Cybersécurité dans le secteur des services et de l’hôtellerie
Les menaces cybercriminelles pèsent de plus en plus sur de nombreuses organisations et entreprises. Le secteur des services et de l’hôtellerie n’est pas épargné. Ces menaces se sont développées avec les avancées et progrès majeurs réalisés dans l’industrie informatique, comme le Cloud Computing, les réseaux sociaux et le Big Data.

Gestion de la sécurité dans le secteur de l’hôtellerie
Assurer la sécurité des clients est une pratique standard dans le secteur hôtelier, mais l’accent a toujours été mis sur la propriété physique. Les clients comptent sur les hôtels pour assurer leur sécurité et celle de leurs biens pendant leurs séjours. Quand ils laissent des objets de valeur dans leur chambre, ils ferment juste la porte à clé ou bien utilisent le coffre-fort de la chambre, mais qu’en est-il de la cybersécurité dans le secteur de l’hôtellerie ?
Lire les avis de professionnels du secteur des Services sur Logpoint SIEM >
Changement de stratégie
Les clients supposent, à tort, que le même niveau de protection offert par les hôtels à leurs biens matériels s’étend aux actifs numériques, comme par exemple leurs ordinateurs portables et smartphones, lorsqu’ils utilisent les connexions Wi-Fi de l’établissement en question. Les hôtels doivent pouvoir offrir un niveau de sécurité permanent à leurs clients et à leurs biens, qu’ils soient matériels ou numériques, en mettant davantage l’accent sur la cybersécurité dans les lieux d’accueil.

Logpoint pour DAV
Avec Logpoint, DAV a :
- un stockage intégral, protégé contre les pannes et les altérations avec toutes les données de log prêtes à être auditées.
- réduit le nombre de faux positifs.
En fournissant des analyses complètes et des tableaux de bord ergonomiques, la solution Logpoint permet de garantir la conformité au RGPD.
En danger à plusieurs niveaux
Les services hôteliers doivent prévoir des systèmes endpoint multiples et des connexions à distance sur lesquelles s’appuyer pour gérer leurs opérations. Les verrous des portes électroniques, les contrôles CVC, les alarmes et toute une gamme d’objets connectés (IoT) peuvent tomber sous le contrôle de cybercriminels visant à perturber les activités courantes.
Le risque que les hôtels soient la cible de cybercriminels est encore plus élevé, car la plupart des personnes travaillant dans les services hôteliers qui s’occupent des systèmes informatiques (par exemple, les responsables de la réception et les comptables) ne sont pas des experts et n’ont qu’une certaine connaissance limitée des systèmes IT, rendant ainsi nécessaire l’amélioration de la cybersécurité dans le secteur de l’hôtellerie.
Menaces pour le secteur hôtelier
Menaces pour le secteur hôtelier
Les cybercriminels ont déjà fait de longs séjours dans les établissements hôteliers. Les hôtels et les restaurants sont parmi les principales cibles des cyberattaques dont sont victimes les services hôteliers et de restauration.
La plupart des violations de sécurité sont motivées financièrement. Elles sont organisées par des acteurs externes qui choisissent leurs cibles en fonction des opportunités et cherchent à compromettre les données des cartes bancaires.
L’utilisation d’identifiants volés est un autre type de violation de sécurité à laquelle le secteur des services est confronté. Ce dernier doit faire face à la fois à des acteurs externes mais aussi à l’abus de privilèges.
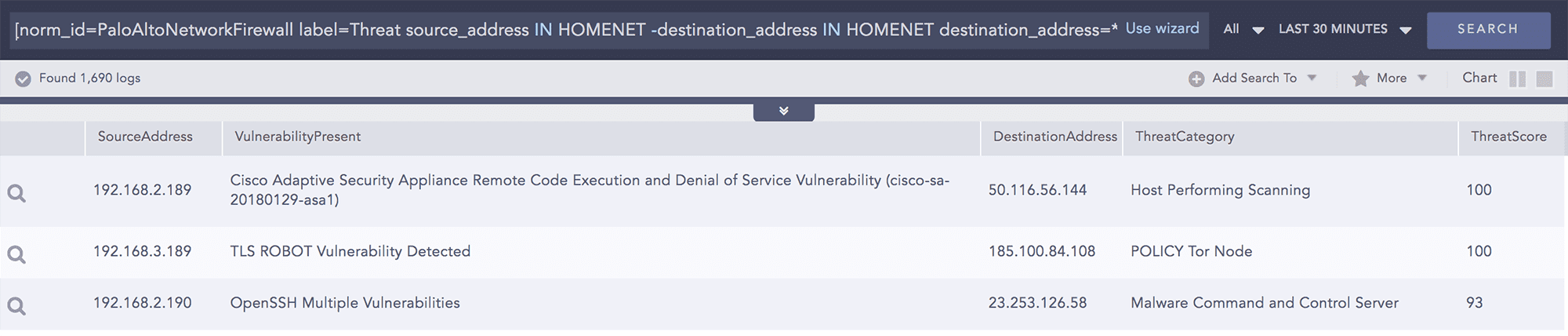
Garantir la sécurité du réseau
Logpoint s’intègre à une large gamme d’équipements réseau et de pare-feu. Les données provenant de ces équipements peuvent être normalisées, agrégées, enrichies et corrélées afin de garantir la sécurité au sein du réseau. De plus, les flux de renseignements sur les menaces (Threat Intelligence Feeds) peuvent être utilisés pour enrichir les données de log afin de comprendre si le réseau est ciblé par un acteur externe. Logpoint peut vérifier plusieurs activités telles que les connexions autorisées et refusées, l’utilisation des données et des applications, la connexion à une source malveillante ou toute autre activité suspecte.
