Logpoint for security analytics
Simple and fast security analytics implementation, user-friendly interface that can be integrated with an entire IT infrastructure.

Logpoint’s SIEM & SOAR products
Cybersecurity is challenged on several frontiers. With alert fatigue and a constant need for market adjustment, companies need solutions that reduce complexity and bring contextual awareness. Solutions that are easy to implement, integrate and operate. Logpoint is that solution.
Logpoint leverages advanced analytics, accelerated by Machine Learning to improve our customers’ cybersecurity and automate their digital transformation. Logpoint’s security analytics engine allows users to easily identify attacks, immediately respond and effectively report.
With Logpoint, our customers get a force multiplier for their security analysts to enhance the safety of critical business intelligence.
Product tour
The Logpoint SIEM & SOAR solution extracts events and incidents from the billions of logs existing in any IT infrastructure of any size for exhaustive security analytics.
We enable our customers to perform Orchestration, Automatization and Incident Response. Take a look at our product tour to explore which parts of Logpoint really stand out.
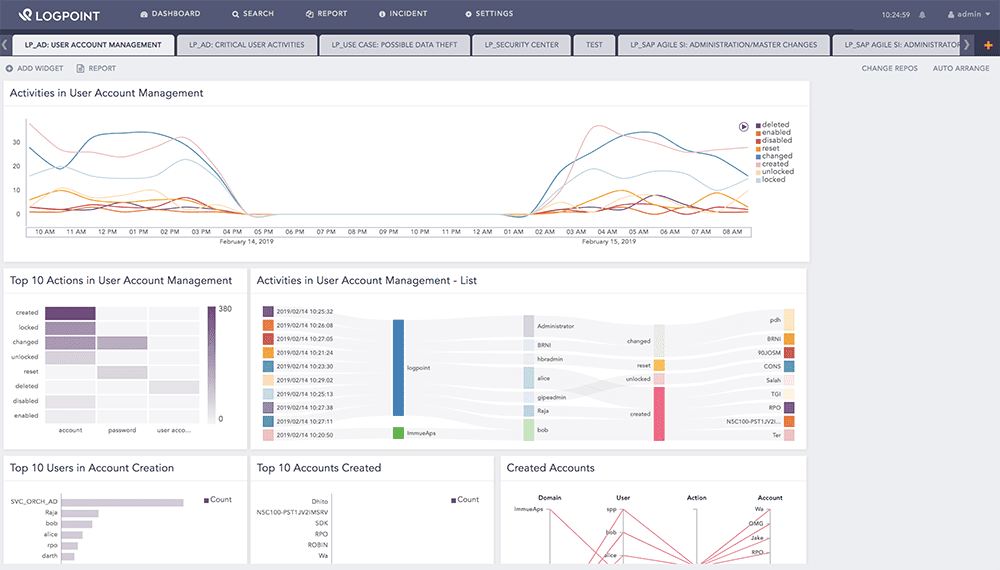
Logpoint as a SIEM & SOAR tool
A Security Information and Event Management (SIEM) solution is a central tool in the risk management toolkit.
A great SIEM & SOAR tool allows businesses to accelerate and improve threat detection and response by providing security analytics through real-time data analysis, early detection of data breaches, data collection, storage and accurate data reporting.
