Se conformer à la directive NIS2 avec Logpoint
La directive NIS2 entre en vigueur et vise à renforcer la protection des infrastructures critiques de l’UE contre les cybermenaces. Elle introduit des exigences en matière de sécurité plus strictes, des obligations de déclaration et une nécessité de mise en œuvre pour un plus grand nombre de secteurs. L’incapacité à se conformer à la directive pourra entraîner des amendes allant jusqu’à 2 % du chiffre d’affaires global.
La conformité prend du temps et coûte cher
Les différents systèmes de votre environnement informatique génèrent des logs dans des formats et à des endroits différents, rendant ainsi coûteux et complexe le respect des exigences en matière de conformité. Pourtant, le coût de la non-conformitéest encore plus élevé. Les amendes, les frais juridiques et les atteintes à la réputation rendent la non-conformité presque 3x plus coûteuse que la conformité.
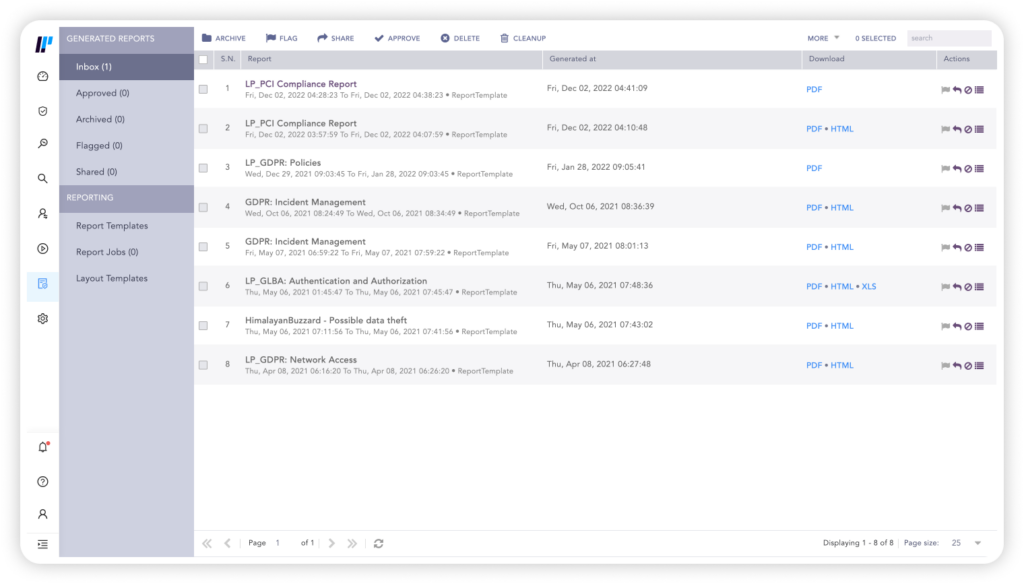
Simplification de la conformité avec une plateforme de sécurité centralisée et des rapports intégrés

Prouver la conformité
La prise en charge de tous les principaux domaines réglementaires permet de documenter et de prouver facilement la conformité.


