Von Julien Soukhavong, Sicherheitsberater, November 16, 2016.
Rückmeldungen von korrelierten Ereignissen können für spätere Analysen äußerst nützlich sein.
Wie hoch war die durchschnittliche tägliche Anzahl der Geräte über drei Monate?
Wir könnten eine vollständige Suche über den gesamten Zeitraum durchführen, aber wenn wir dies regelmäßig sehen wollen, müssten wir eine umfangreiche Abfrage durchführen.
Stattdessen können wir die Ausgabe einer Suche als Eingabe für eine andere Suche verwenden.
Zum Beispiel: Wir zählen jeden Tag die Anzahl der Geräte und geben diese Zahl in einer Protokolldatei aus.
Jetzt müssen wir nur noch einen kleinen Datensatz (90 Tage oder den Durchschnitt von 90 Ganzzahlen) vergleichen.
Dies ist eine wesentlich kleinere Aufgabe.
In LogPoint können wir dies tun, indem wir Alert-Regeln erstellen.
Diese Alert-Regeln führen die Funktion aus, um das Teilergebnis zu berechnen (Aggregation).
Die Ausgabe der Alert-Regel wird mit Hilfe von Syslog-Benachrichtigungen zurück in LogPoint übertragen.
Im Folgenden haben wir die eingebaute Korrelationsregel zur Erkennung von Datenverkehr von bekannten bösen Adressen verwendet und diese Ergebnisse über ein sehr langes Zeitintervall aggregiert, indem wir das Feedback der Alarmregel an das Syslog verwendet haben.
Typische Anwendungsfälle könnten sein:
- Wie können Sie relevante Informationen aus unseren Sicherheitswarnungen gewinnen?
- Welche Quelladressen haben meine Sicherheitswarnungen erzeugt?
- Ist eine Quelladresse an mehreren oder verschiedenen Sicherheitswarnungen beteiligt?
Das folgende Verfahren zeigt Ihnen Schritt für Schritt, wie Sie eine Liste relevanter Daten aus generierten SIEM-Alarmen erstellen.
1. Erstellen oder aktivieren Sie einen Alarm
In unserem Beispiel werden wir den SIEM-Alarm verwenden:
” LP_Default Akzeptierter Verkehr von schlechter IP “
Syslog-Benachrichtigung einrichten
In diesem Beispiel erzeugen wir ein Syslog-Ereignis für den LogPoint-Server selbst:
Server/Anschluss: 127.0.0.1 Anschluss:514
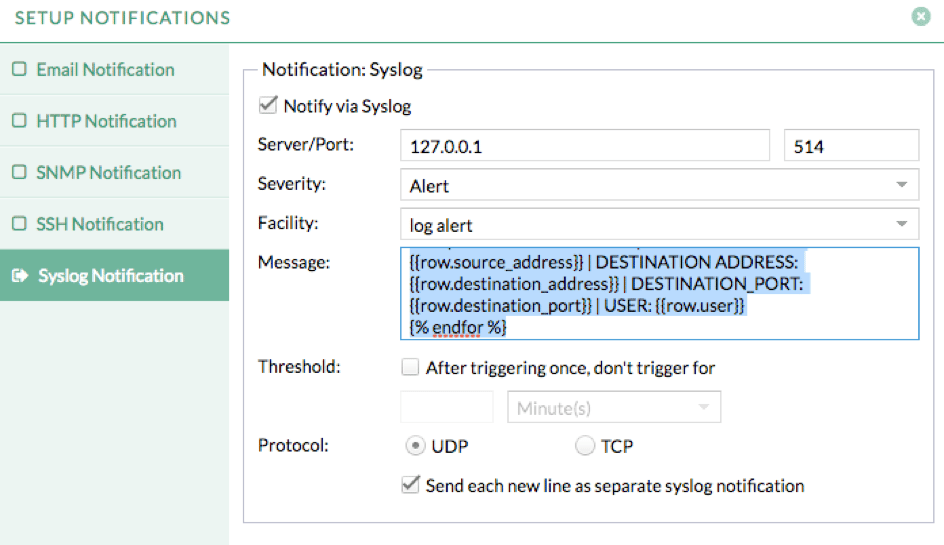
Im Abschnitt Nachricht werden wir einen Jinja-Code verwenden, um die relevanten Felder zu extrahieren, die wir in unserer Benachrichtigung anzeigen möchten.