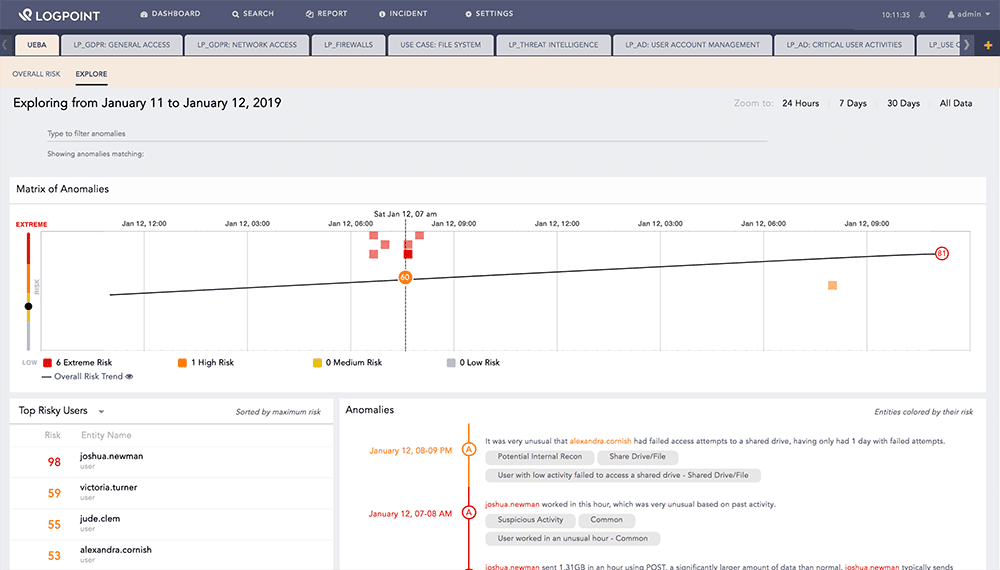
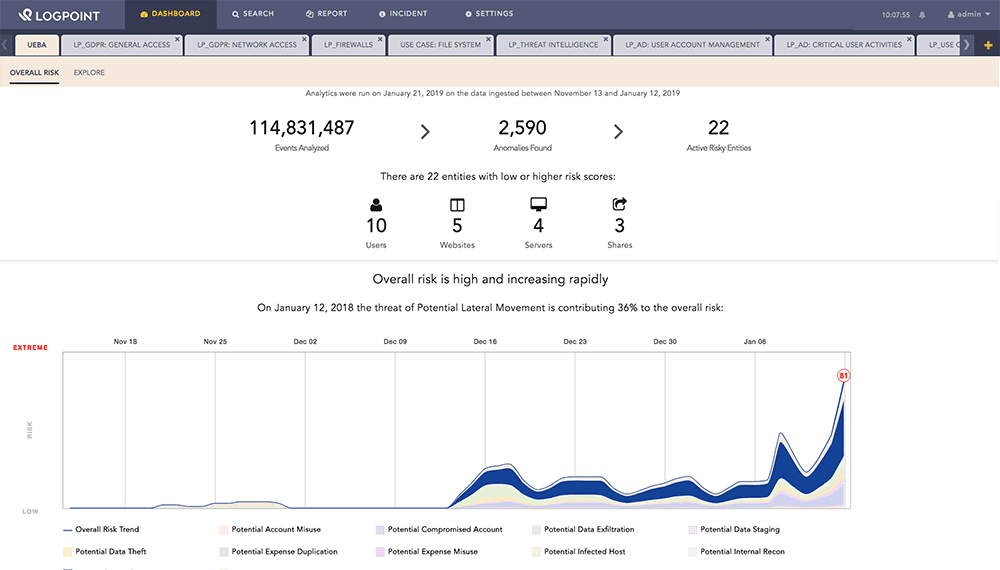
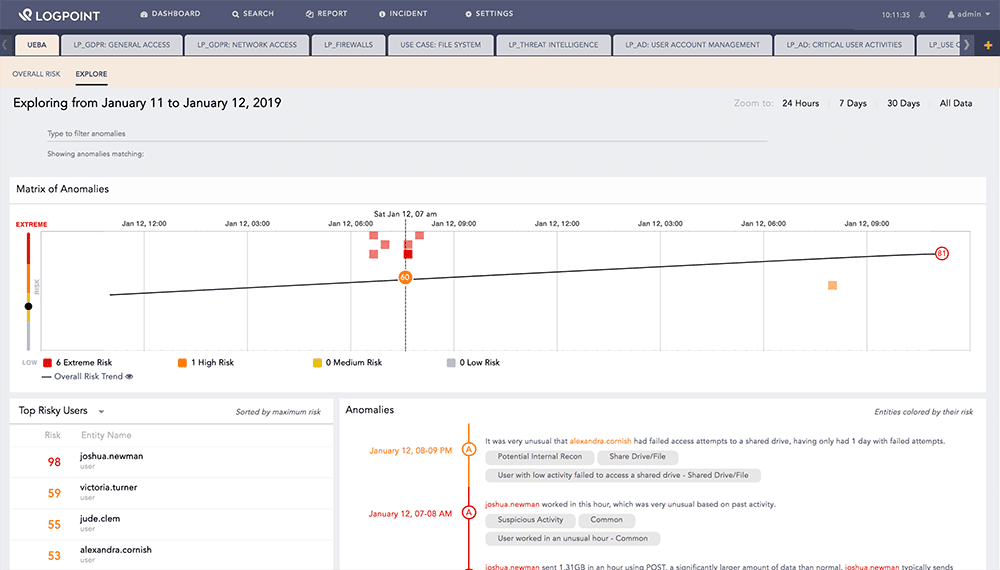
UEBA
Logpoint UEBA, based on advanced Machine Learning, analyzes the behavior of users and entities to find interesting or malicious behaviors and patterns within your infrastructure.