Prise en charge prête à l’emploi de tous les principaux domaines réglementaires à un coût fixe qui n’augmente pas avec l’utilisation.
Détection et analyse automatisées pour assurer la conformité
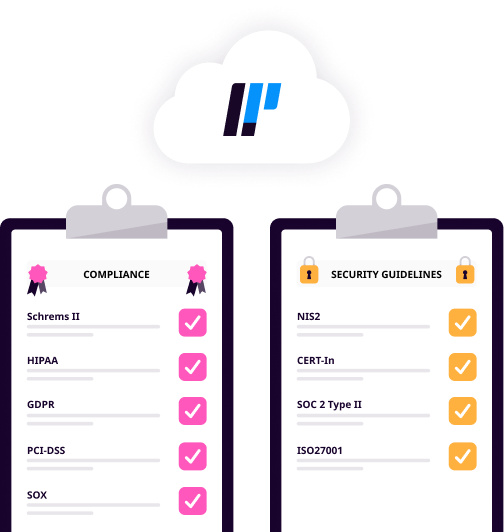
Logpoint assure la conformité à tous les principaux domaines réglementaires, notamment Schrems II, HIPAA, GDPR, PCI-DSS et SOX. Grâce à la journalisation et aux rapports centralisés, Logpoint facilite l’adhésion aux directives de sécurité, notamment NIS2, CERT-In, SOC 2 Type II et ISO27001.
Grâce à la plateforme convergente de Logpoint, vous pouvez également détecter et gérer les violations d’accès, les fuites de données et l’utilisation abusive de données sensibles dans les systèmes SAP essentiels à l’entreprise.
Améliorer la posture de sécurité au niveau de toute l’infrastructure
Logpoint collecte et analyse les données d’événements produites par tout dispositif, application ou système endpoint au sein de votre infrastructure et signale immédiatement les actions potentiellement non conformes.
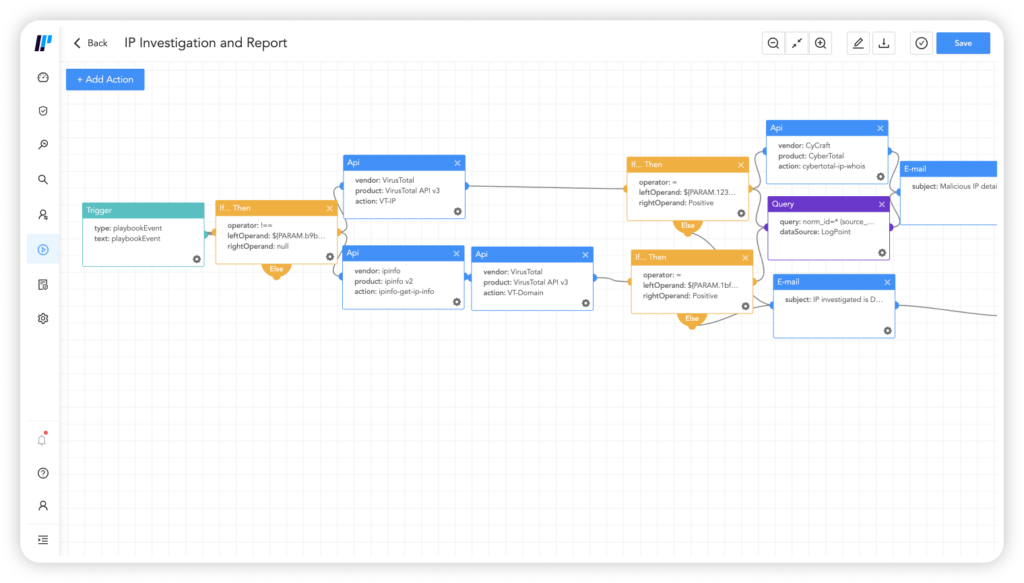
Avec les playbooks et les analyses au niveau de la plateforme centralisée, les comportements problématiques sont rapidement identifiés et une réponse appropriée est lancée.
Il est facile d’effectuer des analyses et des investigations post-mortem afin de pouvoir présenter des preuves de conformité et déterminer la cause profonde des violations.
Réduire les actions manuelles pour assurer la conformité
Automatisez la conformité grâce à des rapports prêts à l’emploi, des enregistrements d’audit de toutes les modifications apportées au système et des analyses historiques. Il est facile de créer et de partager des rapports d’incident complets. Créez également vos propres rapports personnalisés pour répondre aux exigences en matière de conformité réglementaire.
Notre système intégré de gestion des cas permet d’automatiser facilement l’investigation et la réponse à une violation de conformité et de créer des rapports pour documenter la mitigation de tout incident.

En résumé, Logpoint nous permet de documenter la conformité vis-à-vis d’une grande variété de normes et de renforcer la sécurité. La solution SIEM nous permet de fournir à nos clients de meilleurs services et une meilleure assistance.
En tant qu’entreprise du secteur des services financiers, il est impératif que nous maintenions en permanence une solide posture de sécurité. Nous sommes également confrontés à un large éventail de normes sectorielles telles que PCIDSS, RGPD, SOC 2 ainsi que le chiffrement point-à-point. En utilisant Logpoint, nous pouvons garder une vue très granulaire de nos logs et identifier facilement toute activité anormale.
Tenez-vous au courant de l’actualité
Le blog de Logpoint !