUTHORITY\SYSTEM.