{% for row in rows %}
Akzeptierter Verkehr von schlechter IP | SOURCE ADDRESS: {{row.source_address}} | ZIEL-ADRESSE: {{row.destination_address}} | ZIEL_PORT: {{row.destination_port}} | BENUTZER: {{row.user}}
{% endfor %}
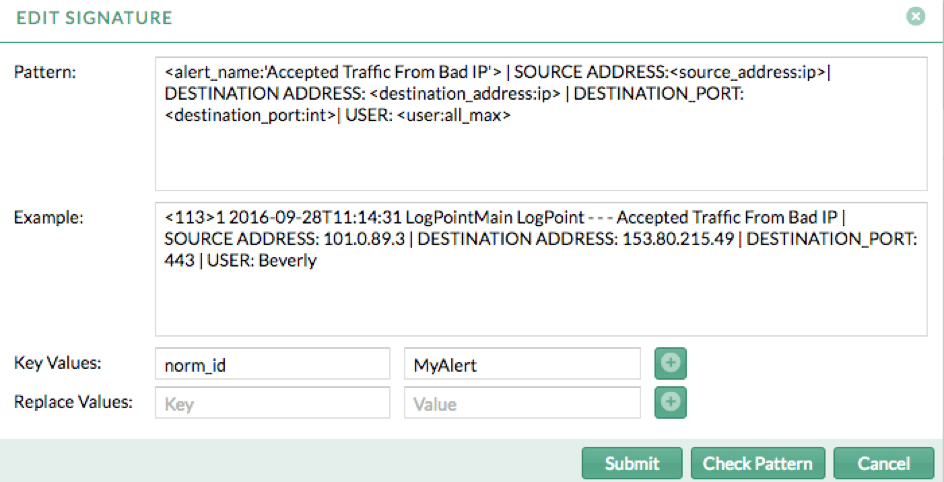
2. Erstellen Sie ein Normalisierungspaket
Jedes Mal, wenn die SIEM-Warnungen ausgelöst werden, wird ein neues Benachrichtigungsereignis empfangen, so dass wir dieses Ereignis normalisieren müssen.
Um dies zu erreichen, können wir die Jinja-Code-Syntax durch unsere für die Normalisierung verwendeten Definer ersetzen:
<alert_name:’Accepted Traffic From Bad IP’> | SOURCE ADDRESS:| DESTINATION ADDRESS: | DESTINATION_PORT: | BENUTZER:
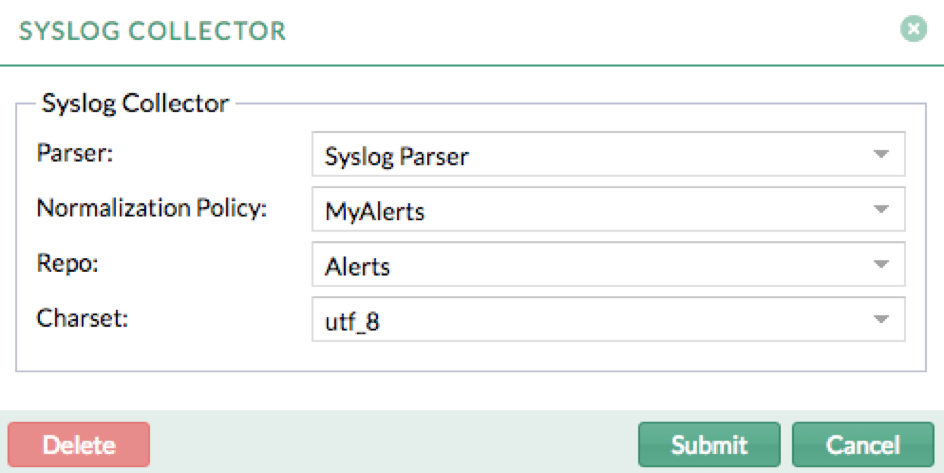
3. Erstellen Sie eine Normalisierungsrichtlinie: MyAlert
Sobald das Normalisierungspaket erstellt ist, müssen wir es in einer Normalisierungsrichtlinie anwenden.
4. Erstellen Sie ein neues Repo, in dem die Benachrichtigungen gespeichert werden.
In unserem Beispiel nennen wir es ‘Alerts’ und die Aufbewahrungsfrist wird entsprechend der Dauer festgelegt, die wir die Daten im System verfügbar halten möchten.