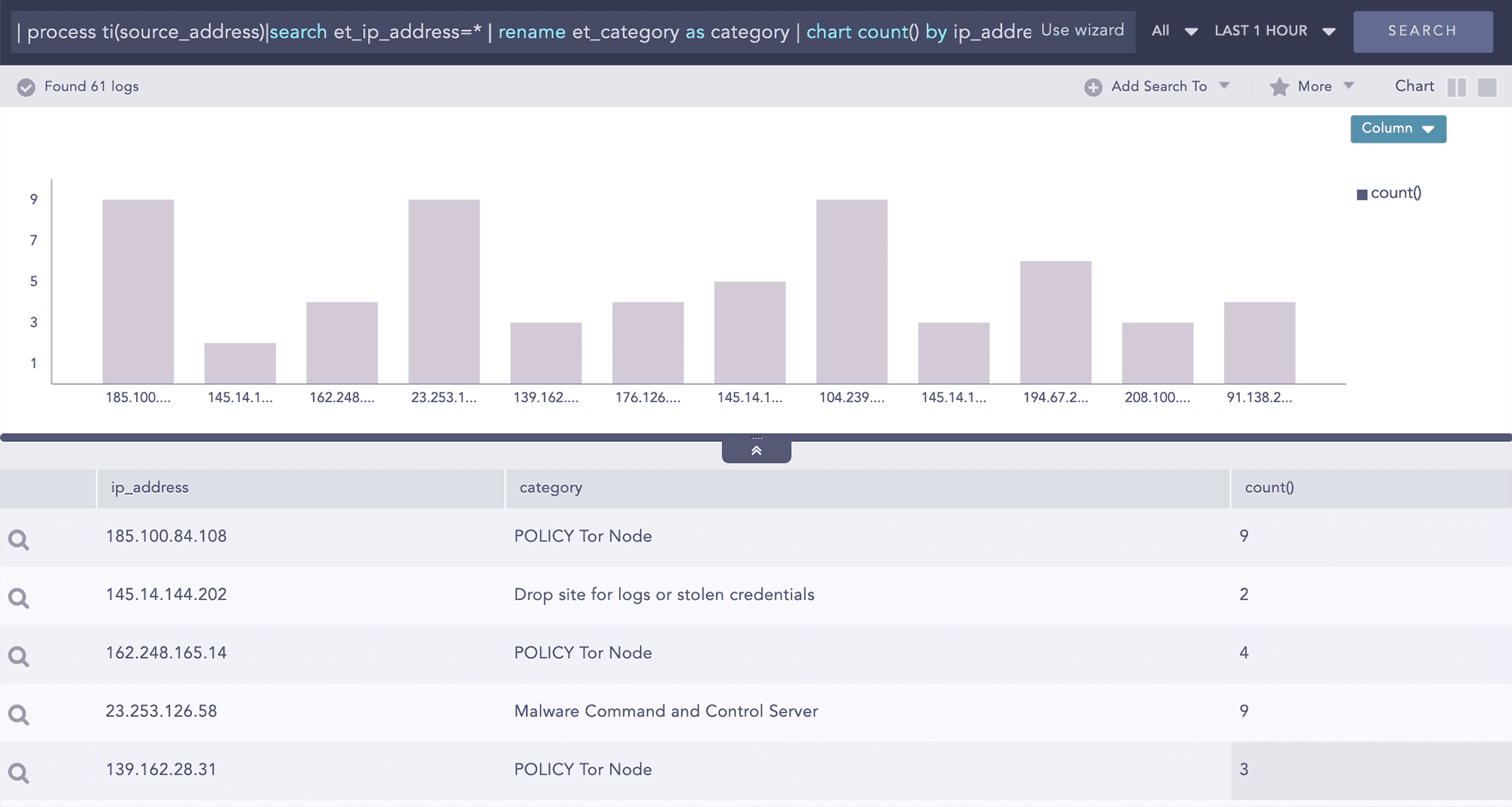
Identification des indicateurs de menace lors de l’utilisation d’importants volumes de logs
Les analystes peuvent utiliser des requêtes avec des commandes génériques pour obtenir des renseignements sur les menaces(Threat Intelligence) afin de filtrer uniquement les indicateurs de menace critiques. Avec Logpoint, le filtrage peut être générique, vous donnant ainsi toutes les correspondances au niveau de la base de données de renseignements sur les menaces ou bien il peut être basé sur certaines catégories de menace ou certains scores attribués aux menaces. Grâce à cette approche, nous permettons à vos analystes de simplifier le processus d’investigation afin que vous puissiez vous concentrer sur la menace réelle.