This feature makes your security team smarter by accelerating detection and response to threats without increasing the workload of your security analysts. UEBA makes your security and operations staff much more efficient and assists them in finding otherwise difficult to identify threats.
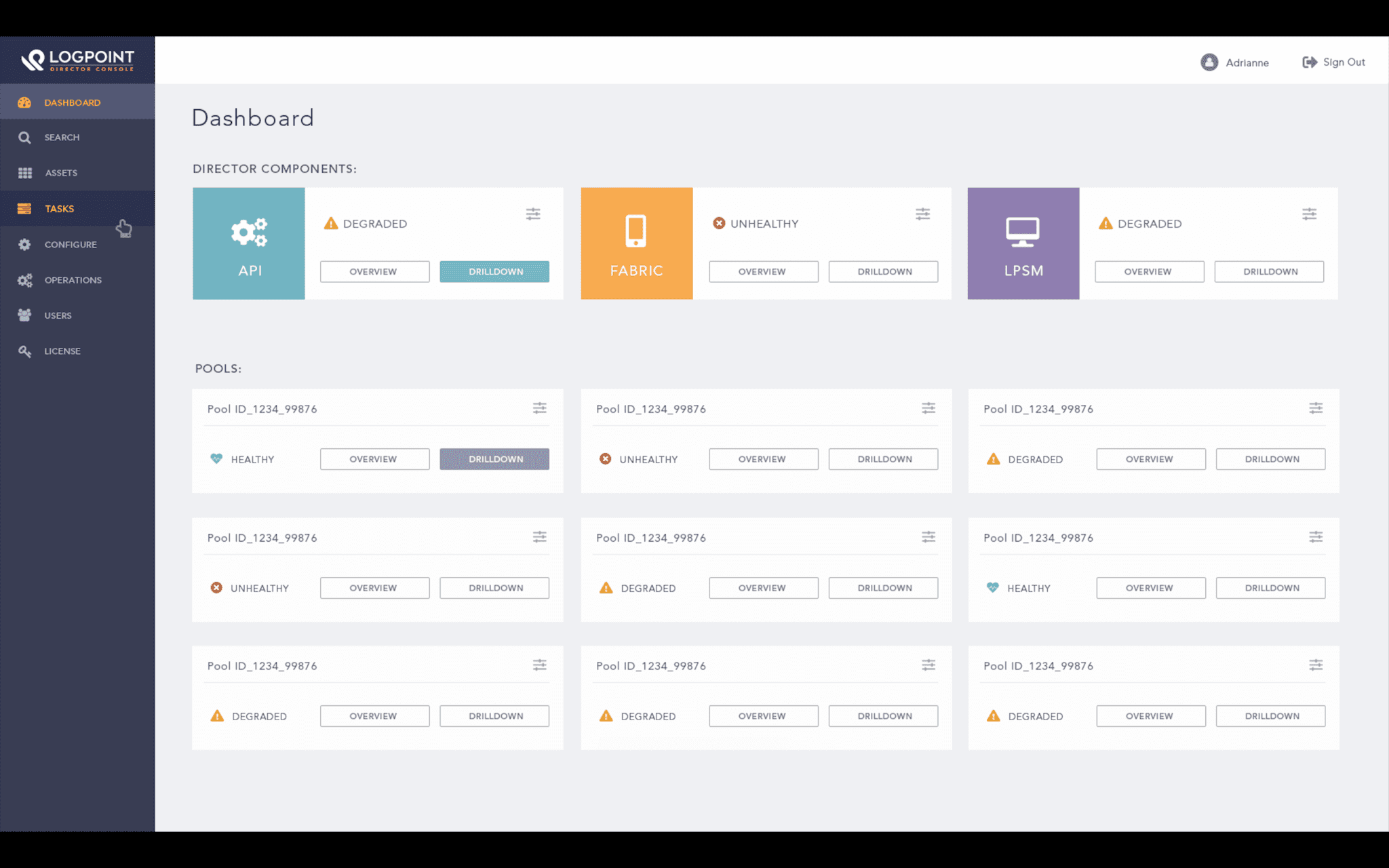
Director
With Director, you’ll be able to orchestrate and automate many cybersecurity tasks that would otherwise tie up your ops-team.
From a single pane of glass, the Director gives MSSPs and enterprises a tool to easily update, manage, operate, and monitor large multi-tenancy and single-instance SIEM & SOAR deployments.
SAP
Don’t underestimate the importance of combating security threats against your SAP environment through a SIEM and SOAR solution.
Threat Intelligence
Threat intelligence helps you comprehend risks related to the most common and severe external threats, such as zero-day threats, advanced persistent threats and exploits.