5. Wenden Sie die Normalisierungsrichtlinie auf localhost device / Syslog Collector an und wählen Sie ‘Alerts’ als Repo.
6. Jetzt werden Ihre Daten für jeden neuen Alarm normalisiert und in der Repo ‘Alerts’ gespeichert.
Von diesem Repo aus können Sie Folgendes tun:
- Analyse:
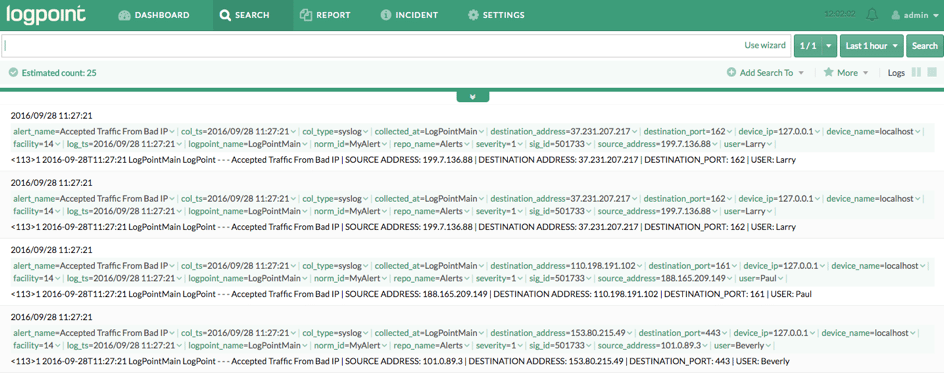
- Statistik:
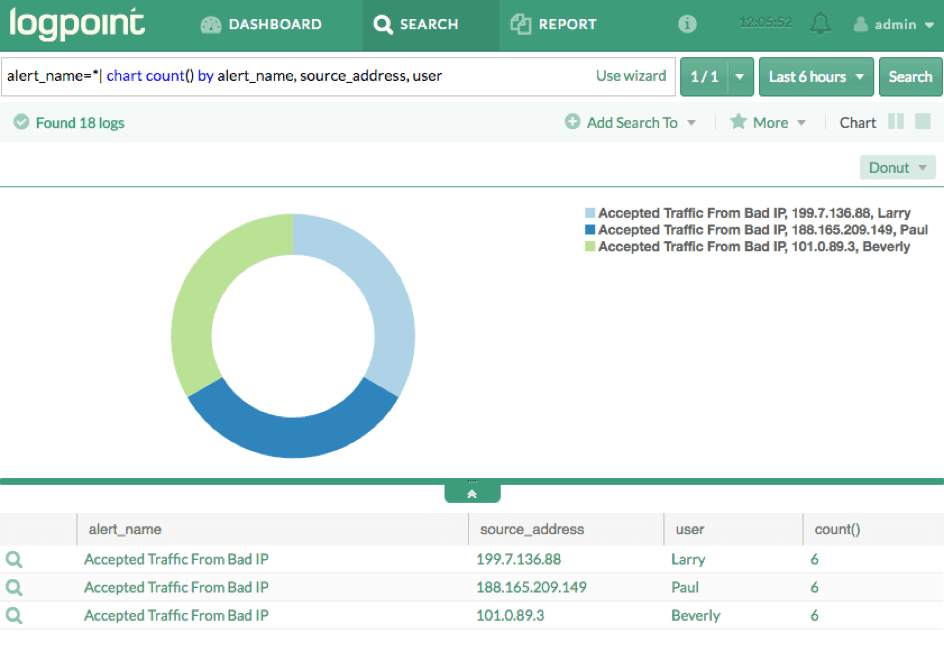
- Extrahieren Sie Ihre Liste im csv-Format:
| alarm_name,quelle_adresse,count() |
| Akzeptierter Verkehr von schlechter IP,101.0.89.3,6 |
| Akzeptierter Verkehr von schlechter IP,199.7.136.88,6 |
| Akzeptierter Verkehr von Bad IP,188.165.209.149,6 |
Dieses Tutorial zeigt die Leistungsfähigkeit und Konfigurierbarkeit von LogPoint.
Durch die Verwendung vorhandener Funktionen können wir die Anwendungen, den Umfang und die Funktionalität von LogPoint gründlich erweitern.
Wie nutzen Sie “Alarm-Feedback durch Syslog”, um langfristige Einblicke in Ihr Unternehmen zu erhalten?
Wenn Sie mehr darüber erfahren möchten, wie LogPoint funktioniert, buchen Sie eine persönliche Demo.






