Quelle différence entre SIEM et EDR ? Cet article compare les solutions SIEM (Security Information and Event Management) et EDR (Endpoint Detection and Response) dans le domaine de la cybersécurité. Le SIEM centralise le stockage et l’analyse des données de diverses sources pour la détection, l’investigation et la réponse aux menaces, sans se limiter aux systèmes endpoint. L’EDR, en revanche, se concentre sur les endpoints pour détecter et répondre aux malwares et aux attaques complexes. Il est recommandé d’utiliser un SIEM en combinaison avec un EDR pour une défense multicouche efficace.

Définition d’une solution EDR
Traditionnellement, les logiciels de cybersécurité de base offrent une protection via des outils basés sur des signatures ou un SIEM. Une solution EDR (Endpoint Detection and Response) propose un logiciel complémentaire au SIEM utilisé pour étendre la capacité de détection et de réponse.
Un « endpoint » représente tout équipement qui est physiquement un « point de terminaison » au niveau du réseau. Il peut s'agir d'appareils sur site ou distants. Comme ils permettent d'accéder aux ressources ou aux applications d'une entreprise, la sécurité des « endpoints » est cruciale.
En particulier, un outil EDR détermine si un malware a été installé sur un système endpoint et trouve ensuite des moyens de répondre à ce type de menace. Une fois déployées, les solutions EDR utilisent des agents installés sur un endpoint pour collecter des données à partir de nombreuses sources de données différentes et ce directement au niveau de ce dernier en les stockant ensuite dans une base de données centrale.
Ces données proviennent généralement des sources suivantes :
- ARP
- DNS
- Sockets
- Registre
- Dumps mémoire
- Appels système
- Adresses IP
- Types de matériel
Une fois qu'une solution EDR localise une tentative de piratage ou une infiltration malveillante, elle fournit immédiatement une liste de réponses recommandées.
Tous les outils EDR fournissent des tableaux de bord ou des rapports, et une analyse des données est ensuite effectuée. Les solutions EDR prennent en charge à l’heure actuelle le système d'exploitation Windows et certains éditeurs proposent un support pour d'autres plateformes telles que macOS, Linux, Unix, iOS ou Android.
Définition d’une solution SIEM
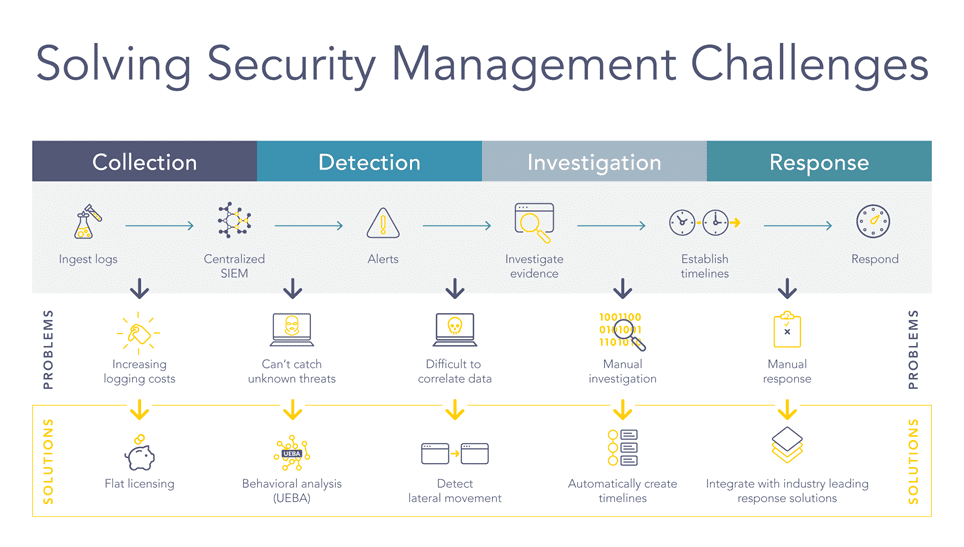
Une solution SIEM (Security Information and Event Management) est un outil centralisé de gestion des risques axé sur la détection, l'investigation et la réponse aux menaces.
Un outil SIEM est utilisé pour fournir un emplacement central unique pour le stockage et l'analyse des données, provenant de nombreuses sources de log différentes, sans se limiter aux systèmes endpoint. De cette façon, un SIEM fournit les moyens de connecter des silos d'informations auparavant séparés pour collecter des données et les analyser en temps réel, détecter les violations de données, stocker des données et créer des rapports. Ces capacités permettent ainsi de fournir une vue d’ensemble simple à comprendre et indépendante d’un point de vue des produits afin de pouvoir lancer des actions et apporter des réponses appropriées.
Etant donné que toutes les institutions sont en train d’achever leur processus de numérisation, les données sont désormais au cœur de tous les business model. Les données et la capacité de les visualiser représentent de manière intrinsèque une très grande valeur. De plus, cette valeur augmente considérablement lorsqu'elle est mise en contexte. Ces données, lorsqu’elles sont enrichies d'informations sur les utilisateurs, les ressources, les menaces et les vulnérabilités, deviennent alors exploitables et le SIEM qui les prend en charge augmente le ROI.
Avec un SIEM, il est possible d’appréhender de nombreux cas d'usage différents et de se connecter à de nombreux types de système accédant à différentes sources de log, tels que : les pare-feu, serveurs, IPS, proxys, etc. Etant donné qu’un SIEM prend en charge une multitude de plateformes différentes, il peut être utilisé pour la corrélation avancée, la gestion des logs et l’analyse post-mortem.
De plus, avec LogPoint SIEM, il n'y a aucune limite en ce qui concerne les cas d'usage. LogPoint est capable de gérer différents domaines tels que les opérations IT, la sécurité IT, la conformité et les Business Analytics.
LogPoint SIEM vous offre bien plus qu'un logiciel SIEM traditionnel.
Notre solution SIEM rassemble, investigue et enregistre efficacement les données d'événement produites par tout appareil ou application au sein de votre infrastructure, vous donnant ainsi les informations nécessaires pour définir l'étendue de la menace et prendre des décisions critiques.
Quelles sont les différences entre SIEM et EDR ?
Un outil SIEM peut être utilisé pour collecter des données à partir de nombreuses sources de données différentes et effectuer une corrélation avancée, une gestion des logs ou des analyses post-mortem. Ces données peuvent être générées par des applications, des bases de données, des infrastructures, des ressources sensibles, des systèmes de production ou de sécurité. Il n'y a aucune limite concernant les plateformes ou le type de cas d'usage pris en charge.
Un outil EDR permet d'investiguer, de découvrir, de prioriser et de remédier les attaques complexes, en particulier et uniquement, en utilisant des données de type endpoint.
Recommandations
Pour obtenir un système de défense multicouche et plus efficace, il est avantageux de combiner ces deux outils : à savoir utiliser la puissance du SIEM de LogPoint en collectant des données à partir de nombreuses sources de log différentes et en y ajoutant une solution EDR pour se focaliser davantage sur le réseau.
Comme un outil EDR ne fonctionne qu'avec des données de type endpoint, il est essentiel de considérer le SIEM comme fondamental et une solution EDR comme un complément idéal. Structurellement, un outil SIEM utilise ensuite une solution EDR comme une autre source de log lui fournissant de précieuses informations.